HP 8/24 Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June
HP 8/24 Manual
 |
View all HP 8/24 manuals
Add to My Manuals
Save this manual to your list of manuals |
HP 8/24 manual content summary:
- HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 1
53-1001864-01 ® March 30, 2010 Fabric OS Encryption Administrator's Guide Supporting Fabric OS v6.4.0, Supporting HP StorageWorks Secure Key Manager (SKM) Environments - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 2
any equipment, equipment feature, or service offered or to be offered by Brocade. Brocade reserves the right to make brocade.com/support/oscd. Brocade Communications Systems, Incorporated Corporate and Latin American Headquarters Brocade Communications Systems, Inc. 1745 Technology Drive San - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 3
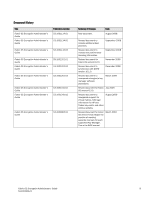
information for HP and Thales key vaults, and other various updates. August 2009 Revised document for Fabric OS version 6.4.0. Began the practice of creating separate manuals for each supported Key Manager. This is the SKM manual. March 2010 Fabric OS Encryption Administrator's Guide iii 53 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 4
iv Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 5
6 Brocade encryption solution overview 7 Data flow from server to storage 8 Data encryption key life cycle management 9 Key management systems 11 Master key management 11 Master key generation 11 Master key backup 11 Support for Virtual Fabrics 12 Fabric OS Encryption Administrator's Guide - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 6
an SKM appliance 24 Configuring a Brocade group on SKM 25 Registering the SKM Brocade group user name and password 26 Setting up the local Certificate Authority (CA) on SKM 27 Downloading the local CA certificate from SKM 28 Creating and installing the SKM server certificate 28 Enabling SSL on - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 7
81 General tab 82 Members tab 83 Consequences of removing an encryption switch 84 Security tab 86 HA Clusters tab 87 Engine Operations tab 87 Tape Pools tab 88 Encryption-related acronyms in log messages 90 Configuring Brocade encryption using the CLI In this chapter 91 Overview 91 Command - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 8
102 Enabling SSL on the Key Management System (KMS) Server 103 Creating an SKM High Availability cluster 104 Copying the local CA certificate 104 Adding SKM appliances to the cluster 105 Initializing the Brocade encryption engines 106 Registering the SKM Brocade group user name and password - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 9
re-keying 147 Initiating a manual re-key session 148 Suspension In this chapter 151 Single encryption switch, two paths from host to target switches 162 VmWare ESX server deployments 163 Best Practices and Special Topics In this chapter 165 Firmware download considerations 166 Firmware - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 10
on extension switches 176 Re-keying best practices and policies 177 Manual re-key 177 Latency in re-key operations 177 Allow re-key to complete before deleting a container 177 Re-key operations and firmware upgrades 177 Do not change LUN configuration while re-keying 178 Brocade native mode - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 11
using the CLI 198 Encryption Enabled Crypto Target LUN 198 Encryption Disabled Crypto Target LUN 199 Management application encryption wizard troubleshooting . . . .200 Errors related to adding a switch to an existing group 200 Errors related to adding a switch to a new group 201 General - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 12
Appendix C Index NS-Based Transparent Frame Redirection xii Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 13
switch Brocade SAN support matrix for disk and tape LUNs, and includes LUN policy troubleshooting information. • Appendix C, "NS-Based Transparent Frame Redirection," provides a name server (NS)-based transparent frame redirection interop matrix. Fabric OS Encryption Administrator's Guide - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 14
support data encryption as described in this manual. • Brocade DCX and DCX-4S with an FS8-18 encryption blade. • Brocade Encryption Switch command names Identifies the names of user-manipulated GUI elements Identifies keywords in the narrative portions of this guide are presented in mixed lettercase: - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 15
statements are used in this manual. They are listed below in damage to hardware, firmware, software, or Brocade Connect. See "Brocade resources" on page xvi for instructions on accessing Brocade Connect. For definitions specific to this document, see "Terminology" on page 2. For definitions of SAN - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 16
Tape backup only, no support for tape pool Legato user ID and password. For practical discussions about SAN design, implementation, and maintenance, you can obtain Building SANs with Brocade Fabric Switches through: http://www.amazon.com For additional Brocade documentation, visit the Brocade SAN - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 17
• Switch model • Switch operating system version • Error numbers and messages received • supportSave command output • Detailed description of the problem, including the switch or fabric behavior immediately following the problem, and specific questions • Description of any troubleshooting steps - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 18
and completeness of this document. However, if you find an error or an omission, or you think that a topic needs further development, we want to hear from you. Forward your feedback to: [email protected] Provide the title and version number of the document and as much detail as possible - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 19
1 •Terminology 2 •The Brocade encryption switch 4 •The FS8-18 blade 5 •Performance licensing 5 •Recommendation for connectivity 6 •Usage limitations 6 •Brocade encryption solution overview 7 •Data encryption key life cycle management 9 •Key management systems 11 •Support for Virtual Fabrics - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 20
different fabrics. DEK clusters enable host MPIO failover. Encryption switch recovers. Devices that were transferred to another switch by failover processing may automatically be transferred back, or they may be manually switched encryption, a switch, DCX, or DCX-4S through which users can manage an - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 21
together from a card reader attached to a PC running the Brocade SAN Management Application to restore the master key. Recovery cards may be targets. Redirection zones are automatically created to enable frame redirection to the virtual initiators and virtual Administrator's Guide 3 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 22
firmware upgrades and other support services. 8 Fibre Channel ports (0-31) - 1, 2, 4, or 8 Gbps auto-sensing F, FL, E, EX, or M ports to connect host servers, SAN disks, SAN tapes, edge switches, or core switches. FIGURE 1 Brocade encryption switch 4 Fabric OS Encryption Administrator's Guide - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 23
and installing an encryption performance license. The base unit Brocade Encryption Switch and FS8-18 Encryption Blade have a standard Fabric OS Administrator's Guide for information about obtaining and adding licenses. Licensing best practices Licenses installed on the switches and blades must - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 24
ports with respect to encryption flows are as follows: - Only ISLs are connected to the Brocade Encryption Switch an encryption switch or blade. Quality of Service (QoS) enabled when an encryption switch or blade is present in the fabric. 6 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 25
Brocade Brocade provides an encryption solution that resides in a Storage Area Network (SAN . Data entering the SAN from a server is high level view of the Brocade encryption solution. Cleartext is sent Switch Ciphertext based on AES256-XTS Disk Storage Ciphertext Cleartext DEKs Ciphertext based - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 26
encryption solution overview Data flow from server to storage The Brocade encryption switch can be introduced into a SAN with minimum disruption, with no need for SAN reconfiguration, and with no need to reconfigure host applications. Frames sent from a host and a target LUN are redirected to - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 27
must be used one more time to decrypt the data, and the resulting cleartext is encrypted with a new key (re-keyed). Fabric OS Encryption Administrator's Guide 9 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 28
1 Data encryption key life cycle management FIGURE 5 DEK life cycle 10 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 29
supports the following leading key management systems: • The NetApp LIfetime Key Manager (LKM) version 4.0 or later. • The RSA Key Manager (RKM) version 2.1.3 or later, available through EMC. • The HP Secure Key Manager (SKM) version only available if the switch is managed by Guide 11 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 30
The Brocade encryption switch does not support the logical switch partitioning capability and can not be partitioned, but the switch can be connected to any Logical Switch partition or Logical Fabric using an E-Port. The FS8-18 encryption blades are supported in only in a default switch partition - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 31
this chapter •Encryption Center features 14 •Encryption user privileges 15 •Smart card usage 16 •Network SKM appliance 24 •Gathering information 33 •Gathering information 33 •Creating a new encryption group 34 •Adding a switch to an OS Encryption Administrator's Guide 13 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 32
