| Section |
Page |
| Contents |
3 |
| Supported Fabric OS 6.x HP StorageWorks hardware |
19 |
| Table 1 Switch model naming matrix |
19 |
| Intended audience |
20 |
| Related documentation |
20 |
| Document conventions and symbols |
20 |
| Table 2 Document conventions |
20 |
| Rack stability |
21 |
| HP technical support |
21 |
| Customer self repair |
21 |
| Product warranties |
21 |
| Subscription service |
22 |
| HP websites |
22 |
| Documentation feedback |
22 |
| Standard features |
23 |
| Overview |
23 |
| Using the CLI |
23 |
| Connecting to the CLI |
24 |
| Using Telnet or SSH session |
24 |
| Using a console session on the serial port |
25 |
| Changing passwords |
25 |
| Table 3 Default administrative account names and passwords |
26 |
| Changing default account passwords at login |
26 |
| Configuring the Ethernet interface |
27 |
| Displaying the network interface settings |
27 |
| Setting static Ethernet addresses |
28 |
| Configuring DHCP |
29 |
| Enabling DHCP |
29 |
| Disabling DHCP |
29 |
| Setting the date and time |
30 |
| Setting time zones |
30 |
| Synchronizing local time using NTP |
32 |
| Customizing switch names |
33 |
| Working with Domain IDs |
33 |
| Licensed features |
34 |
| Generating a license key |
35 |
| Activating a license key |
35 |
| Removing a licensed feature |
36 |
| Features and required licenses |
37 |
| Table 4 License requirements |
37 |
| Inter-Chassis Link (ICL) licensing |
38 |
| Time-based licenses |
39 |
| High Availability considerations |
39 |
| Firmware upgrade and downgrade consideration |
39 |
| Configupload and Configdownload considerations |
39 |
| Expired licenses |
39 |
| Ports on Demand (POD) licensing |
39 |
| Activating POD |
40 |
| Configuring Dynamic Ports on Demand |
40 |
| How ports are assigned to licenses |
40 |
| Displaying the port license assignment |
41 |
| Activating Dynamic Ports on Demand |
41 |
| Disabling Dynamic Ports on Demand |
42 |
| Managing POD licenses |
42 |
| Reserving a license |
42 |
| Releasing a port |
43 |
| Disabling and enabling switches |
44 |
| Disabling and enabling ports |
44 |
| Making basic connections |
45 |
| Connecting to devices |
45 |
| Connecting to other switches |
45 |
| Linking through a gateway |
45 |
| Checking status |
46 |
| Tracking and controlling switch changes |
48 |
| Configuring the audit log |
50 |
| Auditable event classes |
51 |
| Table 5 AuditCfg event class operands |
51 |
| Shutting down switches and Directors |
53 |
| High Availability of daemon processes |
53 |
| Table 6 Daemons that are automatically restarted |
54 |
| Managing user accounts |
55 |
| Overview |
55 |
| Accessing the management channel |
55 |
| Table 7 Maximum number of simultaneous sessions |
55 |
| Using Role-Based Access Control (RBAC) |
56 |
| Table 8 Fabric OS 6.x roles |
56 |
| Role permissions |
57 |
| Table 9 Permission types |
57 |
| Table 10 RBAC permissions matrix |
57 |
| Managing the local database user accounts |
59 |
| About the default accounts |
59 |
| Table 11 Default local user accounts |
59 |
| Defining local user accounts |
59 |
| Recovering accounts |
62 |
| Changing local account passwords |
62 |
| Configuring the local user database |
63 |
| Distributing the local user database |
63 |
| Protecting the local user database from distributions |
63 |
| Configuring password policies |
64 |
| Setting the password strength policy |
64 |
| Setting the password history policy |
65 |
| Setting the password expiration policy |
65 |
| Upgrade and downgrade considerations |
66 |
| Setting the account lockout policy |
66 |
| Denial of service implications |
67 |
| Authentication model |
67 |
| Table 12 Authentication configuration options |
68 |
| Creating Fabric OS user accounts |
69 |
| Table 13 Syntax for VSA-based account roles |
69 |
| Managing Fabric OS users on the RADIUS server |
70 |
| Windows 2000 IAS |
70 |
| Linux FreeRadius server |
71 |
| Table 14 dictionary.brocade file entries |
