Cisco MDS-9124 Troubleshooting Guide - Page 456
Verifying Security Policy Databases Compatibility
 |
View all Cisco MDS-9124 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 456 highlights
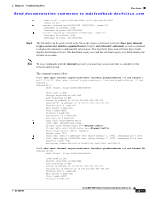
IPsec Issues Chapter 22 Troubleshooting IPsec Send documentation comments to [email protected] Step 6 Step 7 Ensure that the security association (SA) lifetime settings in the show crypto map domain ipsec command outputs are large enough to avoid excessive re-keys (the default settings ensure this). Ensure that the crypto map set is applied to the correct interface in the show crypto map domain ipsec command outputs for both switches. Verifying Security Policy Databases Compatibility To verify that the security policy databases (SPDs) are compatible on both switches, follow these steps: Step 1 Issue the show crypto spd domain ipsec command on both switches to display the SPD. The command outputs follow: MDSA# show crypto spd domain ipsec Policy Database for interface:GigabitEthernet7/1, direction:Both # 0: deny udp any port eq 500 any Clear test policies for IKE # 1: deny udp any any port eq 500 Clear test policies for IKE # 2: permit ip 10.10.100.231 255.255.255.255 10.10.100.232 255.255.255.255 # 127: deny ip any any Clear test policy for all other traffic Step 2 MDSC# show crypto spd domain ipsec Policy Database for interface:GigabitEthernet1/2, direction:Both # 0: deny udp any port eq 500 any # 1: deny udp any any port eq 500 # 2: permit ip 10.10.100.232 255.255.255.255 10.10.100.231 255.255.255.255 # 127: deny ip any any Issue the show ipsec internal crypto-accelerator interface gigabitethernet slot/port spd inbound command on both switches to display SPD information from the crypto-accelerator. Note To issue commands with the internal keyword, you must have an account that is a member of the network-admin group. The example command outputs follow: MDSA# show ipsec internal crypto-accelerator interface gigabitethernet 7/1 spd inbound Inbound Policy 0 : Source IP Address :* Destination IP Address :* Source port :500, Destination port :* Protocol UDP Physical port:0/0, Vlan_id:0/0 Action cleartext Inbound Policy 1 : Source IP Address :* Destination IP Address :* Source port :*, Destination port :500 Protocol UDP Physical port:0/0, Vlan_id:0/0 Action cleartext Inbound Policy 2 : Source IP Address :10.10.100.232/255.255.255.255 Destination IP Address :10.10.100.231/255.255.255.255 Source port :*, Destination port :* Protocol * Physical port:0/1, Vlan_id:0/4095 22-8 Cisco MDS 9000 Family Troubleshooting Guide, Release 3.x OL-9285-05