version 6.4, the Encryption Center is dynamically updated to reflect the latest changes based user privileges" on page 15 describes the Role-based enable encryption. • "Configuring blade processor links" on page 22 describes the steps for interconnecting encryption switches 24 lists the supported key - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 33
to users; users get privileges because they belong to a role in a resource group. A user can only switch, group, or engine properties, • View the Encryption Group Properties Security tab. • View encryption targets, hosts, and LUNs. • Initiate manual LUN re-keying. • Enable Guide 15 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 34
the following: • Control user access to the Management application The following smart card readers are supported: • GemPlus GemPC USB http://www See the following procedures for instructions about how to manage smart Replacement of authentication card certificates. • Enabling and Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 35
Select the Quorum Size. The quorum size is the minimum number of cards necessary to enable the card holders to perform the security sensitive operations listed above. The maximum quorum size to the Registered Authentication Cards table. Fabric OS Encryption Administrator's Guide 17 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 36
from the database and the switch by de-registering them. Use number of cards needed, as directed by instructions on the dialog box. The currently registered cards to appear in the Card ID field. 3. Enter the assigned password. 4. Click Authenticate. 5. Wait for the confirmation dialog box, - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 37
to enable the encryption engine. When the switch or blade is powered off, the encryption engine will not work without first inserting a system card into its card reader. If someone removes a switch or blade with the intent of accessing the encryption engine, it will function as an ordinary FC switch - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 38
the entire list of smart cards to a file. The available formats are comma-separated values (.csv) and HTML files (.html). 20 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 39
Card dialog box 2. Insert the smart card into the card reader. 3. After the card's ID is displayed in the Card ID field, enter the Card Password and click Login. 4. Edit the card assignment user information as needed. 5. Click OK. Fabric OS Encryption Administrator's Guide 21 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 40
supported key management appliance must be connected on the same LAN as the management port of the encryption switches, 384-port Backbone Chassis CPs, and the SAN Link dialog box displays. 3. Enter the link IP address and mask, and the gateway IP address. 4. Click OK. The Blade Processor Link - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 41
standpoint of external SAN management application operations, the FIPS crypto officer, FIPS user, and node CP certificates are transparent to users. The KAC Switch > Init Node. The following warning displays. 2. Select Yes to initialize the node. Fabric OS Encryption Administrator's Guide 23 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 42
group on SKM. • Register the Brocade group user name and password on the encryption node. • Set up a local Certificate Signing Authority (CA) on SKM. • Download the CA certificate. • Create and install an SKM server certificate. • Enable an SSL connection. • Configure a cluster of SKM appliances - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 43
are displayed. 12. In the User List section, select or type the Brocade user name under Username. 13. Select Save. The Brocade user name and password are now configured on SKM. NOTE Fabric OS version 6.2.0 uses brcduser1 as a standard user name when creating a Brocade group on SKM. If you downgrade - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 44
Brocade user name and password: - The user name and password must match the user name and password specified for the Brocade group. - The same user name and password the new encryption group uses different user name and password, the Brocade group user name and password must also be changed to the - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 45
the SKM management web console using the admin password. 2. Select the Security tab. 3. HP SKM Local CA 5. Under Certificates & CAs, select Trusted CA Lists to display the Trusted Certificate Authority List Profiles. 6. Click on Default under Profile Name. Fabric OS Encryption Administrator's Guide - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 46
steps any time another local CA is needed. Downloading the local CA certificate from SKM The local , this certificate must be imported onto the Brocade encryption group leader nodes. 1. From the Security Enter the Key Size. HP recommends using the default value: 1024. 4. Click Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 47
must be renewed based on your site's security policies. The default value is 3649 enabled on the other cluster members. To configure and enable SSL, perform the following steps: 1. Select the Device tab. 2. In the Device Configuration menu, click KMS Server to display the Key Management Services - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 48
. 3. Select and note the Local IP address. You will need this address when you add an appliance to the cluster. 4. For Local Port, use the default value of 9001 unless you are explicitly directed to use a different value for your site. 5. Type the cluster password in the Create Cluster section of - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 49
Download IP and Local Port set to their defaults. 14. Type the original cluster member's local IP address into Cluster Member IP. 15. Type the original cluster member's local Port into Cluster Member Port. 16. Click Browse and select the Cluster Key File you saved. 17. Type the cluster password - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 50
Sign Certificate Request page is displayed. 8. Select Sign with Certificate Authority using the Brocade CA name with the maximum of 3649 days option. 9. Select Client as Certificate Purpose. 10. Allow Certificate Duration to default to 3649. 11. Paste the file contents that you copied in step 3 in - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 51
blades installed have a LAN connection to the SAN management program, and are available for discovery. • A supported key management appliance is connected on the same LAN as the encryption switches, 384-port Backbone Chassis CPs, and the SAN Management program. • An external host is available - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 52
not be in an encryption group already. 3. Select a switch and select Encryption > Create/Add to Group, from the menu bar, or right-click the switch and select Create/Add to Group. The Configure Switch Encryption welcome panel displays. 34 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 53
pre-selected. This is the correct selection for creating a new group. FIGURE 11 Designate Switch Membership dialog box 5. Enter an Encryption Group Name for the encryption group (the maximum length Vault dialog box displays (Figure 12). Fabric OS Encryption Administrator's Guide 35 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 54
2 Creating a new encryption group FIGURE 12 Select Key Vault dialog box 7. Select SKM as the Key Vault Type. 36 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 55
's public key certificate or browse to the location by clicking the Browse button. c. Enter the user name and password you established for the Brocade user group. d. If you are using a backup key vault, also enter the IP address or host name, and the name of the file holding the backup key vault - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 56
know this path and file name to install the switch's public key certificate on the key management appliance. 9. Click Next. The Specify Master Key File Name panel displays (Figure 15). FIGURE 15 Specify Master Key File Name dialog box 38 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 57
Next. The Confirm Configuration panel displays the encryption group name and switch public key certificate file name you specified, shown in Figure 16 successful. A message displays below the table, indicating that the encryption switch was added to the group you named, and the public key - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 58
switch configuration. The CLI commands are detailed in the Fabric OS Encryption Administrator's Guide, "Key vault configuration." • Initialize the switch If the switch keyvault command. • Enable the encryption engines The Management application initializes an encryption switch using the cryptocfg -- - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 59
key to a file The Management application saves the master key into the specified file. 15. Click Next. The Read Instructions dialog box displays instructions for installing public key certificates for the encryption switch. These instructions are specific to the key vault type. Copy or print these - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 60
Encryption Group dialog box displays. FIGURE 19 Add Switch to Existing Encryption Group dialog box 5. Select the group to which you want to add the switch, and click Next. The Specify Public Key Certificate Filename panel displays. 42 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 61
group 2 FIGURE 20 Add switch to an encryption group - Specify Public Key Certificate filename dialog Configuration panel displays the encryption group name and switch public key certificate file name you specified. FIGURE 21 Add switch to an encryption group - Confirm Configuration dialog box - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 62
Next Steps! below this message, and click Next. Instructions for installing public key certificates for the encryption switch are displayed. These instructions are specific to the key vault type. Copy or print these instructions. 44 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 63