71 |
| RADIUS configuration and Admin Domains |
71 |
| Configuring the RADIUS server |
72 |
| Linux |
72 |
| Windows 2000 |
73 |
| LDAP configuration and Microsoft’s Active Directory |
75 |
| Configuring authentication servers on the switch |
77 |
| Enabling and disabling local authentication as backup |
80 |
| Boot PROM password |
80 |
| Setting the boot PROM password with a recovery string |
81 |
| HP StorageWorks 4/8 or 4/16, Brocade 4Gb SAN Switch for HP p-Class BladeSystem, Brocade 4Gb SAN Switch for HP c-Class BladeSystem, SAN Switch 4/32, 4/64 SAN Switch, SAN Switch 4/32B, 400 Multi-protocal (MP) Router |
81 |
| 4/256 SAN Director and DC SAN Backbone Director (short name, DC Director) |
82 |
| Setting the boot PROM password without a recovery string |
83 |
| HP StorageWorks 4/8 or 4/16, Brocade 4Gb SAN Switch for HP p-Class BladeSystem, Brocade 4Gb SAN Switch for HP c-Class BladeSystem, SAN Switch 4/32, 4/64 SAN Switch, SAN Switch 4/32B, 400 Multi-protocal (MP) Router |
83 |
| 4/256 SAN Director and DC SAN Backbone Director (short name, DC Director) |
83 |
| Recovering forgotten passwords |
84 |
| Configuring standard security features |
85 |
| Secure protocols |
85 |
| Table 15 Secure protocol support |
85 |
| Table 16 Items needed to deploy secure protocols |
85 |
| Table 17 Main security scenarios |
86 |
| Ensuring network security |
86 |
| Configuring the Telnet protocol |
87 |
| Blocking Telnet |
87 |
| Unblocking Telnet |
87 |
| Blocking listeners |
88 |
| Table 18 Blocked listener applications |
88 |
| Accessing switches and fabrics |
88 |
| Table 19 Access defaults |
88 |
| Port configuration |
89 |
| Configuring for the SSL protocol |
89 |
| Browser and Java support |
89 |
| Summary of SSL procedures |
90 |
| Table 20 SSL certificate files |
90 |
| Choosing a CA |
90 |
| Generating a public/private key |
90 |
| Generating and storing a CSR |
91 |
| Obtaining certificates |
91 |
| Installing a switch certificate |
92 |
| Activating a switch certificate |
92 |
| Configuring the browser |
93 |
| Installing a root certificate to the Java plug-in |
93 |
| Displaying and deleting certificates |
94 |
| Table 21 Commands for displaying and deleting SSL certificates |
94 |
| Troubleshooting certificates |
94 |
| Table 22 SSL messages and actions |
94 |
| Configuring for SNMP |
95 |
| Setting the security level |
95 |
| Using the snmpConfig command |
96 |
| Configuring secure file copy |
98 |
| Configuring advanced security features |
99 |
| About access control list (ACL) policies |
99 |
| How the ACL policies are stored |
99 |
| Table 23 Security database size restrictions |
99 |
| Identifying policy members |
100 |
| Table 24 Valid methods for specifying policy members |
100 |
| Configuring ACL policies |
100 |
| Displaying ACL policies |
101 |
| Configuring an FCS policy |
101 |
| Table 25 FCS policy states |
101 |
| FCS policy restrictions |
102 |
| Table 26 Switch operations |
102 |
| Overview of steps to create and manage the FCS policies |
103 |
| Modifying the Primary FCS |
103 |
| Distributing an FCS policy |
104 |
| Table 27 Distribution policy states |
105 |
| Configuring a DCC policy |
105 |
| Table 28 DCC policy states |
105 |
| DCC policy restrictions |
105 |
| Creating a DCC policy |
106 |
| Examples of creating DCC policies |
107 |
| Creating an SCC policy |
107 |
| Table 29 SCC policy states |
107 |
| Saving changes to ACL policies |
108 |
| Activating changes to ACL policies |
108 |
| Adding a member to an existing policy |
108 |
| Removing a member from an ACL policy |
109 |
| Deleting an ACL policy |
109 |
| Aborting all uncommitted changes |
109 |
| Configuring the authentication policy for fabric elements |
109 |
| Figure 1 DH-CHAP authentication |
110 |
| E_Port authentication |
110 |
| Device authentication policy |
112 |
| Auth policy restrictions |
112 |
| Supported configurations |
112 |
| Selecting authentication protocols |
