Compaq Armada e500 Wireless Security - Page 14
Symmetric Key vs Public Key
 |
View all Compaq Armada e500 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 14 highlights
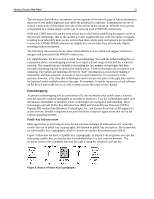
Wireless Security White Paper 14 Core elements of a PKI are: • Asymmetric keys • Digital certificates • Digital signatures The following paragraphs describe and illustrate these elements. A "key" is a numeric value of variable length that an encryption algorithm uses to convert unencrypted text into encrypted text. Public key cryptography uses a pair of asymmetric keys for encryption and decryption. An "asymmetric" key system uses a different key for encryption and decryption. (By contrast, a "symmetric" key system uses the same key for encryption and decryption.) Each pair of keys in an asymmetric key system consists of a public key and a private key. The public key is distributed widely. The private key is always kept secret. Data encrypted with the public key can be decrypted only with the private key. Conversely, data encrypted with the private key can be decrypted only with the public key. Most asymmetric encryption uses the RSA algorithm developed in 1977 by Rivest, Shamir, and Adleman, or derivatives of that algorithm. Figure 6 illustrates symmetric and asymmetric keys. Symmetric Key vs Public Key Symmetric key (shared secret) systems Same key used for encryption and decryption Public key systems private key public key Different keys for encryption and decryption Figure 6: Symmetric and Asymmetric Keys