HP 1606 Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864-01, June - Page 214
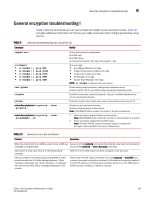
TABLE 10, General encryption troubleshooting I, General errors and conditions
 |
View all HP 1606 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 214 highlights
6 General encryption troubleshooting I TABLE 10 Problem General errors and conditions Resolution LUN state for some LUNS remains in "initialize" state on the passive path. This is expected behavior. The LUNs exposed through Passive paths of the target array will be in either Initialize or LUN Discovery Complete state so long as the paths remain n passive condition. When the passive path becomes active, the LUN changes to Encryption Enabled. Use the --show -LUN command with the -stat option to check the LUN state. A backup fails because the LUN is always in the initialize state for the tape container. Tape media is encrypted and gets a key which is archived in the key vault. The key is encrypted with a master key. At a later point in time you generate a new master key. You decide to use this tape media to back up other data. You rewind the tape, erase the tape, relabel the tape, and start a backup from the start of the tape. When the first command comes from the host, the key vault is queried for the tape media based on the media serial number. Since this tape media was used previously, the key is already present in the key vault for this media serial number but this key is encrypted with the old master key and that master key is not present in the switch. You cannot create a new key for this tape media because, per policy, there can be only one key per media. Use one of two resolutions: • Load the old master key on the switch at an alternate location. The key for the tape media can then be decrypted. • Delete the key for the tape media from the key vault. This forces the switch to create a new key for the tape media. Until you start the backup, the LUN remains in "initialize" state. "Invalid certificate" error message received when doing a KAC certificate exchange between the Brocade Encryption Switch and a key management system appliance. This error is due to the Brocade Encryption Switch time being ahead of the appliance time. Use one of two resolutions: • Change the appliance time to match the start period of the KAC certificate. • Change the Brocade Encryption Switch time to synchronize with the appliance time. Upon completion, regenerate the KAC certificate and then do another KAC certificate exchange with the appliance. "Temporarily out of resources" message received during re-key or first time encryption. Re-key or first time encryption sessions are pending due to resource unavailability. A maximum of twelve sessions including rekey (manual or auto) and first time encryption sessions are supported per encryption switch or blade and two sessions per target. The system checks once every hour to determine, if there are any re-key or first time encryption sessions pending. If resources are available, the next session in the queue is processed. There may be up to an hour lag before the next session in the queue is processed. It is therefore recommended that you do not schedule more than 12 re-key or first time encryption sessions. HA cluster creation fails with error, Create HA cluster status: The IO link IP address of the EE (online) is not configured, even though both the addresses are set and accessible. The IP addresses for the I/O link ports should be configured before enabling the EE. Failure to do so results in unsuccessful HA Cluster creation. If the IP addresses for these ports were configured after the EE is enabled, reboot the encryption switch or slotpoweroff/slotpoweron the encryption blade to sync up the IP address information to the EE. Re-keying fails with error "Disabled (Key not in sync)". cryptocfg --commit fails with message "Default zone set to all access at one of nodes in EG." Re-keying was started on a remote EE but the local EE is not capable of starting re-key because the key returned from key vault does not match with the Key ID used by remote EE. You will need to re-enable the LUN after the keys are synced between two key vaults properly using the needs to cryptocfg --discoverLUN command. Default zoning must be set to no access. 196 Fabric OS Encryption Administrator's Guide 53-1001864-01