D-Link DFL-260 Product Manual - Page 369
A Group Usage Example, 8.2.8. HTTP Authentication, Changing the Management WebUI Port
 |
UPC - 790069296802
View all D-Link DFL-260 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 369 highlights
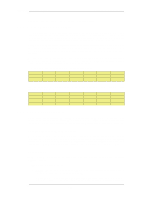
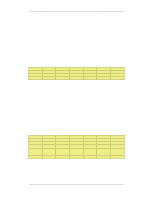
8.2.7. A Group Usage Example Chapter 8. User Authentication Any packets from an IP address that fails authentication are discarded. 8.2.7. A Group Usage Example To illustrate Authentication Group usage, lets suppose that there are a set of users which will login from a network 192.168.1.0/24 connected to the lan interface. The requirement is to restrict access to a network called important_net on the int interface to one group of trusted users, while the other less-trusted users can only access another network called regular_net on the dmz interface. Assuming we using the internal database of users as the authentication source, we add the users to this database with appropriate username/password pairs and a specific Group string. One set of users would be assigned to the group with the name trusted and the other to the group with the name untrusted. We now define two IP objects for the same network 192.168.1.0/24. One IP object is called untrusted_net and has its Group parameter set to the string untrusted. The other IP object is called trusted_net and its Group parameter is set to the string untrusted. The final step is to set up the rules in the IP rule set as shown below: # Action Src Interface Src Network Dest Interface Dest Network Service 1 Allow lan trusted_net int important_net All 2 Allow lan untrusted_net dmz regular_net All If we wanted to allow the trusted group users to also be able to access the regular network we could add a third rule to permit this: # Action Src Interface Src Network Dest Interface Dest Network Service 1 Allow lan trusted_net int important_net All 2 Allow lan trusted_net dmz regular_net All 3 Allow int untrusted_net dmz regular_net All 8.2.8. HTTP Authentication Where users are communicating through a web browser using the HTTP protocol then authentication can be done by presenting the user with HTML pages to retrieve required user information. This is sometimes referred to as WebAuth and the setup requires further considerations. Changing the Management WebUI Port HTTP authentication will collide with the WebUI's remote management service which also uses TCP port 80. To avoid this, the WebUI port number should be changed before configuring authentication. Do this by going to Remote Management > advanced settings in the WebUI and changing the setting WebUI HTTP Port. Port number 81 could instead, be used for this setting. Agent Options For HTTP and HTTPS authentication there is a set of options in Authentication Rules called Agent Options. These are: • Login Type - This can be one of: i. FORM - The user is presented with an HTML page for authentication which is filled in and the data sent back to NetDefendOS with a POST. ii. BASICAUTH - This sends a 401 - Authentication Required message back to the browser which will cause it to use its own inbuilt dialog to ask the user for a username/password 369