Configure Switch Encryption wizard. Replacing an encryption engine in an encryption group To replace an encryption Replace, or right click on the encryption engine and select Replace. The Engine Operations tab of the Encryption Group Properties dialog box displays (Figure 24 Guide 45 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 64
24 Engine Operations tab 2. Select the engine you want to replace in the Engine list. 3. Select the engine you want to use as the replacement in the Replacement list. 4. Click Replace not applied to the switch until you click An IP address is required for the management port for Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 65
too. 1. Select an encryption engine from the right tree (see Figure 25) and click the left arrow button. 2. Either remove the second engine or add a replacement second engine, making sure all HA clusters have exactly two engines. 3. Click OK. Fabric OS Encryption Administrator - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 66
in an HA cluster Swapping engines is useful when replacing hardware. Swapping engines is different from removing an online, the encryption group's failback setting (auto or manual) determines how the encryption engine resumes encrypting and decrypting Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 67
to virtual targets and virtual initiators within the encryption switch. NOTE You must zone the physical host and physical target together to enable creation of a re-direction zone. The re- 26 Configure Storage Encryption welcome panel Fabric OS Encryption Administrator's Guide 49 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 68
group, the list includes all engines in the group. • If the Targets dialog box is showing all targets for a switch, the list includes all encryption engines for the switch. • If the Targets dialog box is showing targets for a single encryption engine, the list contains only that engine. FIGURE - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 69
engine (blade or switch) you want to configure, and click Next. The Select Target panel displays. This panel lists all target ports and target nodes in targets or manually enter the port and node WWNs. FIGURE 28 Select Target dialog box a. Select a target from the list. (The Target Port WWN and - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 70
selecting hosts or manually entering the WWNs. The Name Container panel displays. The name container step in the wizard enables you to specify a name for the target container that is created in the encryption engine to hold the target configuration data. 9. The container name defaults to the target - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 71
Adding encryption targets 2 FIGURE 30 Name Container dialog box 10. Click Next. The Confirmation panel displays. FIGURE 31 Confirmation dialog box Fabric OS Encryption Administrator's Guide 53 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 72
(VI). NOTE If you can view the VI/VT Port WWNs and VI/VT Node WWNs, the container has been successfully added to the switch. FIGURE 32 Configuration Status dialog box 12. Review the configuration. If you want to save a copy of the instructions, click the Copy to Clipboard button. 54 Fabric OS - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 73
encryption targets 2 FIGURE 33 Important Instructions dialog box 14. Review the instructions about post-configuration tasks you must complete after you close the wizard. 15. Click Finish to exit the Configure Storage Encryption wizard. Fabric OS Encryption Administrator's Guide 55 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 74
dialog box displays. 2. Select the encryption group, switch, or encryption engine containing the storage device to be configured.Right-click, or select Group, Switch, or Engine from the menu bar. 3. 34 Encryption Target Hosts dialog box 56 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 75
displays. 2. Right-click a group, switch, or encryption engine or select a group, switch, or encryption engine from the Encryption Port dialog box displays (Figure 36). FIGURE 36 Add New Path Wizard 4. Select the target port from the Target Port list. Fabric OS Encryption Administrator's Guide - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 76
target disk LUNs for encryption 5. Click Next. The Select Initiator Port dialog box displays. 6. Select the initiator port from the Initiator Port list. 7. Click Next. LUN discovery is launched, and a or Apply to apply the modifications. 58 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 77
to the CryptoTarget container and enabling the encryption property on the Crypto LUN. You must add LUNs manually. After you add the LUNs port). 1. Select Configure > Encryption from the menu bar. The Encryption Center dialog box displays. 2. Select the encryption group, switch Guide 59 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 78
enabled version 6.4, disk and tape target containers can be hosted on the same switch or blade. Hosting both disk and tape target containers on the same switch or blade may result in a drop in throughput, but it can reduce cost by reducing the number of switches or blades needed to support manual - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 79
key has been lost, which happens if all encryption engines in the group have been zeroized or replaced with new hardware at the same time. • You want multiple encryption groups to share the same actions Master key actions are as follows: Fabric OS Encryption Administrator's Guide 61 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 80
been backed up. • Create new master key, which is enabled when no master key exists or the previous master key master key can be disabled: • The user does not have Storage Encryption Security permissions. See "Encryption user privileges" on page 15 for more Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 81
OK. ATTENTION Save the passphrase. This passphrase is required if you ever need to restore the master key from the file. Fabric OS Encryption Administrator's Guide 63 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 82
Key ID identifies the storage location in the key vault.) 10. Click OK after you have copied the key ID. 64 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 83
card set A card reader must be attached to the SAN Management application PC to complete this procedure. Recovery cards can driver for Linux and Solaris operating systems, however. For instructions, see the Data Center Fabric Manager Administrator's Guide. The key is divided between the cards in the - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 84
of the person to whom the card is assigned. 10. Type a Card Password. 11. Re-type the password for verification. 12. Record and store the password in a secure location. 13. Click Write Card. The dialog box prompts finish the operation. 66 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 85
. The passphrase that was used to back up the master key must be used to restore the master key. 9. Click OK. Fabric OS Encryption Administrator's Guide 67 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 86
passphrase that was used to back up the master key must be used to restore the master key. 9. Click OK. 68 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 87
smart card set A card reader must be attached to the SAN Management application PC to complete this procedure. Use the following procedure to appear. 8. Enter the password that was used to create the card. After five unsuccessful attempts to enter the correct password, the card becomes locked and - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 88
Creation dialog box displays. FIGURE 44 Confirm master key creation dialog box 5. Read the information, and click Yes to proceed. 70 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 89
engine manually to the encryption switch or the service. • The master key (for other key vaults) is erased from the encryption engine. Once enabled enabled (running) or disabled, but ready to be enabled. If the encryption engine is not in one of these states, an error Guide 71 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 90
dialog box The Encryption Targets dialog box enables you to send outbound data that Switch > Targets, or Engine > Targets, from the tool bar menu, or right-click on the group, switch switch is selected, all configured targets for the switch are displayed. The Encryption Targets dialog box enables - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 91
be configured for encryption again on some other encryption engine. If the LUN data is to be enabled and later accessed by way of another encryption engine, you should unzone the host with the encryption be in the same encryption group. Fabric OS Encryption Administrator's Guide 73 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 92
LUNs and add new LUNs. The button is enabled only if there are hosts associated with the targets to multiple target containers (one target per storage device port). When adding, modifying, or removing multi-pathed LUNs, switches. 74 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 93
departments. • An array or device is removed from service. In all cases, all data on the disk media remains uncommitted until a user-initiated commit or a error message An outstanding transaction is pending in Switch/EG. IF this happens, you can resolve the problems Guide 75 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 94
still stored on the switch. You can display on the switch, and switch. As a precaution, you may want to copy the keys to a secure location before deleting them from the switch switch encryption properties To view switch switch or encryption engine from the Encryption Devices table, and select Switch - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 95
switch. Possible values are Group Member, Leader-Member Comm, Error, Discovering, and Not a member. • Encryption Group - the name of the encryption group to which the switch key operations, enable/disable encryption engines switch belongs. Fabric OS Encryption Administrator's Guide 77 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 96
