HP StorageWorks 4/16 Brocade Fabric OS Command Reference Guide v6.1.0 (53-1000 - Page 633
SNMPv1 Configuration Parameters, Trap Recipient Severity Level, snmpadmin, snmpuser, authKey, privKey
 |
View all HP StorageWorks 4/16 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 633 highlights
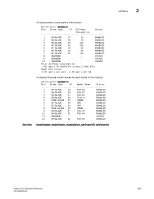
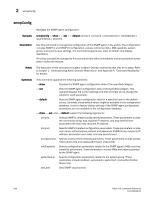
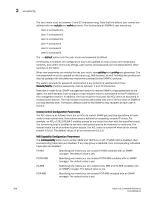
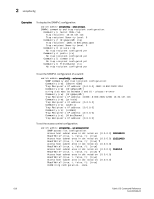
snmpConfig 2 SNMPv1 Configuration Parameters The agent supports six communities and associated trap recipients and trap recipient severity level supported. The first three communities are for read-write (rw) access and the last three are for read-only (ro) access. The default value for the trap recipient of each community is 0.0.0.0. The length of the community string should be in range of 2 to 16 characters. The default values for the community strings are: Community 1: Secret C0de Community 2: OrigEquipMfr Community 3: private Community 4: public Community 5: common Community 6: FibreChannel When FCS policy s enabled, community strings can be changed on the primary FCS switch only, and only the primary FCS switch propagates changes across the fabric. For an SNMP management station to receive a trap generated by the agent, the administrator must configure a trap recipient to correspond to the IP address of the management station. In addition, the trap recipient must be able to pass the access control list (ACL) check as described in the Access Control category. Trap Recipient Severity Level When an event occurs and its severity level is at or below the set value, the Event Trap traps (swEventTrap, connUnitEventTrap and swFabricWatchTrap), are sent to configured trap recipients. By default, this value is set at 0, implying that no Event Trap is sent. Possible values are 0 None 1 Critical 2 Error 3 Warning 4 Informational 5 Debug SNMPv3 Configuration Parameters Two user roles, snmpadmin and snmpuser are supported. snmpadmin provides read-write access and snmpuser provides read-only access. Entries are added to the USM table corresponding to each role. A total of three entries for snmpadmin and snmpuser respectively are supported. Separate default passwords are provided for creation of authKey and privKey for each entry. The default set of passwords is published and the default algorithm (MD5/SHA) is used to create the initial set of auth keys. You can change these passwords using this option. You have the option to select the authentication protocol MD5/SHA or no authentication for each entry. Select the following combination of protocols: NoAuth/NoPriv Auth/NoPriv Auth/Priv Fabric OS Command Reference 607 53-1000599-02