D-Link DFL-260 Product Manual - Page 346
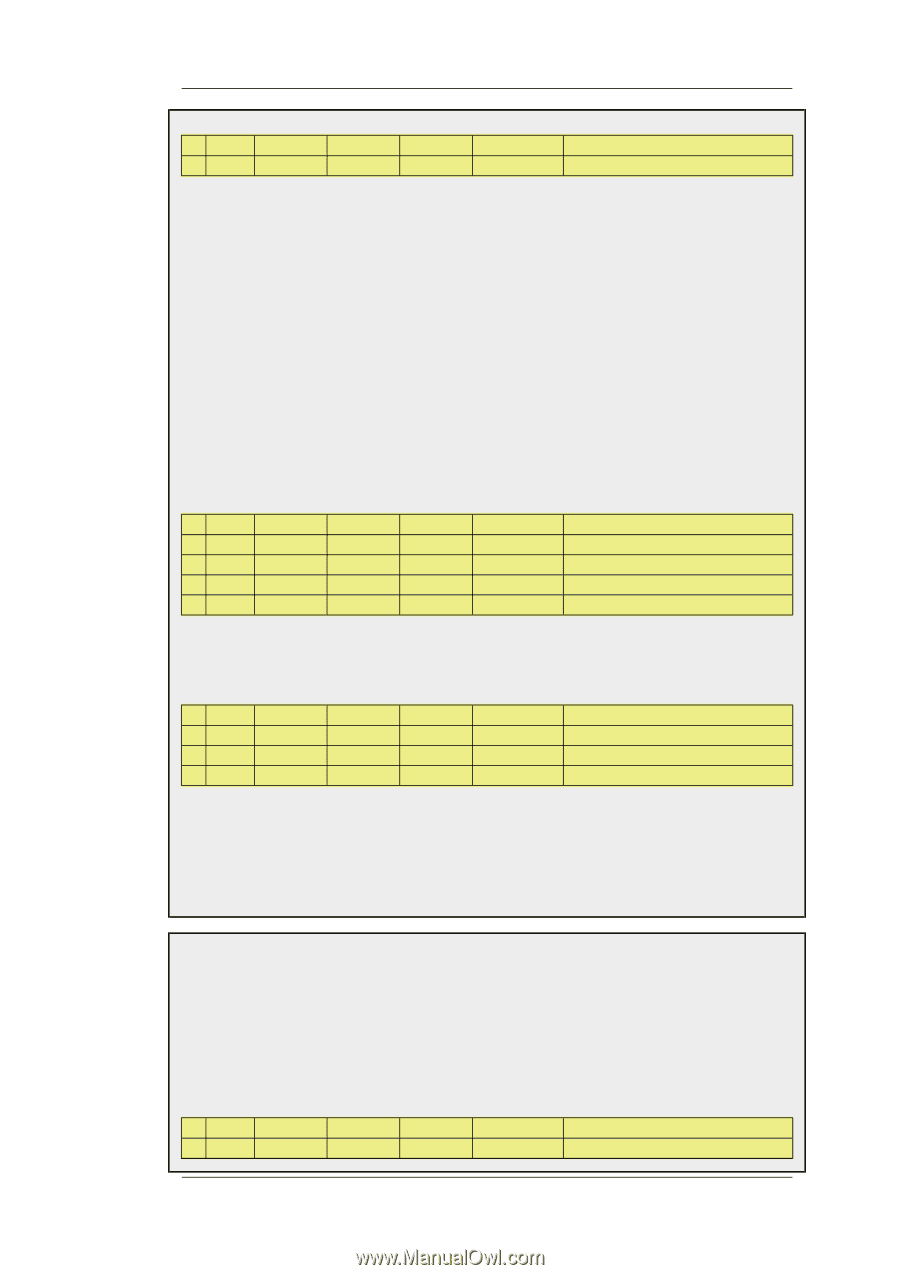
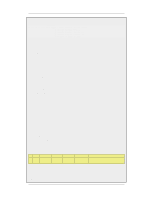
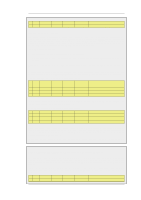
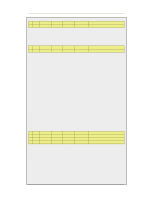
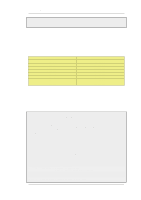
Example 7.4. Enabling Traffic to a Web Server on an Internal Network, Action, Src Iface, Src Net
 |
UPC - 790069296802
View all D-Link DFL-260 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 346 highlights
7.4.1. Translation of a Single IP Address (1:1) Chapter 7. Address Translation # Action Src Iface 3 NAT lan Src Net lannet Dest Iface any Dest Net all-nets Parameters All Now, what is wrong with this rule set? If we assume that we want to implement address translation for reasons of security as well as functionality, we discover that this rule set makes our internal addresses visible to machines in the DMZ. When internal machines connect to wan_ip port 80, they will be allowed to proceed by rule 2 as it matches that communication. From an internal perspective, all machines in the DMZ should be regarded as any other Internet-connected servers; we do not trust them, which is the reason for locating them in a DMZ in the first place. There are two possible solutions: 1. You can change rule 2 so that it only applies to external traffic. 2. You can swap rules 2 and 3 so that the NAT rule is carried out for internal traffic before the Allow rule matches. Which of these two options is the best? For this configuration, it makes no difference. Both solutions work just as well. However, suppose that we use another interface, ext2, in the NetDefend Firewall and connect it to another network, perhaps to that of a neighboring company so that they can communicate much faster with our servers. If option 1 was selected, the rule set must be adjusted like this: # Action 1 SAT 2 Allow 3 Allow 4 NAT Src Iface any wan ext2 lan Src Net all-nets all-nets ext2net lannet Dest Iface core core core any Dest Net wan_ip wan_ip wan_ip all-nets Parameters http SETDEST 10.10.10.5 80 http http All This increases the number of rules for each interface allowed to communicate with the web server. However, the rule ordering is unimportant, which may help avoid errors. If option 2 was selected, the rule set must be adjusted like this: # Action 1 SAT 2 NAT 3 Allow Src Iface any lan any Src Net all-nets lannet all-nets Dest Iface core any core Dest Net wan_ip all-nets wan_ip Parameters http SETDEST 10.10.10.5 80 All http This means that the number of rules does not need to be increased. This is good as long as all interfaces can be trusted to communicate with the web server. If, however, at a later point we add an interface that cannot be trusted to communicate with the web server, separate Drop rules would have to be placed before the rule granting all machines access to the web server. Determining the best course of action must be done on a case-by-case basis, taking all circumstances into account. Example 7.4. Enabling Traffic to a Web Server on an Internal Network The example we have decided to use is that of a web server with a private address located on an internal network. From a security standpoint, this approach is wrong, as web servers are very vulnerable to attack and should therefore be located in a DMZ. However, due to its simplicity, we have chosen to use this model in our example. In order for external users to access the web server, they must be able to contact it using a public address. In this example, we have chosen to translate port 80 on the NetDefend Firewall's external address to port 80 on the web server: # Action Src Iface 1 SAT any Src Net all-nets Dest Iface core Dest Net wan_ip Parameters http SETDEST wwwsrv 80 346