ID - the domain ID of the selected switch. • Firmware Version - the current encryption firmware on the switch. • Primary Key Vault Link Key Status link key, and Online. • Set State To - enter a new value, enabled or disabled, and click OK to apply the change. • Total Targets - the Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 97
manager appliance. Refer to "Steps for connecting to an SKM appliance" on page 24 and look through the following sections to find the procedure that applies. Importing a certificate. 3. Click OK. The file is imported onto the switch. Fabric OS Encryption Administrator's Guide 79 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 98
the Set State To entry under Encryption Engine Properties. 2. Click the field and select Enabled. 3. Click OK. Disabling the encryption engine state from Properties To disable the encryption only if the key vault type is NetApp LKM. 80 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 99
or Tivoli Key Lifetime Manager (TKLM. • REPL Support - whether or not remote replication LUNs support is enabled or disabled. You can change the current setting by clicking on the field and selecting the desired state. • Primary Key Vault IP address - The IP address of the primary key vault, either - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 100
switch is switch is not reachable by way of the management port, or if the member switch does not believe it is part of the encryption group. • Configuring - the member switch switch switch. • If you remove a switch switch. In this case, a pop-up error message displays. • If you remove the last switch - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 101
but is not usable until the encryption target is manually configured on another encryption switch. The switch has encryption engines in HA Clusters. CAUTION The encryption Remove to remove a switch. FIGURE 48 Removal of switch warning Fabric OS Encryption Administrator's Guide 83 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 102
2 Viewing and editing group properties Figure 49 shows the warning message that displays if you click Remove to remove an encryption group. FIGURE 49 Removal of switch in encryption group warning 84 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 103
(Figure 50) displays the status of the master key for the encryption group. NOTE You must enable encryption engines before you back up or restore master keys. Master key actions are as follows: • Group Properties - Security tab Fabric OS Encryption Administrator's Guide 85 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 104
Engine Operations tab enables you to replace an encryption engine in an encryption switch with another encryption engine in another switch within a DEK no user-configurable properties. Refer to "Replacing an encryption engine in an encryption group" on page 45. NOTE You cannot replace an encryption - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 105
pool. See "Adding tape pools" on page 88 for more information. Tape pools overview Tape cartridges and volumes may be organized into a tape pool instead of the tape LUN settings. Encryption switches and encryption blades support tape encryption at the tape pool level (for Guide 87 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 106
new encryption group is created, any existing tape pools in the switch are removed and must be added. 1. Select Configure > box displays. The Name tape pool label type is the default; however, you can change the tape pool label type to 88 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 107
requires a DF-compatible encryption license to be present on the switch. If the license is not present, a warning message displays. obtaining a new key, if you want to enforce a key lifespan. The default is Infinite (a blank field or a value of 0). NOTE The key lifespan Guide 89 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 108
2 Encryption-related acronyms in log messages 90 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 109
111 •High Availability (HA) cluster configuration 113 •Enabling the encryption engine 116 •Zoning considerations 117 •CryptoTarget container the Brocade Encryption Switch, DCX, or DCX-4S has been done as part of the initial hardware installation, including setting the management port IP address - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 110
in AD255 context (and the user should own access to AD0-AD255 and have admin RBAC privilege). • Disallowed = Only allowed to execute in AD0 or AD255 context, not allowed in AD1-AD254 context. • PortMember = All control operations allowed only if the port or the local switch is part of the current - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 111
Users Enable firmware download. • Perform regular Fabric OS management functions. Refer to Table 4 for the RBAC permissions of the encryption configuration commands. TABLE 4 Encryption command RBAC availability and admin domain type1 Command name User Admin Operator Switch Basic Switch Admin - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 112
) Command name User Admin Operator Switch Zone Fabric Basic Admin Admin Admin Switch Admin createtapepool N N N O N discoverLUN N OM N N N OM N eject N OM N N N O N enable N OM N N N O N enableEE N OM N N N O N export N OM N N Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 113
Command name User Admin Operator Switch Zone Fabric Basic Admin Admin Admin Switch Admin removeinitiator N OM N N N OM N removeLUN N OM N N N OM N replace N OM N N N OM N set N OM N N N O N setEE Encryption Administrator's Guide 95 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 114
Link Key on the specified EE. --disableEE []: This command reboots the Mace switch or power cycle the Lance blade in case of chassis system. --enableEE []: Enables the system to perform encryption. --zeroizeEE []: Zeroize all critical security parameter. --import - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 115
. All switches you plan to include in an encryption group must be connected to the key management system. Either IPv4 and IPv6 addressing may be used, but all nodes, including the key management system, must use the same version of IP addressing. Fabric OS Encryption Administrator's Guide 97 53 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 116
switch:admin> ipaddrset -slot 7 -gate --add 10.32.1.1 There are additional considerations if blades are removed and replaced, or moved to a different slot. On chassis-based systems, IP previously configured for a different type of blade with two IP ports (an FC4-16E blade, for example), the FS8-18 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 117
IP address is configured after the encryption engine is enabled for encryption, or if the IP address of the cluster link ports is modified after encryption engine is enabled for encryption, the encryption switch IP Address change of a node within an encryption group Modifying the IP IP IP version IP address - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 118
are displayed. 12. In the User List section, select or type the Brocade user name under Username. 13. Select Save. The Brocade user name and password are now configured on SKM. NOTE Fabric OS version 6.2.0 uses brcduser1 as a standard user name when creating a Brocade group on SKM. If you downgrade - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 119
the Trusted Certificate Authority List Profiles. 6. Click on Default under Profile Name. 7. In the Trusted Certificate Authority List, click Edit. 8. From the list of Available CAs in the right panel, select the CA you just created. Fabric OS Encryption Administrator's Guide 101 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 120
the downloaded file, changing the .cert extension to a .pem extension. This file is needed later when "Registering SKM on a Brocade Officer to go. - Enter the Key Size. HP recommends using the default value: 1024. 4. Click Create Certificate Request. Successful Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 121
must be renewed based on your site's security policies. The default value is 3649 enabled on the other cluster members. To configure and enable SSL, perform the following steps: 1. Select the Device tab. 2. In the Device Configuration menu, click KMS Server to display the Key Management Services - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 122
. 3. Select and note the Local IP address. You will need this address when you add an appliance to the cluster. 4. For Local Port, use the default value of 9001 unless you are explicitly directed to use a different value for your site. 5. Type the cluster password in the Create Cluster section of - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 123
Download IP and Local Port set to their defaults. 14. Type the original cluster member's local IP address into Cluster Member IP. 15. Type the original cluster member's local Port into Cluster Member Port. 16. Click Browse and select the Cluster Key File you saved. 17. Type the cluster password - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 124
Brocade encryption node (switch switch as Admin or SecurityAdmin. 2. Zeroize all critical security parameters (CSPs) on the switch switch or a blade. • When the encryption engine is on an encryption switch, reboot the switch time on the switch and the key node. SecurityAdmin:switch>cryptocfg -- switch - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 125
SKM Brocade group user name and password The Brocade group user name and password you created when configuring a Brocade group on SKM must also be registered on each Brocade encryption node. 1. Log into the switch as Admin or SecurityAdmin. 2. Register the HP SKM Brocade group user password and user - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 126
. 13. Download the signed certificate to your local system as signed_kac_skm_cert.pem. 14. Import the signed certificate from its location, or from a USB storage device. SecurityAdmin:switch>cryptocfg --import -scp signed_kac_skm_cert.pem \ 192.168.38.245 mylogin /tmp/certs/kac_skm_cert.pem Password - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 127
