HP Jetdirect J2550A HP Jetdirect Security Guidelines
HP Jetdirect J2550A Manual
 |
View all HP Jetdirect J2550A manuals
Add to My Manuals
Save this manual to your list of manuals |
HP Jetdirect J2550A manual content summary:
- HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 1
HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 2
unboxing them, powering them up, getting a configuration page to find the IP address, adding them to your desktop computer system or printer spooler, and then forgetting about them. Does that last part sound like your printing and imaging security strategy? One of the challenges HP Jetdirect has in - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 3
printing infrastructure. Secondly, we can also understand what HP Jetdirect cannot do. As an example, some information on the Internet conveys that the PJL parser is implemented on HP Jetdirect. Based upon this diagram, we know that is false. Upgrading your HP Jetdirect card to provide your printer - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 4
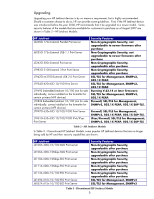
MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 5
be upgraded to a newer model. Some security features of the models that are available for customers to purchase as of August 2007 are shown in Table 2 - HP Jetdirect Models: HP Jetdirect J3258G 170x External Parallel Print server J6035G 175x External USB 1.1 Print Server J3263G 300x External Print - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 6
As you can see, replacing a discontinued 400n MIO model with a new external parallel port print server like the 300X will not upgrade the security capabilities of the Jetdirect device. Printers that have an MIO slot like the LaserJet IIIsi and LaserJet 4si have been discontinued for many years. - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 7
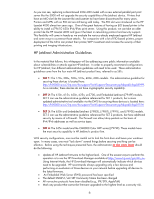
Print Server Firmware Version V.33.14/V.33.15 K.08.49 K.08.49 G.08.49 G.08.49 G.08.49 L.25.57 R.25.57 H.08.60 J.08.60 J.08.60 V.28.22 V.29.20 V.29.29 V.36.11 Table 4 - Jetdirect Firmware Versions NOTE: For some Embedded Jetdirect products, you'll need to upgrade the printer/MFP firmware to update - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 8
to 0.0.0.0). This doesn't prevent HP Jetdirect from receiving packets from other subnets, but does prevent the responses from returning to those remote subnets. As a result, TCP connections cannot be formed. Option 2) For SET 1/2/3/4. Setup an access control list with the IP address and mask for the - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 9
can populate the firmware upgrade MIB table with TFTP server information. HP Jetdirect uses this information to start a TFTP client and pull down the download file. These applications use the well-known default SNMP community names. However, if an administrator has configured the SNMP SET community - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 10
interface directly with the printer/MFP's PJL library over a print connection. These tools often claim to bypass HP Jetdirect security. However, as we've seen from our functional diagram, HP Jetdirect controls the networking stack and does not parse PJL and cannot be configured to block PJL commands - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 11
with UNIX or Linux environments; however, there are many free BOOTP and TFTP servers for Windows and setup is fairly easy. An example UNIX configuration will be provided here. picasso:\ :hn:\ :ht=ether:\ :vm=rfc1048:\ :ha=0001E6123456:\ :ip=192.168.40.39:\ :sm=255.255.255.0:\ :gw=192.168.40.1:\ :lg - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 12
". This file is sent to the printer on power-up. Here is a sample content for the pjlprotection file: %-12345X@PJL @PJL COMMENT **Set Password** @PJL COMMENT **& Lock Control Panel** @PJL JOB PASSWORD = 7654 @PJL DEFAULT PASSWORD = 1776 @PJL DINQUIRE - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 13
First and foremost, set a password. 13 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 14
Change the Encryption Strength to "Medium" and check the "Encrypt All Web Communication " checkbox. This checkbox forces HTTPS to be used for all web communication. Uncheck "Enable Telnet and FTP Firmware Update" and "Enable RCFG". 14 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 15
Uncheck "Enable SNMPv1/v2" and check Enable "SNMPv3". Provide SNMPv3 parameters. 15 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 16
Based upon the customer's environment, read only SNMPv1/v2c access may need to be granted. Some tools such as the HP Standard Port Monitor use SNMPv1/v2c for status. Setup an Access Control List entry. This is another customer environment specific entry. In this example, the subnet 192.168.1.0 is - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 17
and services. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is required. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. For now, this configuration step - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 18
Deployments: SET 3 First and foremost, SET 3 configuration needs to have the Security Wizard for SET 2 executed. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. A sample Firewall configuration is shown where the management protocols are - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 19
Be sure that you are using HTTPS before navigating to this page. Select the drop down box for the Default Rule to be "Allow" and then click "Add Rules..." We have a specific administrator subnet defined for printing and imaging devices. Click the "New" button so we can be very specific about what - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 20
192.168.0/24 subnet for the Remote Address. We've also named this address template very clearly. Now for IPv6. Click "New" again. NOTE: If IPv6 is not used on your network, go to TCP/IP settings and disable IPv6 for increased security. You can also skips which use IPv6 in this configuration. 20 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 21
Select the appropriate IPv6 addresses and name the address template. Now that we have the address templates, let's create a rule. Rules are processed in priority order from 1 - 10. Let's create an IPv4 rule first. Select the IPv4 address template you created, then click "Next". 21 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 22
