ZyXEL P-660HW-T1 v2 User Guide - Page 234
Table 99, Table 98
 |
View all ZyXEL P-660HW-T1 v2 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 234 highlights
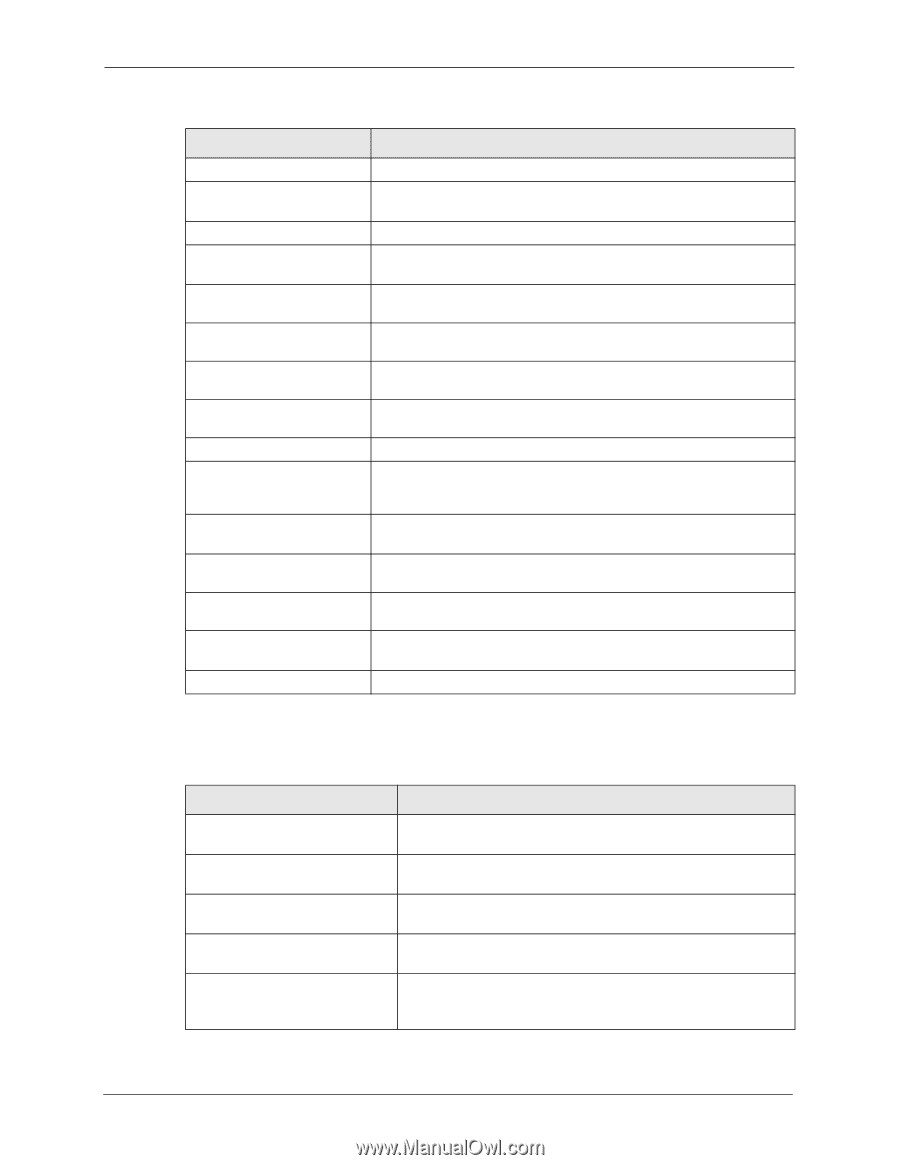
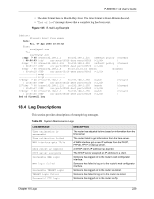
P-660HW-T v2 User's Guide Table 98 Content Filtering Logs (continued) LOG MESSAGE DESCRIPTION %s: Contains ActiveX The web site contains ActiveX. %s: Contains Java applet The web site contains a Java applet. %s: Contains cookie The web site contains a cookie. %s: Proxy mode detected The router detected proxy mode in the packet. %s The content filter server responded that the web site is in the blocked category list, but it did not return the category type. %s:%s The content filter server responded that the web site is in the blocked category list, and returned the category type. %s(cache hit) The system detected that the web site is in the blocked list from the local cache, but does not know the category type. %s:%s(cache hit) The system detected that the web site is in blocked list from the local cache, and knows the category type. %s: Trusted Web site The web site is in a trusted domain. %s When the content filter is not on according to the time schedule or you didn't select the "Block Matched Web Site" check box, the system forwards the web content. Waiting content filter The external content filtering server did not respond within the timeout server timeout period. DNS resolving failed The ZyXEL Device cannot get the IP address of the external content filtering via DNS query. Creating socket failed The ZyXEL Device cannot issue a query because TCP/IP socket creation failed, port:port number. Connecting to content The connection to the external content filtering server failed. filter server fail License key is invalid The external content filtering license key is invalid. Table 99 Attack Logs LOG MESSAGE DESCRIPTION attack [TCP | UDP | IGMP | ESP | GRE | OSPF] attack ICMP (type:%d, code:%d) land [TCP | UDP | IGMP | ESP | GRE | OSPF] land ICMP (type:%d, code:%d) ip spoofing - WAN [TCP | UDP | IGMP | ESP | GRE | OSPF] The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF attack. The firewall detected an ICMP attack. For type and code details, see Table 106 on page 242. The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF land attack. The firewall detected an ICMP land attack. For type and code details, see Table 106 on page 242. The firewall detected an IP spoofing attack on the WAN port. 234 Chapter 18 Logs