file> primary At this point, it may take around one minute to fully configure the switch with SKM. 5. As the switches come up, enable the encryption engines. SecurityAdmin:switch>cryptocfg --enableEE Operation succeeded. Fabric OS Encryption Administrator's Guide 109 53-1001864 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 128
Vault: IP address: Certificate ID: Certificate label: State: Type: 10.32.53.55 Brocade skmcert Connected SKM Secondary Key Vault not configured Additional Key Vault/Cluster Information: Key Vault/CA Certificate Validity: Port for Key Vault Connection: Time of Day on Key Server: Server SDK Version - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 129
Note that the Brocade SAN management application provides switch>cryptocfg --export -scp -currentMK \ 192.168.38.245 mylogin GL_MK.mk Password IP Address: 10.32.244.71 Certificate: GL_cpcert.pem Current Master Key State: Configured Current Master KeyID: 8f:88 for enableEE 8f:88:45:32:8e:bf - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 130
IP Address: 10.32.244.60 Certificate: enc1_cpcert.pem Current Master Key State: Configured Current Master KeyID: 8f:88 This example shows the encryption group brocade with two member nodes, one key IDs are zero. SecurityAdmin:switch>cryptocfg --show -groupmember -all NODE Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 131
default, but is configurable with a manual page 98 for instructions. • Configuration the case for Brocade encryption switches, but is not true if two FS8-18 blades in the same DCX or DCX-4S chassis are configured in the same HA cluster. In Fabric OS version Guide 113 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 132
number if the encryption engine is a blade. The following example adds a Brocade FS8-18 in slot 5 to the HA cluster HAC2. SecurityAdmin:switch>cryptocfg --add -haclustermember HAC2 \ 10:00:00:60:5b:03:1c:90 committing the transaction. 114 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 133
an HA cluster when an encryption switch or blade that failed earlier has been restored or replaced. Automatic failback mode is enabled by default. • manual - Enables manual failback mode. In this mode, failback must be initiated manually when an encryption switch or blade that failed earlier has - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 134
steps or to troubleshoot an encryption engine that behaves in unexpected ways. Use the cryptocfg --show -localEE command to check the encryption engine status. SecurityAdmin:switch> cryptocfg --show -localEE EE Slot: 1 SP state: Online Primary Link KeyID: 85:1c:ca:dd:fc:8c:31:fc:87:21:26:d1:24:a0:92 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 135
Node WWN/Slot EE IP Addr EE State switch default zoning to no access Initially, default zoning for all Brocade switches is set to All Access. The All Access setting allows the Brocade Encryption Switch FCS switch, change the default zoning setting to No Access. switch:admin> defzone --noaccess switch - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 136
with legacy platforms. In McDATA fabrics, the hosts and the switches hosting the targets require firmware versions M-EOSc 9.8 and M-EOSn 9.8. Only the M6140, M4700F, McDATA 4400, and the Brocade Intrepid 10000 support frame redirection. Creating an initiator - target zone 1. Log into the - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 137
by a configuration name and the zone member name. FabricAdmin:switch>cfgcreate itcfg, itzone 6. Enable the zone configuration. FabricAdmin:switch>cfgenable itcfg You are about to enable a new zoning configuration. This action will replace the old zoning configuration with the current configuration - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 138
by a configuration name and the zone member name. FabricAdmin:switch>cfgcreate itcfg, itzone 9. Enable the zone configuration. FabricAdmin:switch>cfgenable itcfg You are about to enable a new zoning configuration. This action will replace the old zoning configuration with the current configuration - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 139
port hosted on a Brocade Encryption Switch ports, each target port is hosted on a separate encryption switch or blade. There is a one-to-one mapping between virtual target and physical target to the fabric whose LUNs are being enabled switch instructions described in the section "Configuring a multi - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 140
version 6.4, disk and tape target containers can be hosted on the same switch or blade. Hosting both disk and tape target containers on the same switch or blade may result in a drop in throughput, but it can reduce cost by reducing the number of switches or blades needed to support manual - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 141
must be hosted on only one Encryption switch (or pair in case of HA deployment). Another such target port should be hosted on a different encryption switch either in the same fabric or in a different fabric based on host MPIO configuration. A given host port through which the LUNs are accessible is - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 142
ports before committing the container configuration. Failure to do so results in data corruption. Refer to the section "Configuring a multi-path Crypto LUN" on page 141 for specific instructions and the virtual target. FabricAdmin:switch>cfgshow Defined configuration: cfg: Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 143
a CryptoTarget container You may delete a CryptoTarget container to remove the target port from a given encryption switch or blade. Deleting a CryptoTarget container removes the virtual target and all -key session on clear text LUNs. Fabric OS Encryption Administrator's Guide 125 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 144
switch>cryptocfg --delete -container my_disk_tgt Operation Succeeded 3. Commit the transaction. FabricAdmin:switch the encryption switch and another LSAN zones and manually created redirect on page 159 for instructions on configuring encryption in . FabricAdmin:switch>cryptocfg --move - - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 145
is not enabled for encryption LUN per HA cluster pair is supported. When an actual LUN has switch or blade or on different encryption switches multiple hosts, follow the instructions described in the section Brocade Encryption platform provides LUN discovery services Guide 127 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 146
virtualization software or any other configuration that involves mounted file systems on the LUN, you must enable first-time encryption at the time when you create the LUN by setting the --enable_encexistingdata lost and unrecoverable. 128 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 147
encryption_format option to set the format to DF_compatible (the default is Native). The following example adds a disk LUN enabled for encryption. FabricAdmin:switch>cryptocfg --add -LUN my_disk_tgt 0x0 \ 10:00:00 options are modifiable. Fabric OS Encryption Administrator's Guide 129 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 148
target ports The Brocade encryption solutions supports up to Enables or disables a LUN for encryption. Valid values are: • cleartext - Encryption is disabled. This is the default setting. When the LUN policy is set to cleartext the following policy parameters are invalid and generate errors - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 149
container of type tape. Refer to the section "Creating a CryptoTarget container" on page 123 for instructions. a. Create the container, allowing the encryption format to default to Native. FabricAdmin:switch>cryptocfg --create -container tape my_tape_tgt \ 10:00:00:05:1e:41:9a:7e 20:0c:00 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 150
to encrypt, or the encryption format from Brocade native to DF-compatible while data is being :switch>cryptocfg --commit Operation Succeeded d. Display the LUN configuration FabricAdmin:switch>cryptocfg encryption format from Brocade native to DF-compatible. FabricAdmin:switch>cryptocfg --modify - - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 151
and the initiator PWWN. FabricAdmin:switch>cryptocfg --remove -LUN my_disk_tgt the configuration. FabricAdmin:switch>cryptocfg --commit Operation same encryption switch or blade or on different encryption switches or blades being exposed through the encryption switch and another path has direct - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 152
and the parameter you wish to modify. FabricAdmin:switch>cryptocfg --modify -LUN my_disk_tgt 0x0 10:00:00 example, by force-enabling the LUN, -enable_encexistingdata and -enable_rekey are disabled by default, and you must error. 134 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 153
the encryption format from Brocade native to DF-compatible troubleshooting" on page 204 for a description of conditions under which a LUN may be disabled, and for recommendations on re-enabling :switch>cryptocfg --enable device is removed from service. In all cases Guide 135 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 154
remains uncommitted until a user-initiated commit or a error message An outstanding transaction is pending in Switch/EG. IF this happens, you can resolve the problems to be deleted after a decommissioning operation manually from the keyvault. cryptocfg -show -decommissionedkeyids Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 155
enable (defaults or switch instructions switch or blade. • A tape pool must first be created on the encryption switch or blade before you can label the tape media and assign them to the tape pool. Failure to observe this sequence invalidates tape pool-level settings and policies, and default - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 156
the None pool pool host: ANYHOST pool user: ANY pool group: NONE 4. Use the pool number as the tape pool number on the encryption switch or blade. NetWorker labeling NetWorker does not the tape pool on your encryption switch. 138 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 157
