HP StorageWorks 8/40 Brocade Web Tools Administrator's Guide v6.2.0 (53-100119 - Page 270
Basic IPSec configurations, Endpoint to Endpoint, Gateway to Gateway, Endpoint to Gateway
 |
View all HP StorageWorks 8/40 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 270 highlights
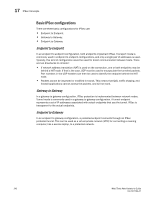
17 IPSec Concepts Basic IPSec configurations There are three basic configurations for IPSec use: • Endpoint to Endpoint. • Gateway to Gateway. • Endpoint to Gateway. Endpoint to Endpoint In an endpoint to endpoint configuration, both endpoints implement IPSec. Transport mode is commonly used in endpoint to endpoint configurations, and only a single pair of addresses is used. Typically, this kind of configuration would be used for direct communication between hosts. There are two drawbacks to consider: • If network address translation (NAT) is used on the connection, one or both endpoints may be behind a NAT node. If that is the case, UDP must be used to encapsulate the tunneled packets. Port numbers in the UDP headers can then be used to identify the endpoint behind the NAT node. • Packets cannot be inspected or modified in transit. This means that QoS, traffic shaping, and firewall applications cannot access the packets, and will not work. Gateway to Gateway In a gateway to gateway configuration, IPSec protection is implemented between network nodes. Tunnel mode is commonly used in a gateway to gateway configuration. A tunnel endpoint represents a set of IP addresses associated with actual endpoints that use the tunnel. IPSec is transparent to the actual endpoints. Endpoint to Gateway In an endpoint to gateway configuration, a protected endpoint connects through an IPSec protected tunnel. This can be used as a virtual private network (VPN) for connecting a roaming computer, like a service laptop, to a protected network. 242 Web Tools Administrator's Guide 53-1001194-01