HP Mini 110-4100 HP Notebook Reference Guide - Windows 7 - Page 15
Protecting your WLAN, Firewall, Wireless encryption
 |
View all HP Mini 110-4100 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 15 highlights
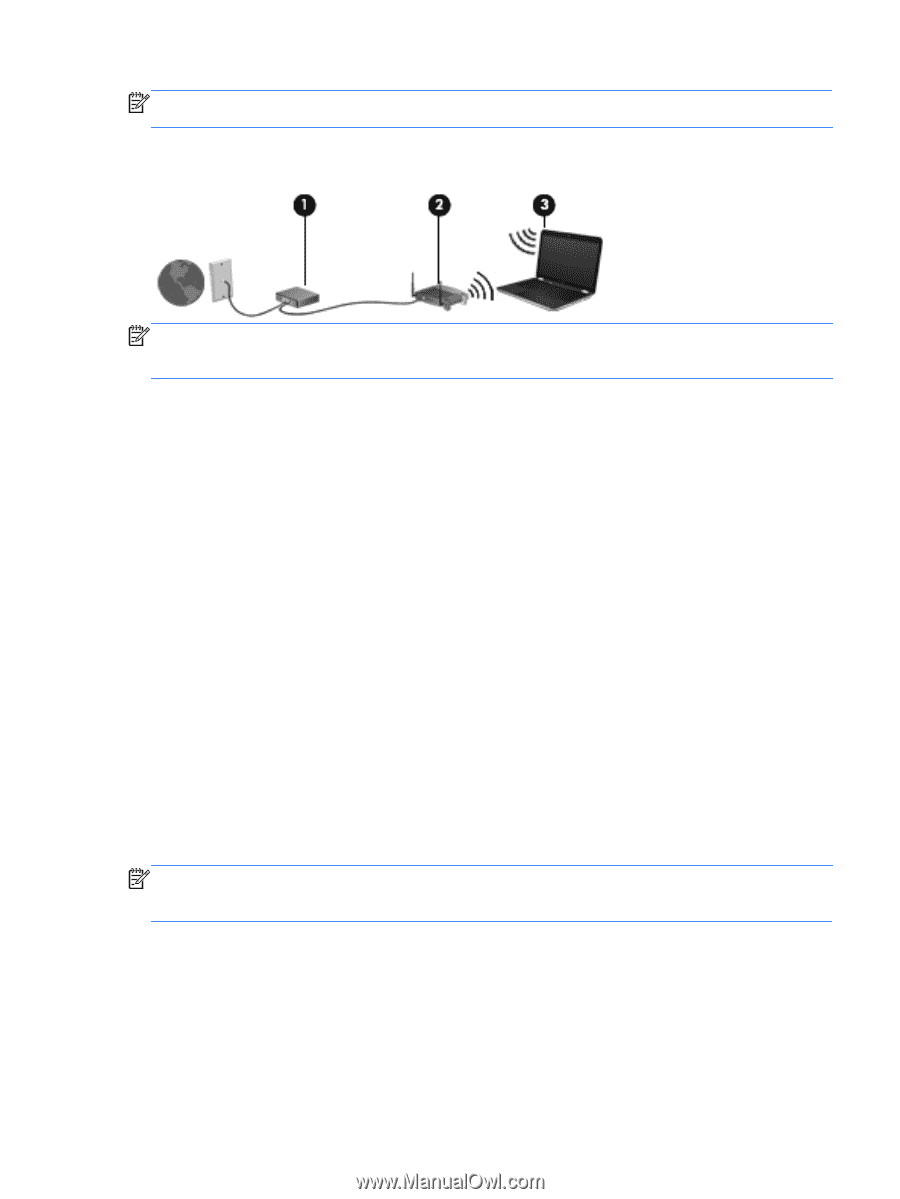
NOTE: Some cable modems include a built-in router. Check with your ISP to see if you need a separate router. The illustration below shows an example of a wireless network installation that is connected to the Internet. NOTE: When setting up a wireless connection, be sure that your computer and wireless router are synchronized. To synchronize your computer and wireless router, turn your computer and wireless router off and then back on. As your network grows, additional wireless and wired computers can be connected to the network to access the Internet. For help in setting up your WLAN, refer to the information provided by your router manufacturer or your ISP. Protecting your WLAN When you set up a WLAN or access an existing WLAN, always enable security features to protect your network from unauthorized access. WLANs in public areas (hotspots) like coffee shops and airports may not provide any security. If you are concerned about the security of your computer in a hotspot, limit your network activities to e-mail that is not confidential and basic Internet surfing. Wireless radio signals travel outside the network, so other WLAN devices can pick up unprotected signals. You can take the following precautions to protect your WLAN: ● Firewall-A firewall checks both data and requests for data that are sent to your network, and discards any suspicious items. Firewalls are available in both software and hardware. Some networks use a combination of both types. ● Wireless encryption-Your computer supports three encryption protocols: ◦ Wi-Fi Protected Access (WPA) ◦ Wi-Fi Protected Access II (WPA2) ◦ Wired Equivalent Privacy (WEP) NOTE: HP recommends that you select WPA2, which is the most advanced of the three encryption protocols. The use of WEP encryption is not recommended, because it can be overcome with little effort. ● Wi-Fi Protected Access (WPA) and Wi-Fi Protected Access II (WPA2) use security standards to encrypt and decrypt data transmitted over the network. Both WPA and WPA2 dynamically Using a WLAN (select models only) 5