113 |
| Re-authenticating ports |
113 |
| Managing secret key pairs |
114 |
| Fabric wide distribution of the Auth policy |
115 |
| Accept distributions configuration parameter |
116 |
| IP Filter policy |
116 |
| Creating an IP Filter policy |
116 |
| Cloning an IP Filter policy |
116 |
| Displaying an IP Filter policy |
117 |
| Saving an IP Filter policy |
117 |
| Activating an IP Filter policy |
117 |
| Deleting an IP Filter policy |
118 |
| IP Filter policy rules |
118 |
| Table 30 Supported services |
118 |
| Table 31 Implicit IP Filter rules |
119 |
| Table 32 Default IP policy rules |
119 |
| IP Filter policy enforcement |
119 |
| Creating IP Filter policy rules |
120 |
| Deleting IP Filter policy rules |
120 |
| Aborting a switch session transaction |
120 |
| IP Filter policy distributions |
121 |
| IP Filter policy restrictions |
121 |
| Distributing the policy database |
121 |
| Table 33 Interaction between fabric-wide consistency policy and distribution settings |
122 |
| Configuring the database distribution settings |
122 |
| Table 34 Supported policy databases |
122 |
| Distributing ACL policies to other switches |
123 |
| Table 35 ACL policy database distribution behavior |
124 |
| Setting the consistency policy fabric-wide |
124 |
| Table 36 Fabric-wide consistency policy settings |
124 |
| Notes on joining a switch to the fabric |
125 |
| Matching fabric-wide consistency policies |
126 |
| Table 37 Merging fabrics with matching fabric-wide consistency policies |
126 |
| Non-matching fabric-wide consistency policies |
127 |
| Table 38 Examples of strict fabric merges |
127 |
| Table 39 Fabric merges with tolerant/absent combinations |
127 |
| FIPS support |
127 |
| Zeroization functions |
128 |
| Table 40 Zeroization behavior |
128 |
| Power-up self tests |
128 |
| Conditional tests |
129 |
| FIPS mode |
130 |
| Table 41 FIPS mode restrictions |
130 |
| Preparing the switch for FIPS |
131 |
| Overview of steps |
131 |
| Maintaining configurations |
135 |
| Maintaining consistent configuration settings |
135 |
| Displaying configuration settings |
135 |
| Backing up a configuration |
135 |
| Troubleshooting configuration upload |
136 |
| Restoring switch information |
137 |
| Table 42 CLI commands to display switch configuration information |
137 |
| Restoring a configuration |
137 |
| Configuration download without disabling a switch |
137 |
| Security considerations |
139 |
| Troubleshooting configuration download |
139 |
| Messages captured in the logs |
140 |
| Restoring configurations in a FICON environment |
140 |
| Table 43 Backup and restore in a FICON CUP environment |
140 |
| Downloading configurations across a fabric |
140 |
| Configuration form |
141 |
| Table 44 Configuration and connection information |
141 |
| Managing administrative domains |
143 |
| Figure 2 Fabric with two Admin Domains |
144 |
| Figure 3 Filtered fabric views |
144 |
| Admin Domain features |
145 |
| Requirements for Admin Domains |
145 |
| User-defined Administrative Domains |
145 |
| System-defined Administrative Domains |
145 |
| AD0 |
146 |
| AD255 |
146 |
| Figure 4 Fabric with AD0 and AD255 |
147 |
| Admin Domain access levels |
147 |
| Table 45 AD user types |
147 |
| Admin Domains and login |
148 |
| Admin Domain member types |
148 |
| Device members |
148 |
| Switch port members |
149 |
| Switch members |
149 |
| Admin Domains and switch WWN |
149 |
| Figure 5 Fabric showing switch and device WWNs |
150 |
| Figure 6 Filtered fabric views showing converted switch WWNs |
150 |
| Admin Domain compatibility and availability |
150 |
| Admin Domains and merging |
150 |
| Compatibility |
151 |
| Figure 7 Isolated subfabrics |
151 |
| Firmware upgrade and downgrade scenarios |
151 |
| Managing Admin Domains |
151 |
| Understanding the AD transaction model |
152 |
| Implementing Admin Domains |
152 |
| Creating an Admin Domain |
153 |
| Assigning a user to an Admin Domain |