or Brocade native (default) NOTE To encrypt tapes in DataFort-compatible encryption format (both metadata and encryption algorithm), the DataFort-compatible encryption format needs to be set both at the LUN-level (tape drive) and at the tape pool-level. This ensures that the latest version of - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 158
both. The following example changes the encryption format from Brocade native to DF-compatible. FabricAdmin:switch>cryptocfg --modify -tapepool -label my_tapepool -encryption_format DF_compatible a unique key, matching DataFort behavior. 140 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 159
on a dual-port target that is accessed over two paths by a dual-port host. The two encryption switches form an encryption group and an HA cluster. The following example illustrates a simplified version of a multi-path LUN configuration. Fabric OS Encryption Administrator's Guide 141 53-1001864 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 160
2. Refer to the section "Creating an initiator - target zone" on page 118 for instructions. 3. On the group leader encryption switch (switch 1), create a CryptoTarget container for each target port and add the hosts in sequence. Do NOT commit the configuration until you have created all CryptoTarget - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 161
> e. Commit the configuration. FabricAdmin:switch>cryptocfg --commit Upon commit, redirection zones are created for target port 1, host port 1 and target port 2, host port 2. These redirection zones include the and data corruption. Fabric OS Encryption Administrator's Guide 143 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 162
Rekey: enabled Key ID: not available Key life: 47 (minute) Rekey status: 0 Operation succeeded. 7. Commit the LUN configuration. FabricAdmin:switch>cryptocfg -commit NOTE There is a 25 LUN transaction limit per commit operation. Make sure to issue commit after adding 24 LUNs (12 LUNs - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 163
at which the key expires and automatic re-keying should take place (time period in days) Enabling automatic re-keying is valid only if the LUN policy is set to encrypt and the encryption format is Brocade native. Refer to the section "Crypto LUN parameters and policies" on page 129 for more - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 164
disk array LUNs or fixed block devices. There is no re-keying support for tape media. If there is a need to re-encrypt encrypted encryption sessions. This includes both re-key (auto and manual) and first time encryption sessions. When scheduled re-key Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 165
• Set LUN policy as either cleartext or encrypt. • If cleartext is enabled (default), all encryption-related options are disabled and no DEK is associated with the 129 for more information. • When using Brocade native mode in LKM installations, manual rekey is highly recommended. If auto rekey is - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 166
encryption group must be online for this operation to succeed. The manual re-keying feature is useful when the key is compromised and rekey" 5. Check the status of the re-keying session. FabricAdmin:switch> cryptocfg --show -rekey -all Number of rekey session(s):1 Container name Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 167
error is logged. All cluster members are notified. Host I/O to all regions of the LUN is halted. Only READ operations are supported FabricAdmin:switch>cryptocfg re-key session. FabricAdmin:switch> cryptocfg --show -rekey instructions on how to remove a LUN by force. Fabric OS Encryption - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 168
3 Data re-keying 150 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 169
Deployment Scenarios Chapter 4 In this chapter •Single encryption switch, two paths from host to target 152 •Single fabric deployment part of an edge fabric 161 •Deployment with FCIP extension switches 162 •VmWare ESX server deployments 163 •VmWare ESX server deployments 163 Fabric OS - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 170
T2. Host port 1 is zoned with target port 1, and host port 2 is zoned with target port 2 to enable the redirection zoning needed to redirect traffic to the correct CTC. FIGURE 58 Single encryption switch, two paths from host to target 152 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 171
Edge Switch Host Edge Switch Target Edge Switch Virtual Target Encryption Switch Virtual Initiator Target Target Cluster Link Dedicated Cluster Network LAN Cluster Link Ciphertext Cleartext FIGURE 59 Single fabric deployment - HA cluster Fabric OS Encryption Administrator's Guide 153 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 172
the communication needed to distribute and synchronize configuration information, and enable the two switches to act as a high availability (HA) cluster, providing automatic failover if one of the switches fails, or is taken out of service. Single fabric deployment - DEK cluster Figure 60 shows an - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 173
2 to target port 2 is defined in a CryptoTarget container on the other encryption switch. This forms a DEK cluster between encryption switches for both target paths. Please note that configuring an HA cluster between the two encryption switches in the above configuration is not supported. The DEK - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 174
DEK Cluster Host Port 1 Encryption Switch 2 GE Port(s) HA Cluster1 Encryption Switch 1 Fabric1 Host Port 2 CTC3 Encryption Switch 3 Fabric2 GE Port(s) HA Cluster2 Encryption Switch 4 GE Port(s) CTC1 Target Target Port 2 Port 3 Target Port 1 Target Port 4 CTC4 GE Port(s) IO Sync Link - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 175
to target port 3and target port 4 in fabric 2. • There are four Brocade encryption switches organized in HA clusters. • HA cluster 1 is in fabric 1, and HA cluster 2 is in fabric 2. • There is one DEK cluster, and one encryption group. Fabric OS Encryption Administrator's Guide 157 53-1001864 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 176
Port 1 DEK Cluster Encryption Switch 1 Fabric1 Ecryption Group Host Port 2 Fabric2 Encryption Switch 2 CTC3 Target Target Port 2 Port 3 Target Port 1 Target Port There are two host ports, one in each fabric. • Host port 3 and target port 4 in fabric 2. • There are two encryption switches - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 177
with the host and target edge fabrics using device sharing between backbone and edge fabrics. FIGURE 64 Encryption switch connected to FC router as part of backbone fabric FIGURE 65 Encryption switch as FC router and backbone fabric Fabric OS Encryption Administrator's Guide 159 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 178
creating and enabling the port WWNs can be obtained by running the cryptocfg --show -container -cfg command on the encryption switch Guide for information about LSANs, LSAN zoning, and Fibre Channel routing (FCR) configurations. 160 Fabric OS Encryption Administrator's Guide - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 179
Target FIGURE 66 Encryption switch as part of an edge fabric The following is a summary of steps for creating and enabling the frame redirection features and VT port WWNs can be obtained by running the cryptocfg --show -container -cfg command on the encryption switch or blade - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 180
enable long distance connections. Figure 67 shows an encryption switch deployment in a Fibre Channel over IP (FCIP) configuration. Refer to the Fabric OS Administrator's Guide link. If the encryption services are enabled for the host and the remote target, the encryption switch can take clear text - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 181
physical HBA port connection, or it may use a virtual port and share a physical HBA port with port 1 to target port 1, redirected through CTC T1. • Host port 2 to target port 2, redirected through CTC T2. Host port 1 is zoned with target port 1, and host port 2 is zoned with target port 2 to enable - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 182
host port 2 is zoned with target port 2 to enable the redirection zoning needed to redirect traffic to the correct CTC. Key Management Appliance or Key Vault Management Network LAN DCFM CTC1 (T1) Management Link Management Link VmWare ESX Server Guest OS1 Guest OS2 V-Port1 V-Port2 FC HBA - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 183
Topics 5 In this chapter •Firmware download considerations 166 •HP-UX considerations 171 •Enable of a disabled LUN 171 based encryption 176 •Avoid double encryption 176 •PID failover 176 •Turn off compression on extension switches 176 •Re-keying best practices and policies 177 •Changing IP - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 184
to v6.2.0 results in a loss of encryption services. • Fabric OS version 6.2.0 supports only one HP SKM key vault. Registering of a second HP SKM key vault will be blocked. • Fabric OS version 6.2.0 uses brcduser1 as a standard user name when creating a Brocade group on SKM. If you downgrade from - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 185
6.4.0 is enforced in an encryption group if any of the Fabric OS version 6.4.0 features are enabled. If any Fabric OS version 6.4.0 feature is in an enabled state then any firmware download to Fabric OS version 6.3.x or earlier versions is blocked. - Do not try to use configupload from Fabric OS - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 186
the failback mode to auto from manual, if required by issuing the following command. cryptocfg --set -failback auto Configuration upload and download considerations Important information is not included when you upload a configuration from an encryption switch or blade. Extra steps are necessary - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 187
. Perform following steps prior to configuration download to generate and obtain the necessary certificates user certificates 2. Import peer nodes/switches certificates onto the switch prior to configuration download. 3. Import key vault certificates onto switch prior to configuration download - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 188
