Cisco CP-7965G Administration Guide - Page 28
Establishing and Identifying Secure Conference Calls, Call Security Interactions and Restrictions
 |
View all Cisco CP-7965G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 28 highlights
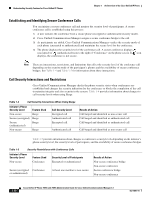
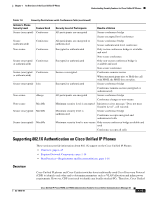
Understanding Security Features for Cisco Unified IP Phones Chapter 1 An Overview of the Cisco Unified IP Phone Establishing and Identifying Secure Conference Calls You can initiate a secure conference call and monitor the security level of participants. A secure conference call is established using this process: 1. A user initiates the conference from a secure phone (encrypted or authenticated security mode). 2. Cisco Unified Communications Manager assigns a secure conference bridge to the call. 3. As participants are added, Cisco Unified Communications Manager verifies the security mode of each phone (encrypted or authenticated) and maintains the secure level for the conference. 4. The phone displays the security level of the conference call. A secure conference displays (encrypted) or (authenticated) icon to the right of "Conference" on the phone screen. If icon displays, the conference is not secure. Note There are interactions, restrictions, and limitations that affect the security level of the conference call depending on the security mode of the participant's phones and the availability of secure conference bridges. See Table 1-4 and Table 1-5 for information about these interactions. Call Security Interactions and Restrictions Cisco Unified Communications Manager checks the phone security status when conferences are established and changes the security indication for the conference or blocks the completion of the call to maintain integrity and also security in the system. Table 1-4 provides information about changes to call security levels when using Barge. Table 1-4 Call Security Interactions When Using Barge Initiator's Phone Security Level Feature Used Non-secure Barge Secure (encrypted) Barge Secure (authenticated) Barge Non-secure Barge Call Security Level Encrypted call Authenticated call Encrypted call Authenticated call Results of Action Call barged and identified as non-secure call Call barged and identified as authenticated call Call barged and identified as authenticated call Call barged and identified as non-secure call Table 1-5 provides information about changes to conference security levels depending on the initiator's phone security level, the security levels of participants, and the availability of secure conference bridges. Table 1-5 Security Restrictions with Conference Calls Initiator's Phone Security Level Non-secure Feature Used Conference Security Level of Participants Encrypted or authenticated Secure (encrypted Conference or authenticated) At least one member is non-secure Results of Action Non-secure conference bridge Non-secure conference Secure conference bridge Non-secure conference 1-14 Cisco Unified IP Phone 7965G and 7945G Administration Guide for Cisco Unified Communications Manager 6.1 OL-14641-01