154 |
| Activating and deactivating Admin Domains |
155 |
| Adding and removing Admin Domain members |
156 |
| Renaming an Admin Domain |
156 |
| Deleting an Admin Domain |
157 |
| Deleting all user-defined Admin Domains |
157 |
| Validating an Admin Domain member list |
158 |
| Using Admin Domains |
158 |
| Using CLI commands in an AD context |
158 |
| Table 46 Ports and devices in CLI output |
159 |
| Executing a command in a different AD context |
159 |
| Displaying an Admin Domain configuration |
159 |
| Switching to a different Admin Domain context |
160 |
| Performing zone validation |
160 |
| Admin Domain interactions |
160 |
| Table 47 Admin Domain interaction with Fabric OS features |
161 |
| Admin Domains, zones, and zone databases |
162 |
| Admin Domains and LSAN zones |
162 |
| Configuration upload and download in an AD context |
163 |
| Table 48 Configuration upload and download scenarios in an AD context |
163 |
| Installing and maintaining firmware |
165 |
| About the firmware download process |
165 |
| Upgrading and downgrading firmware |
166 |
| Effects of firmware changes on accounts and passwords |
166 |
| Table 49 Effects of firmware changes on accounts and passwords |
166 |
| Considerations for FICON CUP environments |
166 |
| Preparing for firmware downloads |
167 |
| Checking connected switches |
168 |
| Table 50 Recommended firmware |
168 |
| Obtaining and decompressing firmware |
169 |
| Performing firmwareDownload on switches |
169 |
| Overview of the firmware download process on switches |
169 |
| HP StorageWorks 4/8 SAN Switch, 4/16 SAN Switch, Brocade 4Gb SAN Switch for HP p-Class BladeSystem, Brocade 4Gb SAN Switch for HP c-Class BladeSystem, SAN Switch 4/32, 4/64 SAN Switch, SAN Switch 4/32B, 400 MP Router, and firmware download |
170 |
| Downloading firmware to a Director |
171 |
| Overview of the firmware download process on directors |
172 |
| 4/256 SAN Director and DC Director firmwareDownload procedure |
172 |
| Director restrictions for downgrading |
175 |
| firmwaredownload from a USB device |
176 |
| FIPS Support |
177 |
| Public and private key management |
177 |
| The firmwareDownload command |
178 |
| Power-on firmware checksum test |
179 |
| Testing and restoring firmware on switches |
179 |
| Testing and restoring firmware on directors |
180 |
| Validating firmwareDownload |
183 |
| Troubleshooting firmwareDownload |
184 |
| Considerations for downgrading firmware to Fabric OS 5.3.0 or earlier |
184 |
| Preinstallation messages |
185 |
| Blade troubleshooting tips |
191 |
| Configuring Directors |
193 |
| Changing a Director’s name |
193 |
| Identifying ports |
193 |
| Director port numbering schemes |
194 |
| Table 51 Port numbering schemes for the 4/256 Director and DC Director |
194 |
| By slot and port number |
194 |
| By port area ID |
194 |
| By index |
194 |
| Table 52 Default index/area_ID core PID assignment with no port swap |
195 |
| Basic blade management |
196 |
| Powering port blades off and on |
196 |
| Disabling and enabling port blades |
197 |
| FR4-18i blade exceptions |
197 |
| FC4-48 and FC8-48 blade exceptions |
198 |
| Conserving power |
198 |
| Blade terminology and compatibility |
199 |
| Table 53 Director terminology and abbreviations |
199 |
| CP blades |
199 |
| Core blades |
200 |
| Port blade compatibility |
200 |
| Table 54 Port blades supported by each Director |
200 |
| Setting chassis configuration options for the 4/256 Director |
200 |
| Table 55 Supported configuration options |
200 |
| Table 56 Chassis configuration options |
201 |
| Obtaining slot information |
201 |
| Routing traffic |
203 |
| About data routing and routing policies |
203 |
| Specifying the routing policy |
203 |
| Assigning a static route |
204 |
| Specifying frame order delivery |
204 |
| Using dynamic load sharing |
205 |
| Viewing routing path information |
206 |
| Viewing routing information along a path |
208 |