is run, use the following command to change the ownership of containers to the new encryption switch or blade, assuming the host and target physical zone exists. cryptocfg -replace 4. Commit the configuration. cryptocfg --commit 5. Use the following command to - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 189
Based on the LUN list returned as part of LUN discovery, add the LUN 0 if LUN 0 is present in the target (which is usually the case). Enable switch software, and some additional latency should be expected. Tape metadata One kilobyte of metadata is added per tape block for both the native Brocade - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 190
supports compression, but is not enabled by the host backup application, then compression is not performed by the encryption switch cleartext), format (such as native Brocade format or DF-compatible), and level policies are ignored and default LUN level policies are applied. Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 191
has a user-determined lifespan, version disks are not supported for reading. Only DF version 3.x-compatible disk block formats and metaheaders are supported for writing and encrypting disk LUNs in DF-compatible format. A DF-compatible license is required. Fabric OS Encryption Administrator's Guide - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 192
encryption switch or switch or FS8-18 blade. • To enable host MPIO, LUNs must also be available through a second target port, hosted on a second encryption switch. The second encryption switch switches, and host the target port as a virtual target on one of the switches encryption switch or FS8 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 193
disrupted. To recover, re-enable the existing device configuration by by the encryption device do not support the AD feature in this to denial of encryption services. Master key usage In DHCP for IP interfaces Do not use DHCP interfaces. Assign static IP addresses. Ensure uniform - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 194
. These operating systems include the following: • HP-UX prior to 11.x • All versions of IBM AIX • Solaris 2.x Turn off compression on extension switches If tape piplining and fast write are enabled on an extension switch, data compression may also be enabled. If data has been encrypted in its path - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 195
users, and can be compromised only by an insider breach of security. Manual ports labeled Ge0 and Ge1) must be configured, and must both be connected to the I/O sync LAN to enable and firmware upgrades All nodes in an encryption group must be at the same firmware level Guide 177 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 196
IP Address change of a node within an encryption group" on page 99. Disabling the encryption engine The disable EE interface command cryptocfg --disableEE [slot no] should be used only during firmware download All Cryptotarget containers hosted on the encryption switch or FS8-18 blade must either be - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 197
targets, and LUNs accessed, Brocade Encryption Engines (EEs) are designed to support a fan-In ratio of between four and eight initiator ports to one target port, in terms of the number of distinct initiator ports to a Crypto Container (i.e., a virtual target port corresponding to the physical target - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 198
. • For Windows-based host clusters, when the case for Brocade encryption switches, but is not version 6.3.0 and later releases, HA cluster creation is blocked when encryption engines belonging to FS8-18 blades in the same DCX or DCX-4S are specified. 180 Fabric OS Encryption Administrator's Guide - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 199
Troubleshooting examples using the CLI 198 •Management application encryption wizard troubleshooting 200 •Errors related to adding a switch to an existing group 200 •LUN policy troubleshooting to the section "Replacing an HA cluster member" on page 185 for instructions. The procedure for removing - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 200
switch>cryptocfg --show -groupmember \ 10:00:00:05:1e:41:99:bc Node Name: 10:00:00:05:1e:41:99:bc (current node) State: DEF_NODE_STATE_DISCOVERED Role: MemberNode IP the node WWN. SecurityAdmin:switch>cryptocfg --dereg -membernode 10 switch group. SecurityAdmin:switch>cryptocfg --eject - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 201
leader as Admin or SecurityAdmin 2. Enter the cryptocfg --delete -encgroup command followed by the encryption group name. SecurityAdmin:switch>cryptocfg --delete -encgroup brocade Encryption group create status: Operation Succeeded. Fabric OS Encryption Administrator's Guide 183 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 202
Cluster. Refer to the section "Replacing an HA cluster member" on page 185 for instructions on replacing a failed encryption engine in an the transaction is committed. SecurityAdmin:switch>cryptocfg --show -hacluster -all Encryption Group Name: brocade Number of HA Clusters: 2 Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 203
replacement encryption engine must be part of the same encryption group as the encryption engine that is replaced. SecurityAdmin:switch>cryptocfg --replace replace -haclustermember command on the group leader to replace adds the replacement encryption to the replacement encryption engine the replaced - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 204
6 Encryption group and HA cluster maintenance FIGURE 72 Replacing a failed encryption engine in an HA cluster 186 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 205
engine (EE2) are transferred to the replacement encryption engine (EE3). 2. Commit the transaction. 3. Remove the encryption engine EE2 from the encryption group. FIGURE 73 Replacing a "live" encryption engine in an HA cluster. Fabric OS Encryption Administrator's Guide 187 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 206
Enter the cryptocfg --commit command to commit the transaction. Performing a manual failback of an encryption engine By default, failback occurs automatically if an encryption engine that failed was replaced or comes back online. When manual failback policy is set in the encryption group, you must - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 207
brocade Number of HA Clusters: 1 HA cluster name: HAC3 - 2 EE entries Status: Committed WWN Slot Number EE1 => 10:00:00:05:1e:53:89:dd 0 EE2 => 10:00:00:05:1e:53:fc:8a 0 Status Online - Failover active Online • A manual failback is issued. SecurityAdmin:switch replaced Assumptions replace - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 208
cluster maintenance Recovery 1. Configure the IP address 0f the new node that is replacing the failed node, and the IP addresses of the I/O cluster sync ports (Ge0 and Ge1), and initialize the node with the cryptocfg --initnode command. 2. Register the new node IP address and CP certificate with the - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 209
, and N1 now performs all of the rebooted node's encryption services. Any re-key sessions in progress continue. Re-key sessions invoke a manual failback if required. Refer to the section "Performing a manual failback of an encryption engine" on page 188 for instructions. A Guide 191 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 210
require communication with the "offline" member nodes. You cannot start any re-key operations (auto or manual) on any of the nodes. Refer to the section "Configuration impact of encryption group split or encryption traffic is concerned. 192 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 211
require communication with the "offline" member nodes. You cannot start any re-key operations (auto or manual) on any of the nodes. Refer to the section"Configuration impact of encryption group split or node leader to all member nodes. Fabric OS Encryption Administrator's Guide 193 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 212
an encryption group • Registering a member node (IP address, certificates) • Removing an encryption engine a master key • Restoring a master key • Enabling or disabling encryption on an encryption engine • Creating • Starting a manual re-keying session • Performing a manual failback of containers - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 213
the console. Determine if the default port has been changed on the key vault. Power cycle the DCX chassis and then issue the cryptocfg --enableEE [slot number] command to bring the container's LUN state to Encryption Enabled.If the eth0 IP address on the Brocade Encryption Switch or on the FS8-18 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 214
for these ports were configured after the EE is enabled, reboot the encryption switch or slotpoweroff/slotpoweron the encryption blade to sync up the IP address information to the EE. Re-keying fails with error "Disabled (Key not in sync)". cryptocfg --commit fails with message "Default zone set - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 215
troubleshooting I 6 TABLE 10 Problem General errors more) LKM database searches may get queued and may not get serviced fast enough, and the request times out. There is no workaround enable the LUN. 3 Decommission the LUN. When a Brocade 7600 application platform is in the data path, I/O errors - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 216
examples using the CLI Troubleshooting examples using the CLI Encryption Enabled Crypto Target LUN The LUN state should be Encryption enabled for the host to see the Crypto LUN. switch:FabricAdmin> cryptocfg --show -LUN kmfvt 0 21:01:00:e0:8b:a9:ac:d2 -stat Container name: lkmfvt - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 217
