D-Link DES-3828 Product Manual - Page 149
create access_profile, create, create access_profile ip source_ip_mask 255.255.255.0 profile_id 1
 |
UPC - 790069276811
View all D-Link DES-3828 manuals
Add to My Manuals
Save this manual to your list of manuals |
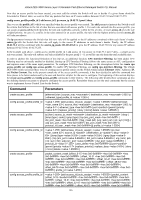
Page 149 highlights
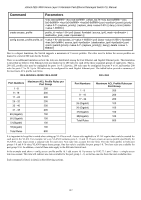
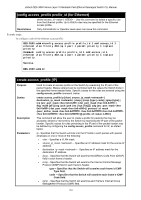
xStack DES-3800 Series Layer 3 Stackable Fast Ethernet Managed Switch CLI Manual Command delete cpu access_profile Parameters 0x0-0xffffffff> | {offset 32-47 | {offset 4863 | {offset 64-79 }] [profile_id ] profile_id config cpu access_profile profile_id enable cpu interface_filtering disable cpu_interface_filtering show cpu_interface_filtering show cpu access_profile [add access_id [ethernet {vlan | source_mac | destination_mac | ethernet_type } [permit | deny] | ip {vlan | source_ip | destination_ip | dscp | [icmp {type code } | igmp {type } | tcp {src_port | dst_port | {urg | ack | psh | rst | syn | fin}]} | udp {src_port | dst_port } | protocol_id {user_define }]} [permit | deny] | packet_content {offset_0-15 | offset_16-31 | offset_32-47 | offset_48-63 | offset_64-79 } [permit | deny] | delete access_id ] {profile_id {access_id }} Access profiles allow you to establish criteria to determine whether or not the Switch will forward packets based on the information contained in each packet's header. These criteria can be specified on a VLAN-by-VLAN basis. Creating an access profile is divided into two basic parts. First, an access profile must be created using the create access_profile command. For example, if you want to deny all traffic to the subnet 10.42.73.0 to 10.42.73.255, you must first create an access profile that instructs the Switch to examine all of the relevant fields of each frame: create access_profile ip source_ip_mask 255.255.255.0 profile_id 1 Here we have created an access profile that will examine the IP field of each frame received by the Switch. Each source IP address the Switch finds will be combined with the source_ip_mask with a logical AND operation. The profile_id parameter is used to give the access profile an identifying number − in this case, 1. The deny parameter instructs the Switch to filter any frames that meet the criteria − in this case, when a logical AND operation between an IP address specified in the next step and the ip_source_mask match. The default for an access profile on the Switch is to permit traffic flow. If you want to restrict traffic, you must use the deny parameter. 145