| Using the FC-FC routing service |
211 |
| Supported platforms |
211 |
| Supported configurations |
211 |
| Fibre Channel routing concepts |
211 |
| Figure 8 A metaSAN with interfabric links |
212 |
| Figure 9 A metaSAN with edge-to-edge and backbone fabrics |
213 |
| Figure 10 Edge SANs connected through a backbone fabric |
214 |
| Proxy devices |
214 |
| Figure 11 MetaSAN with imported devices |
215 |
| Routing types |
215 |
| Fibre Channel NAT and phantom domains |
215 |
| Setting up the FC-FC routing service |
216 |
| Performing verification checks |
217 |
| Assigning backbone fabric IDs |
218 |
| Configuring FCIP tunnels (optional) |
219 |
| Configuring FC-FC routing to work with Secure Fabric OS (optional) |
219 |
| Configuring DH-CHAP secret |
220 |
| Configuring an interfabric link |
221 |
| portCfgExport options |
223 |
| Configuring the FC router port cost (optional) |
226 |
| Using router port cost |
227 |
| Upgrade, downgrade, and HA considerations |
227 |
| Port cost considerations |
228 |
| Setting a proxy PID |
228 |
| Matching fabric parameters |
228 |
| Configuring EX_Port frame trunking (optional) |
229 |
| Supported configurations and platforms |
230 |
| High Availability support |
230 |
| Backward compatibility support |
230 |
| Using EX_Port frame trunking |
230 |
| Security considerations |
230 |
| Trunking commands |
230 |
| Configuring LSANs and zoning |
231 |
| Use of administrative domains with LSAN zones and FCR |
231 |
| Defining and naming zones |
232 |
| LSAN zones and fabric-to-fabric communications |
232 |
| LSAN zone binding (optional) |
235 |
| Dual backbone configuration |
236 |
| Maximum LSAN count |
236 |
| Configuring backbone fabrics for interconnectivity |
237 |
| HA and downgrade considerations |
237 |
| IPFC over FCR |
237 |
| Broadcast configuration |
238 |
| Monitoring resources |
239 |
| Routing ECHO |
240 |
| Upgrade and downgrade considerations |
241 |
| Interoperability with legacy FCR switches |
241 |
| Backward compatibility |
242 |
| Table 57 Hardware and firmware compatibility for nonsecure fabrics |
242 |
| Front domain consolidation |
242 |
| Using front domain consolidation |
242 |
| Range of output ports |
243 |
| Interoperating with an M-EOS fabric |
245 |
| Table 58 Brocade-McDATA M-EOSc interoperability compatibility matrix |
245 |
| Table 59 Brocade-McDATA M-EOSn interoperability compatibility matrix |
246 |
| McDATA Mi10K interoperability |
246 |
| Configuring the fabrics for interconnectivity |
247 |
| Connectivity modes |
248 |
| Table 60 portCfgExPort -m values |
248 |
| Configuring the FC router |
248 |
| Figure 12 EFCM SAN status |
251 |
| Configuring M-EOS for interconnection |
251 |
| Figure 13 SAN Pilot and EFCM Zone screens |
252 |
| Figure 14 Adding a zone set name in SAN Pilot |
254 |
| LSAN zoning with M-EOS |
254 |
| Completing the configuration |
255 |
| Migrating from an MP Router to a 400 MP Router |
257 |
| Configurations |
257 |
| Non-redundant configuration |
257 |
| Figure 15 Non-redundant router configuration |
257 |
| Figure 16 Configuration during the upgrade |
258 |
| Redundant configuration |
258 |
| Figure 17 Redundant router configuration |
258 |
| Dual backbone configuration |
258 |
| Figure 18 Dual backbone fabric configuration |
259 |
| Devices directly connected to router |
259 |
| Administering FICON fabrics |
261 |
| Overview of Fabric OS support for FICON |
261 |
| Supported switches |
262 |
| Types of FICON configurations |
262 |
| Control Unit Port (CUP) |
262 |
| FICON commands |
263 |
| Table 61 Fabric OS commands related to FICON and FICON CUP |
263 |
| User security considerations |
264 |
| Configuring switches |
264 |
| Preparing a switch |
265 |
| Configuring a single switch |
265 |
| Configuring a high-integrity fabric |
265 |
| Figure 19 Cascaded configuration, two switches |
266 |
| Figure 20 Cascaded configuration, three switches |
266 |
| Setting a unique Domain ID |
266 |