Troubleshooting examples using the CLI 6 Encryption Disabled Crypto Target LUN If the LUN state is Encryption Disabled the host will not be able to access the Crypto LUN. switch:FabricAdmin>> cryptocfg --show - Operation succeeded Fabric OS Encryption Administrator's Guide 199 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 218
, and describes how to troubleshoot them. TABLE 11 Error recovery instructions for adding a switch to an existing group Configuration task Error description Instructions Initialize the switch Initialize the switch Add the switch to the encryption group Enable the encryption engines Save the - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 219
, and describes how to troubleshoot them. TABLE 12 Error recovery instructions for adding a switch to a new group Configuration task Error description Instructions Initialize the switch Create encryption group on the switch Register one or more key vaults Enable the encryption engines Unable - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 220
dialog box. 2 Re-run the Configure Switch Encryption wizard for the switch. Manual Option: 1 Save the switch's public key certificate to a file using the Switch Encryption Properties dialog box. 2 Follow the Key Vault instructions 202 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 221
wizard. TABLE 13 Problem General errors related to the Configure Switch Encryption wizard Resolution Initialization fails on the encryption engine after the encryption engine is zeroized. Reboot the switch. Configuration Commit fails with message "Default zone set to all Default zoning must be - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 222
problems related to LUN policies. TABLE 14 LUN policy troubleshooting Case Reasons for the LUN getting disabled by Action taken the encryption switch If you do not need to save the data: If you need to save the data: 1 The LUN was modified from encrypt LUN is disabled. Issue the cryptocfg -enable - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 223
to replace the failed group leader node with a new node: 1. On the new node, perform the switch/node initialization steps as described in Chapter 3. 2. Create an encryption group on the new node with the same encryption group name as before. 3. Use the configdownload command to download - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 224
that only one path is active to the LUN, but the Brocade encryption switch internal LUN states for both paths will now likely be displayed as Encryption Enabled. In active/passive storage array environments, for troubleshooting purposes, you may want to update the encryption engine Internal LUN - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 225
MPIO and internal LUN states 6 FabricAdmin:switch> cryptocfg --show -rekey -all • Read all data off the LUN and write it to . Refer to the section "Removing a LUN from a CryptoTarget container" on page 133 for instructions on how to remove a LUN by force. Fabric OS Encryption Administrator - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 226
6 MPIO and internal LUN states 208 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 227
security processor (SP) state Description Not available Not Brocade Encryption Switch or DCX Not Ready Fail to connect to blade is awaiting FIPS certificates. Run regEE. Awaiting the explicit enabling of encryption engine. Run enableEE. Encryption engine is operational but Guide 209 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 228
LUN_READONLY_3 LUN_WR_META_IN_PROG Unknown LUN state unavailable. Initialize LUN discovery in progress. LUN discovery complete. LUN setup cleartext encryption enabled. Encryption enabled. Read only (found native metadata while LUN is in DF mode). Read only (found DF metadata while LUN - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 229
Key expired re-key is pending. LUN_MANUAL_REKEY_PENDING Manual re-key is pending. LUN_DECRYPT_PENDING Data decryption Disabled (Get key record API returns error). LUN_DIS_DEK_GET_CB_ERR Disabled (Key retrieval from with failure). Fabric OS Encryption Administrator's Guide 211 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 230
(Wrong device type found). LUN_DIS_NOT_SUPPORTED Disabled (LUN not connected or supported). LUN_DIS_CFG_KEY_NOT_FOUND Disabled (Unable to retrieve key by key ID specified cleartext). LUN_STATE_UNKNOWN State of the LUN is unknown. 212 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 231
error. If it occurs, contact Brocade support. Target port is not currently in the fabric. Check connections and L2 port state. The target port is active, but this particular Logical Unit is not supported by that target. This indicates a user configuration error switch or blade - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 232
its current tape policy is DataFort-compatible mode, but The encryption switch or blade does not have the appropriate license to enable this feature. The tape medium is neither readable nor writable. ABORTED COMMAND returned to host. 214 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 233
19 DataFort compatibility support matrix for disk LUNs DataFort firmware versions Brocade handling for DF disk LUNs - Read Brocade handling for DF-compatible encryption - Write Version 1.x Version 2.x (No Metadata on the LUN) Version 3.x The encryption switch will support reading and decrypting - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 234
No error. If the LUN was previously DF-encrypted, the LUN is set to Read Only until you either remove the LUN and add it back with the native Brocade encryption format, or issue the runtime CLI command to force the change. The data encryption key is retrieved from the key vault based - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 235
key ID input is not applicable to cleartext. Error is returned from the CLI. No error. If the LUN was previously Brocade encrypted, the LUN is set to Read Only until you either modify the encryption format or user the runtime cryptocfg --enable -LUN command to force the change. The LUN is disabled - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 236
Brocade Encrypt No (Brocade) DF Cleartext Encrypt enable -LUN command to force the change from the current state of the LUN to encrypt. No error. First time encryption started to convert the LUN from cleartext to encrypt. No error. The key ID is ignored. Not a valid combination. Cleartext support - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 237
firmware versions Brocade handling for DataFort written tapes - Read Brocade handling for DataFort-compatible encryption - Write DF SAN version 1.x DF SAN version 2.x/3.x 1.x tape support in DF-compatible mode is not supported in Fabric OS v6.1.1_enc. The encryption switch supports reading - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 238
Compatibility support matrix for tape pools (Continued) Tape pool encryption format Tape pool policy Metadata present Results DF-compatible DF-compatible DF-compatible DF-compatible Encrypt Cleartext Cleartext Cleartext No (new tape) Brocade metadata DF metadata No (new tape) No error. A new - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 239
and EOSn 9.8 or later. Also requires a FOS switch with firmware version 6.1.1 or later in the fabric to manually create redirection zones. 1. Only the M6140, M4700F, McDATA 4400, and Brocade Intrepid 10000 are supported for frame redirection. NOTE When an EOSc switch is powered down and powered up - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 240
C NS-Based Transparent Frame Redirection 222 Fabric OS Encryption Administrator's Guide 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 241
Brocade Encryption Switch See switch C certificates storing the public key, 38 CLI general errors and resolution, 195 using to configure encryption switch tasks to complete before encryption, 91 configuring target ports, 174 container adding a LUN to CryptoTarget using the Guide 223 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 242
in fibre channel routed fabrics, 159 deployment with FCIP extension switches, 162 dual fabric deployment, 155 single fabric deployment, 153, for IP interfaces, 175 discover commands --discover -LUN, 143 --discoverLUN, 127, 131 disk metadata, 171 E eject commands -eject -membernode, 182 enable a - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 243
recovery instructions for adding a switch to a new group, 201 for adding a switch to an existing group, 200 error recovery instructions for adding a switch to an existing group, 200 errors related to the CLI, 195 export commands --exportmasterkey, 111 Fabric OS Encryption Administrator's Guide 225 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 244
encryption engines during, 188 field replaceable unit See FRU firmware download considerations, 166 frame redirection creating and enabling in an FCR configuration (edge to edge), 161 deploying the encryption switch or blade to hosts and targets, 118 enabling, 118 interop matrix, 221 prerequesites - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 245
, 130 force-enabling for encryption, M manual command, --manual_rekey, 148 manual re NetWorker labeling, 138 NS-based transparent frame redirection interop LUN re-keying, 147 privileges, user, 15 R redirection zones, 175 LUN, 146 initiating a manual session, 148 modes, 146 replace commands --replace - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 246
195 general errors related to the Configure Switch Encryption wizard, 203 management application wizard, 200 nsshow command, 195 supportsave command, 195 troubleshooting examples using the CLI, 198 turn off compression on extension switches, 176 turn off host-based encryption, 176 U user privileges - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 247
Z zeroize command --zeroize, 106 zeroizing effects of using on encryption engine, 72 zone creating an initiator-target using the CLI, 118 Fabric OS Encryption Administrator's Guide 229 53-1001864-01 - HP 8/24 | Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 248
230 Fabric OS Encryption Administrator's Guide 53-1001864-01

53-1001864-01
March 30, 2010
®
53-1001864-01
Fabric OS Encryption
Administrator’s Guide
Supporting Fabric OS v6.4.0, Supporting HP StorageWorks Secure Key
Manager (SKM) Environments