Compaq ProLiant 4000 Compaq Enterprise Security Framework - Page 19
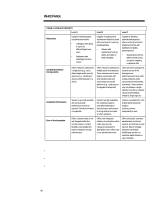
TABLE 3: LEVELS OF SECURITY, Level A, Level B, Level C, Robustness, Comprehensiveness,
 |
View all Compaq ProLiant 4000 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 19 highlights
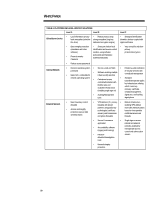
WHITE PAPER (cont.) ... TABLE 3: LEVELS OF SECURITY Level A Level B Level C Robustness Capable of deterring basic, unsophisticated attacks: • Colleagues attempting to log-on as different/higher level users • Employees who unwittingly introduce viruses Capable of repelling more sophisticated attacks by those with some level of computing power/expertise: • Attacker with sophisticated hacking utilities and ability to break encryption Capable of defeating sophisticated/organized attacks uniformly across the enterprise by those with significant computing power/expertise: • Organizations with the ability to break strong encryption, targeting competitive data Comprehensiveness/ Interoperability Offers measures addressed to a single point (e.g., log-in, data storage) and/or security objective (e.g., identification access control) typically on a device. Offers measures addressed to multiple points and objectives. These measures are to some degree interoperable with other solutions and work across many (but not all) platforms (e.g., single sign on for segment of enterprise). Offers pervasive package that functions across all the heterogeneous platforms/environments within a large enterprise and/or across Externet environment, seamlessly. These solutions may only address a single objective, but offer a complete solution (Externet/large enterprise single sign-on). Availability/ Performance Solution is generally available with some periodic maintenance and set-up required. Overall performance is acceptable. Solution has high availability, but sometimes requires scheduled maintenance. Security feature performance is strong and has no impact on other operations. Solution is available 24x7 with limited maintenance time required. Solution performs transparently to user. Ease of Use/Integration Offers a solution which is not well integrated with other security solutions. Limited flexibility and management tools for enterprise security administrators. Offers more integrated solutions for enterprises which make many security measures transparent to appropriate users. Offers easy to use administration tools. Offers centralized, seamless administration for internal network, and Externet security services. Easy to manage; Enterprise can flexibly build/change solutions to meet their needs. Based on open standards. In practice, several solution sets fit into each level and across devices and networks. However, certain types of solutions characterize each security level. For example: • Level A solutions are primarily concerned with achieving basic security through stringent access control to local devices, and basic boundary protection for the network. • Level B solutions require greater levels of authentication and authorization control locally, and centralized security services for the internal network. • Level C solutions enable secure Externet applications and communications with advanced external network functionality. Level C also contains robust security at the boundary of and inside the corporate network. Higher security levels primarily operate as network services. Table 4 details at what platforms and levels specific solutions operate: 19