| Displaying information |
267 |
| Link incidents |
267 |
| Registered listeners |
267 |
| Node identification data |
267 |
| FRU failures |
267 |
| Swapping ports |
268 |
| Clearing the FICON management database |
268 |
| Using FICON CUP |
268 |
| Setup summary |
269 |
| Enabling and disabling FICON Management Server mode |
269 |
| Setting up CUP when FICON Management Server mode is enabled |
270 |
| Displaying the fmsmode setting |
270 |
| Displaying mode register bit settings |
271 |
| Table 62 FICON CUP mode register bits |
271 |
| Setting mode register bits |
272 |
| Persistently enabling/disabling ports |
272 |
| Port and switch naming standards |
273 |
| Adding and removing FICON CUP licenses |
273 |
| Zoning and PDCM considerations |
273 |
| Zoning and link incident reporting |
273 |
| Troubleshooting |
274 |
| Identifying ports |
274 |
| Backing up and restoring FICON configuration files |
275 |
| Recording configuration information |
276 |
| Table 63 FICON configuration worksheet |
276 |
| Sample IOCP configuration file |
277 |
| Administering Extended Fabrics |
363 |
| Extended Fabrics licensing |
363 |
| Extended Fibre Channel over distance |
363 |
| Distance levels for extended Inter-Switch Links (ISLs) |
363 |
| Buffer-to-Buffer Credits |
363 |
| Table 80 Fibre Channel data frames |
364 |
| FC switch port Buffer Credit requirements for long distance calculations |
365 |
| Determining how many ports can be configured for long distance |
365 |
| Displaying the remaining buffers in a port group |
366 |
| Table 81 Switch, port speed, and distance with ASIC and buffers |
368 |
| Fabric considerations |
369 |
| Long distance link initialization activation |
369 |
| Extended Fabrics device limitations |
369 |
| Configuring an extended ISL |
369 |
| Table 82 Extended ISL modes: B-Series 2Gb Switches (Bloom and Bloom II ASICs) |
371 |
| Administering Advanced Zoning |
383 |
| About zoning |
383 |
| Figure 31 Zoning example |
383 |
| Zone types |
384 |
| Table 84 Types of zoning |
384 |
| Table 85 Approaches to fabric-based zoning |
384 |
| Zone objects |
385 |
| Zoning schemes |
386 |
| Zone aliases |
386 |
| Zone configurations |
386 |
| Zoning enforcement |
387 |
| Software-enforced zoning |
387 |
| Hardware-enforced zoning |
387 |
| Table 86 Enforcing hardware zoning |
388 |
| Figure 32 Hardware-enforced nonoverlapping zones |
389 |
| Figure 33 Hardware-enforced overlapping zones |
389 |
| Figure 34 Zoning with hardware assist (mixed-port and WWN zones) |
389 |
| Figure 35 Session-based hard zoning |
390 |
| Considerations for zoning architecture |
390 |
| Table 87 Considerations for zoning architecture |
390 |
| Best practices for zoning |
391 |
| Broadcast zones |
391 |
| Supported switches for broadcast zones |
392 |
| Broadcast zones and Admin Domains |
392 |
| Figure 36 Broadcast zones and Admin Domains |
392 |
| Upgrade and downgrade considerations |
393 |
| High Availability considerations with broadcast zones |
393 |
| Loop devices and broadcast zones |
393 |
| Backward compatibility with pre-5.3.0 switches |
393 |
| Broadcast zones and default zoning |
393 |
| Creating and managing zone aliases |
394 |
| Creating and maintaining zones |
396 |
| Activating default zones |
399 |
| Merging zones |
400 |
| Table 88 Zoning database limitations |
400 |
| Table 89 Resulting database size: 0 to 96K |
401 |
| Table 90 Resulting database size: 96K to 128K |
401 |
| Table 91 Resulting database size: 128K to 256K |
402 |
| Table 92 Resulting database size: 256K to 1M |
402 |
| Creating and modifying zoning configurations |
404 |
| Maintaining zone objects |
407 |
| Managing zoning configurations in a fabric |
410 |
| Adding a new switch or fabric |
410 |
| Splitting a fabric |
412 |
| Using zoning to administer security |
412 |
| Resolving zone conflicts |
412 |
| Configuring the PID format |
463 |
| About PIDs and PID binding |
463 |
| Summary of PID formats |
463 |
