HP StorageWorks 8/40 Brocade Fabric OS Administrator's Guide v6.3.0 (53-100133 - Page 194
IPsec policies, IPsec traffic selector, IPsec transform
 |
View all HP StorageWorks 8/40 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 194 highlights
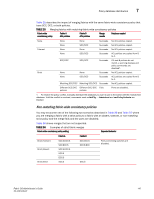
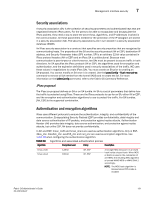
7 Management interface security TABLE 38 Algorithm Algorithms and associated authentication policies Encryption Level Policy Description 3des_cbc 168-bit ESP blowfish_cbc 64-bit ESP aes128_cbc 128-bit ESP aes256_cbc 256-bit ESP null_enc n/a ESP Triple DES is a more secure variant of DES. It uses three different 56-bit keys to encrypt blocks of 64-bit plain text. The algorithm is FIPS-approved for use by Federal agencies. Blowfish is a 32-bit to 448-bit keyed, symmetric block cipher. Advanced Encryption Standard is a 128- or 256-bit fixed block size cipher. A form of plaintext encryption. IPsec policies An IPsec policy determines the security services afforded to a packet and the treatment of a packet in the network. An IPsec policy allows classifying IP packets into different traffic flows and specifies the actions or transformations performed on IP packets on each of the traffic flows. The main components of an IPsec policy are: IP packet filter and selector (IP address, protocol, and port information) and transform set. IPsec traffic selector The traffic selector is a traffic filter that defines and identifies the traffic flow between two systems that have IPsec protection. IP addresses, the direction of traffic flow (inbound, outbound) and the upper layer protocol are used to define a filter for traffic (IP datagrams) that is protected using IPsec. IPsec transform A transform set is a combination of IPsec protocols and cryptographic algorithms that are applied on the packet after it is matched to a selector. The transform set specifies the IPsec protocol, IPsec mode and action to be performed on the IP packet. It specifies the key management policy that is needed for the IPsec connection and the encryption and authentication algorithms to be used in security associations when IKE is used as the key management protocol. IPsec can protect either the entire IP datagram or only the upper-layer protocols. The appropriate modes are called tunnel mode and transport mode. In tunnel mode the IP datagram is fully encapsulated by a new IP datagram using the IPsec protocol. In transport mode only the payload of the IP datagram is handled by the IPsec protocol; it inserts the IPsec header between the IP header and the upper-layer protocol header. IKE policies When IKE is used as the key management protocol, IKE policy defines the parameters used in IKE negotiations needed to establish IKE SA and parameters used in negotiations to establish IPsec SAs. These include the authentication and encryption algorithms, and the primary authentication method, such as preshared keys, or a certificate-based method, such as RSA signatures. 152 Fabric OS Administrator's Guide 53-1001336-01