Kyocera ECOSYS FS-1320D Kyocera Command Center Operation Guide Rev 6.5.2012.7 - Page 60
Advanced > Security > IPSec > Rule1 (to Rule3), Data Protection IKE phase2
 |
View all Kyocera ECOSYS FS-1320D manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 60 highlights
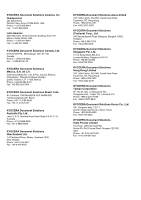
COMMAND CENTER Pages Shows whether the set rule is enabled or disabled. To enable or disable the rule, refer to Advanced > Security > IPSec > Rule1 (to Rule3) on page 3-53. Advanced > Security > IPSec > Rule1 (to Rule3) These pages allow you to select or edit rules to use for IPSec protocol-based communication. Rule Specifies whether or not to enable the selected IPSec policy rule. Select On to enable the rule. Select Off to disable it. Key Exchange (IKE phase1) When using IKE phase1, a secure connection with the other end is established by generating ISAKMP SAs. Configure the following items so that they meet the requirement of the other end. • Mode Main Mode protects identifications but requires more messages to be exchanged with the other end. Aggressive Mode requires fewer messages to be exchanged with the other end than Main Mode but restricts identification protection and narrows the extent of the parameter negotiations. When Aggressive Mode is selected and Preshared is selected for Authentication Type, only host addresses can be specified for IP addresses of the rule. • Hash Selects the hash algorithm. • Encryption Selects the encryption algorithm. • Diffie-Hellman Group The Diffie-Hellman key-sharing algorithm allows two hosts on an unsecured network to share a private key securely. Select the Diffie-Hellman group to use for key sharing. • Lifetime (Time) Specifies the lifetime of an ISAKMP SA in seconds. Data Protection (IKE phase2) In IKE phase2, IPSec SAs such as AH or ESP are established by using SAs established in IKE phase1. Configure the following items so that they meet the requirement of the other end. • Protocol Select ESP or AH for the protocol. ESP protects the privacy and integrity of the packet contents. Select the hash algorithm and encryption algorithm below. AH protects the integrity of the packet contents using encryption checksum. Select the hash algorithm below. • Hash Selects the hash algorithm. • Encryption Selects the encryption algorithm. (When ESP is selected under Protocol.) • PFS When PFS is set to On (enabled), even if a key is decrypted, the decrypted key cannot be used to decrypt the other keys generated after the decryption. 3-53 User Guide