| Impact of changing the fabric PID format |
464 |
| Host reboots |
464 |
| Static PID mapping errors |
464 |
| Changes to configuration data |
465 |
| Table 101 Effects of PID format changes on configurations |
465 |
| Selecting a PID format |
465 |
| Table 102 PID format recommendations for adding new switches |
466 |
| Evaluating the fabric |
466 |
| Planning the update procedure |
468 |
| Online update |
468 |
| Offline update |
469 |
| Hybrid update |
469 |
| Changing to core PID format |
469 |
| Converting port number to area ID |
470 |
| Figure 45 4/256 SAN Director with extended edge PID |
471 |
| Performing PID format changes |
472 |
| Basic procedure |
472 |
| HP/UX procedure |
473 |
| AIX procedure |
475 |
| Swapping port area IDs |
476 |
| Implementing an interoperable fabric |
477 |
| Overview |
477 |
| Understanding Brocade and McDATA interoperability |
477 |
| Determining McDATA-aware features |
477 |
| Table 103 McDATA-aware features |
477 |
| Determining McDATA-unaware features |
478 |
| Table 104 McDATA-unaware features |
478 |
| Supported Connectivity for Fabric 6.0 |
479 |
| Figure 46 Typical configuration |
479 |
| Feature support and interoperability |
479 |
| Table 105 Complete feature compatibility matrix |
479 |
| M-EOS 9.6.2 features supported in Fabric OS 6.0 |
481 |
| Port number offset |
481 |
| NPIV |
481 |
| Trunking |
482 |
| M-EOS 9.6.2 features not supported by Fabric OS 6.0 |
482 |
| Domain ID offset configuration |
482 |
| Diagnostic test differences |
482 |
| Optional 6.0 licensing |
482 |
| Table 106 Supported optional features |
482 |
| Table 107 Unsupported features |
483 |
| Supported switches |
483 |
| Table 108 Fabric OS Interoperability with M-EOS |
483 |
| Supported features McDATA Fabric mode (interopmode 2) |
484 |
| Supported features McDATA Open Fabric mode (interopmode 3) |
484 |
| Unsupported features McDATA Fabric and Open Fabric modes |
484 |
| McDATA Fabric mode configuration restrictions |
484 |
| McDATA Open Fabric mode configuration restrictions |
485 |
| Upgrade and downgrade restrictions |
485 |
| Zoning restrictions |
485 |
| Zone name restrictions |
486 |
| Activating zones in McDATA Fabric mode |
486 |
| Default zone |
486 |
| Safe zone |
487 |
| Activating zone configurations on a standalone switch |
487 |
| Activating zone configurations fabric-wide |
487 |
| Verifying the effective zone configuration |
487 |
| Moving to McDATA Open Fabric mode from earlier Fabric OS versions |
489 |
| Enabling McDATA Open Fabric mode |
489 |
| Enabling McDATA Fabric mode |
490 |
| Enabling Brocade Native mode |
491 |
| Enabling Fabric OS L2 SANtegrity (Fabric Binding) |
491 |
| FCR SANtegrity (Fabric Binding) |
492 |
| Enabling FCR Fabric Binding |
492 |
| Support for coordinated Hot Code Load |
493 |
| Supported configurations |
493 |
| Upgrade and downgrade considerations |
493 |
| Table 109 Hot Code upgrade considerations |
494 |
| Activating Hot Code Load |
494 |
| Understanding legacy password behavior |
495 |
| Password management information |
495 |
| Table 110 Account/password characteristics matrix |
495 |
| Password prompting behaviors |
496 |
| Table 111 Password prompting matrix |
496 |
| Password migration during firmware changes |
497 |
| Table 112 Password migration behavior during firmware upgrade/downgrade |
497 |
| Password recovery options |
497 |
| Table 113 Password recovery options |
497 |
| Using Remote Switch |
499 |
| About Remote Switch |
499 |
| Remote Switch capabilities |
499 |
| Using Remote Switch with a gateway |
499 |
| Zone merging scenarios |
501 |
| Table 114 Zone merging scenarios |
501 |
| Index |
505 |
| A |
505 |
| B |
506 |
| C |
506 |
| D |
507 |
| E |
508 |
| F |
508 |
| G |
509 |
| H |
509 |
| I |
509 |
| J |
509 |
| K |
510 |
| L |
510 |
| M |
510 |
| N |
510 |
| O |
510 |
| P |
510 |
| R |
511 |
| S |
512 |
| T |
513 |
| U |
513 |
| V |
514 |
| W |
514 |
| X |
514 |

 1
1 2
2 3
3 4
4 5
5 6
6 7
7 8
