bizhub C35
Contents-1
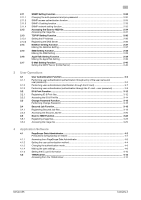
Contents
1
Security
1.1
Introduction
.....................................................................................................................................
1-2
Compliance with the ISO15408 Standard
.........................................................................................
1-2
Operating Precautions
.......................................................................................................................
1-2
INSTALLATION CHECKLIST
..............................................................................................................
1-3
1.2
Security Functions
..........................................................................................................................
1-4
Check Count Clear Conditions
..........................................................................................................
1-4
1.3
Data to be Protected
......................................................................................................................
1-5
1.4
Precautions for Operation Control
................................................................................................
1-6
Roles and Requirements of the Administrator
...................................................................................
1-6
Password Usage Requirements
........................................................................................................
1-6
Network Connection Requirements for the Machine
.........................................................................
1-6
User information control system control requirements
.....................................................................
1-6
Security function operation setting operating requirements
..............................................................
1-7
Operation and control of the machine
...............................................................................................
1-7
Machine Maintenance Control
...........................................................................................................
1-7
Operating conditions for the IC card and IC card reader
..................................................................
1-7
IC card owner requirements
..............................................................................................................
1-7
1.5
Miscellaneous
..................................................................................................................................
1-8
Password Rules
.................................................................................................................................
1-8
Precautions for Use of Various Types of Applications
.......................................................................
1-8
Encrypting communications
..............................................................................................................
1-9
IPP printing
........................................................................................................................................
1-9
Items of Data Cleared by Data Erase Function
................................................................................
1-10
HDD Format
.....................................................................................................................................
1-11
Upgrading of the firmware
...............................................................................................................
1-11
2
Administrator Operations
2.1
Accessing the Admin Settings
.......................................................................................................
2-2
Accessing the Admin Settings
...........................................................................................................
2-2
2.2
Enhancing the Security Function
...................................................................................................
2-5
Setting the Enhanced Security Mode
................................................................................................
2-7
2.3
Setting the Authentication Method
...............................................................................................
2-9
Setting the Authentication Method
....................................................................................................
2-9
2.4
ID & Print Setting Function
...........................................................................................................
2-12
Setting the ID & Print
........................................................................................................................
2-12
2.5
Auto Reset Function
.....................................................................................................................
2-13
Setting the Auto Reset function
.......................................................................................................
2-13
2.6
User Setting Function
...................................................................................................................
2-16
Making user setting
..........................................................................................................................
2-16
2.7
IC card information Setting Function
..........................................................................................
2-18
Registering information from the control panel
...............................................................................
2-18
2.8
Changing the Administrator Password
.......................................................................................
2-20
Changing the Administrator Password
............................................................................................
2-20
2.9
Erasing data when the machine is to be discarded or use of a leased machine is
terminated
......................................................................................................................................
2-22
2.9.1
Setting the Overwrite All Data
..........................................................................................................
2-22
2.9.2
Setting the SSD Low-level Format
...................................................................................................
2-25
2.9.3
Setting the Restore All
.....................................................................................................................
2-26
2.10
SSL Setting Function
....................................................................................................................
2-27
2.10.1
Device Certificate Setting
................................................................................................................
2-27
2.10.2
SSL Setting
......................................................................................................................................
2-29
2.10.3
Removing a Certificate
.....................................................................................................................
2-30