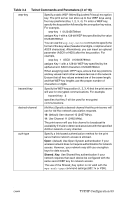
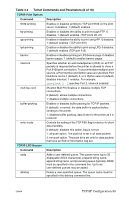
HP 4200n HP Jetdirect Print Servers - Administrator Guide - Page 85
Table 3.4, Telnet Commands and Parameters 5 of 18, TCP/IP Configuration 85
 |
UPC - 808736313971
View all HP 4200n manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 85 highlights
Table 3.4 Telnet Commands and Parameters (5 of 18) svr-auth-pass Specify a password for server-based authentication. Up to 128 alphanumeric characters may be used. svr-auth-id Specify the CA certificate character string that will be used to identify and validate the authentication server. This string will be compared to an identification string received from the authentication server. For string comparison, you can specify whether an exact match is required: RIGHT_MOST (default): The string entry will be compared to the right-most characters in the CA certificate string. USE_EXACT: The string entry must exactly match the authentication server's string. wpa-auth-type This command is not compatible with the Shared Key authentication option in the auth-type command. Use this command to specify a supported EAP authentication type: 802.1x: Select this option on an EAP network that uses an authentication server. Use the server-auth command to specify the EAP/802.1x protocols used on your network. Use the dynamic-encrypt command to specify a dynamic encryption option. PSK: Select this option on EAP networks where an authentication server is not used. Instead, a Pre-shared key provides device authentication. A Pre-shared key is generated when you specify a network pass-phrase using the psk-passphrase command. The dynamic-encrypt command should be set to the Robust option. psk-passphrase Specify a pass-phrase that is used to generate a network Pre-shared key. A pass-phrase must be from 8 to 63 ASCII characters in the hexadecimal range 21 through 7E (characters 0-9, a-z, A-Z and numerous special characters including dynamic-encrypt Select a supported dynamic encryption option: Basic: Dynamic WEP encryption is supported. Robust: Dynamic Wi-Fi Protected Access (WPA) and WEP encryption protocols are supported. Use the wpa-auth-type command to select a compatible EAP authentication type: G For EAP/PSK authentication, the print server should use Robust encryption (WPA encryption protocols). G For EAP/802.1x authentication (LEAP only), the print server should use Basic encryption. G For EAP/802.1x authentication (PEAP, TLS, TTLS only), the print server may use either Basic encryption or Robust encryption depending on your network. Dynamic encryption protocols are under the control of the authentication server and also must be supported by the Access Point. ENWW TCP/IP Configuration 85