8 9
9 10
10 11
11 12
12 13
13 14
14 15
15 16
16 17
17 18
18 19
19 20
20 21
21 22
22 23
23 24
24 25
25 26
26 27
27 28
28 29
29 30
30 31
31 32
32 33
33 34
34 35
35 36
36 37
37 38
38 39
39 40
40 41
41 42
42 43
43 44
44 45
45 46
46 47
47 48
48 49
49 50
50 51
51 52
52 53
53 54
54 55
55 56
56 57
57 58
58 59
59 60
60 61
61 62
62 63
63 64
64 65
65 66
66 67
67 68
68 69
69 70
70 71
71 72
72 73
73 74
74 75
75 76
76 77
77 78
78 79
79 80
80 81
81 82
82 83
83 84
84 85
85 86
86 87
87 88
88 89
89 90
90 91
91 92
92 93
93 94
94 95
95 96
96 97
97 98
98 99
99 100
100 101
101 102
102 103
103 104
104 105
105 106
106 107
107 108
108 109
109 110
110 111
111 112
112 113
113 114
114 115
115 116
116 117
117 118
118 119
119 120
120 121
121 122
122 123
123 124
124 125
125 126
126 127
127 128
128 129
129 130
130 131
131 132
132 133
133 134
134 135
135 136
136 137
137 138
138 139
139 140
140 141
141 142
142 143
143 144
144 145
145 146
146 147
147 148
148 149
149 150
150 151
151 152
152 153
153 154
154 155
155 156
156 157
157 158
158 159
159 160
160 161
161 162
162 163
163 164
164 165
165 166
166 167
167 168
168 169
169 170
170 171
171 172
172 173
173 174
174 175
175 176
176 177
177 178
178 179
179 180
180 181
181 182
182 183
183 184
184 185
185 186
186 187
187 188
188 189
189 190
190 191
191 192
192 193
193 194
194 195
195 196
196 197
197 198
198 199
199 200
200 201
201 202
202 203
203 204
204 205
205 206
206 207
207 208
208 209
209 210
210 211
211 212
212 213
213 214
214 215
215 216
216 217
217 218
218 219
219 220
220 221
221 222
222 223
223 224
224 225
225 226
226 227
227 228
228 229
229 230
230 231
231 232
232 233
233 234
234 235
235 236
236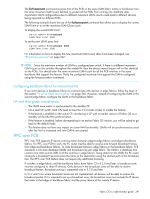 237
237 238
238 239
239 240
240 241
241 242
242 243
243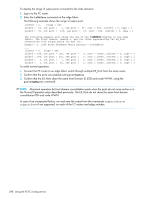 244
244 245
245 246
246 247
247 248
248 249
249 250
250 251
251 252
252 253
253 254
254 255
255 256
256 257
257 258
258 259
259 260
260 261
261 262
262 263
263 264
264 265
265 266
266 267
267 268
268 269
269 270
270 271
271 272
272 273
273 274
274 275
275 276
276 277
277 278
278 279
279 280
280 281
281 282
282 283
283 284
284 285
285 286
286 287
287 288
288 289
289 290
290 291
291 292
292 293
293 294
294 295
295 296
296 297
297 298
298 299
299 300
300 301
301 302
302 303
303 304
304 305
305 306
306 307
307 308
308 309
309 310
310 311
311 312
312 313
313 314
314 315
315 316
316 317
317 318
318 319
319 320
320 321
321 322
322 323
323 324
324 325
325 326
326 327
327 328
328 329
329 330
330 331
331 332
332 333
333 334
334 335
335 336
336 337
337 338
338 339
339 340
340 341
341 342
342 343
343 344
344 345
345 346
346 347
347 348
348 349
349 350
350 351
351 352
352 353
353 354
354 355
355 356
356 357
357 358
358 359
359 360
360 361
361 362
362 363
363 364
364 365
365 366
366 367
367 368
368 369
369 370
370 371
371 372
372 373
373 374
374 375
375 376
376 377
377 378
378 379
379 380
380 381
381 382
382 383
383 384
384 385
385 386
386 387
387 388
388 389
389 390
390 391
391 392
392 393
393 394
394 395
395 396
396 397
397 398
398 399
399 400
400 401
401 402
402 403
403 404
404 405
405 406
406 407
407 408
408 409
409 410
410 411
411 412
412 413
413 414
414 415
415 416
416 417
417 418
418 419
419 420
420 421
421 422
422 423
423 424
424 425
425 426
426 427
427 428
428 429
429 430
430 431
431 432
432 433
433 434
434 435
435 436
436 437
437 438
438 439
439 440
440 441
441 442
442 443
443 444
444 445
445 446
446 447
447 448
448 449
449 450
450 451
451 452
452 453
453 454
454 455
455 456
456 457
457 458
458 459
459 460
460 461
461 462
462 463
463 464
464 465
465 466
466 467
467 468
468 469
469 470
470 471
471 472
472 473
473 474
474 475
475 476
476 477
477 478
478 479
479 480
480 481
481 482
482 483
483 484
484 485
485 486
486 487
487 488
488 489
489 490
490 491
491 492
492 493
493 494
494 495
495 496
496 497
497 498
498 499
499 500
500 501
501 502
502 503
503 504
504 505
505 506
506 507
507 508
508 509
509 510
510 511
511 512
512 513
513 514
514


