HP Spectre XT TouchSmart Ultrabook 15-4010nr User Guide - Windows 8 - Page 82
Securing your computer and information, Using passwords
 |
View all HP Spectre XT TouchSmart Ultrabook 15-4010nr manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 82 highlights
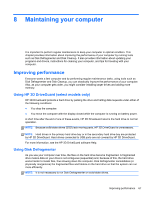
9 Securing your computer and information Computer security is essential for protecting the confidentiality, integrity, and availability of your information. Standard security solutions provided by the Windows operating system, HP applications, the non-Windows Setup Utility, or Basic Input/Output System (BIOS), and other third-party software can help protect your computer from a variety of risks, such as viruses, worms, and other types of malicious code. IMPORTANT: Some security features listed in this chapter may not be available on your computer. Computer risk Unauthorized use of the computer Computer viruses Unauthorized access to data Unauthorized access to Setup Utility (BIOS) settings and other system identification information Ongoing or future threats to the computer Unauthorized access to a Windows user account Unauthorized removal of the computer Security feature Power-on password Antivirus software Firewall software Administrator password Software updates User password Security cable lock Using passwords A password is a group of characters that you choose to secure your computer information and to protect online transactions. Several types of passwords can be set. For example, when you set up your computer for the first time, you were asked to create a user password to secure your computer. Additional passwords can be set in Windows or in the HP Setup Utility (BIOS) that is preinstalled on your computer. You may find it helpful to use the same password for a Setup Utility (BIOS) feature and for a Windows security feature. Use the following tips for creating and saving passwords: ● To reduce the risk of being locked out of the computer, record each password and store it in a secure place away from the computer. Do not store passwords in a file on the computer. ● When creating passwords, follow requirements set by the program. 72 Chapter 9 Securing your computer and information