We are concerned with management services, so select the service template "All Jetdirect Management Services". Click "Next". Select "Allow Traffic". Click "Next" 22 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 23
Select "Create another rule". Select the IPv6 address template you created and then click "Next". 23 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 24
Select the "All Jetdirect Management Services" service template. Click "Next". Select "Allow Traffic". Click Next. 24 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 25
We have allowed management traffic from our IPv4/IPv6 administrative subnet. Now we must create a rule to throw away all other management traffic. Click "Create another rule". Here we select "All IP addresses" which encompasses both IPv4 and IPv6. Click "Next". 25 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 26
Again, select "All Jetdirect Management Services" for the service template and then click "Next". Select "Drop". Click "Next". 26 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 27
Otherwise, if it is a management service, it will be dropped. All other traffic will be allowed (the default rule is allow). Click "Finish". Select "Yes" for Enable Policy. HTTPS failsafe can be used when trying out configurations. If this is your first firewall configuration, you may want to enable - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 28
can begin the IPsec configuration. Let's go through the same process as we did with SET 3, only this time, we'll simply say that all IP addresses must use IPsec to utilize a management protocol. If an end station tries to communicate with a management protocol to Jetdirect without using IPsec, the - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 29
Select "All Jetdirect Management Services". Click "Next". Select "Require traffic to be protected with an IPsec/Firewall Policy". Click "Next". 29 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 30
Click "New". Name the IPsec Template. Some Jetdirect models may require you to configure IKE parameters. However, this model has a quick set of IKE defaults that can be used. The one selected is for more emphasis on Interoperability and less on Security. Click "Next". 30 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 31
For example purposes only, Pre-Shared Key Authentication is used. HP does not recommend using PreShared Key Authentication. Certificates or Kerberos is highly recommended. Click "Next". Select the IPsec template you just created. Click "Next". 31 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 32
Here is our IPsec policy. If a management protocol is to be used, it must use IPsec. All other traffic is allowed based upon the default rule. Click "Finish". Select "Yes" to enable the IPsec policy. You can also choose to have a failsafe if you would like. Click "OK". 32 - HP Jetdirect J2550A | HP Jetdirect Security Guidelines - Page 33
/c00731218.pdf IPsec: http://h20000.www2.hp.com/bc/docs/support/SupportManual/c01048192/c01048192.pdf IPv6: http://h20000.www2.hp.com/bc/docs/support/SupportManual/c00840100/c00840100.pdf Using the networking infrastructure to better protect your printing and imaging devices: http://h20000.www2
HP Jetdirect Security Guidelines
whitepaper
Table of Contents:
Introduction
.....................................................................................................................................
1
HP Jetdirect Overview
......................................................................................................................
2
What is an HP Jetdirect?
...................................................................................................................
3
How old is Your HP Jetdirect?
............................................................................................................
4
Upgrading
......................................................................................................................................
5
HP Jetdirect Administrative Guidelines
................................................................................................
6
HP Jetdirect Hacks: TCP Port 9100
.....................................................................................................
7
HP Jetdirect Hacks: Password and SNMP Community Names
................................................................
9
HP Jetdirect Hacks: Firmware Upgrade
...............................................................................................
9
HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them
.................................................................
10
HP Jetdirect Hacks: Printer/MFP access
............................................................................................
10
Recommended Security Deployments: SET 1
......................................................................................
11
Recommended Security Deployments: SET 2
......................................................................................
12
Recommended Security Deployments: SET 3
......................................................................................
18
Recommended Security Deployments: SET 4
......................................................................................
28
Further Reading
.............................................................................................................................
33
Introduction
The availability of public information on the Internet for hacking HP Jetdirect products has prompted
customers to ask HP about how they can protect their printing and imaging devices against such
attacks and what is HP doing about preventing those attacks.
In all fairness, some of this public
information is of rather poor quality and inflammatory; however, some websites detailing the attacks
and the vulnerabilities on HP Jetdirect are informative and raise valid concerns that need to be
addressed.
It is the purpose of this whitepaper to address customer concerns about these attacks and
vulnerabilities and to recommend proper security configurations to help customers protect their
printing and imaging devices.
This whitepaper is only a small part of a broad initiative within HP to
educate our customer base about printing and imaging security.
Resources such as The Secure
Printing website (
) provide a great deal of information for
customers about products, solutions, as well as configuration recommendations. In general, a lot of
this information can be put to use on existing HP Jetdirect products, mainly because HP Jetdirect was
1