Asus X50SR User Manual - Page 48
Trusted Platform Module (TPM) (on selected models), TPM Applications
 |
View all Asus X50SR manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 48 highlights
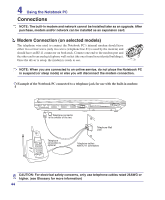
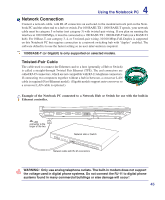
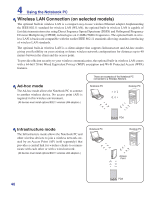
4 Using the Notebook PC Trusted Platform Module (TPM) (on selected models) The TPM, or Trusted Platform Module, is a security hardware device on the system board that will hold computer-generated keys for encryption. It is a hardware-based solution that an help avoid attacks by hackers looking to capture passwords and encryption keys to sensitive data. The TPM provides the ability to the PC or notebook to run applications more secure and to make transactions and communication more trustworthy. The security features provided by the TPM are internally supported by the following cryptographic capabilities of each TPM: hashing, random number generation, asymmetric key generation, and asymmetric encryption/decryption. Each individual TPM on each individual computer system has a unique signature initialized during the silicon manufacturing process that further enhances its trust/security effectiveness. Each individual TPM must have an Owner before it is useful as a security device. TPM Applications TPM is useful for any customer that is interested in providing an addition layer of security to the computer system. The TPM, when bundled with an optional security software package, can provide overall system security, file protection capabilities and protect against email/privacy concerns. TPM helps provide security that can be stronger than that contained in the system BIOS, operating system, or any non-TPM application. Note: The TPM is disabled by default. Use BIOS setup to enable it. Important: Use your TPM application's "Restore" or "Migration" function to backup your TPM security data. You can launch the Security Platform application from Windows "Control Panel". You can launch the Security Platform application from Windows "Start" menu. When the Security Platform is running, this icon will show in the Windows taskbar. You can choose to initialize or manage here. 48 When you launch the Security Platform application for the first time, answer Yes and follow the instructions to configure it.