Print Controller Design Guide for Information Security
Page 3 of 86
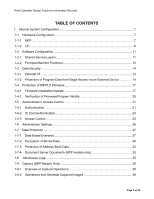
1-9-3
Capture Settings
...................................................................................................
41
1-9-4
Security Considerations
........................................................................................
42
1-9-5
Captured Documents and Log Data
......................................................................
42
1-10
Additional Methods for Increased Security
...............................................................
42
2.
Principal Machine Functions
........................................................................................
43
2-1
Copier (MFP Models Only)
.......................................................................................
43
2-1-1
Overview of Copier Operations
.............................................................................
43
2-1-2
Data Security Considerations
...............................................................................
43
2-1-3
Protection of Copy Jobs in Progress
.....................................................................
43
2-1-4
Protection of Document Server Documents
..........................................................
43
2-1-5
Protection of Copier/Document Server Features
..................................................
45
2-1-6
Restricting the Available Functions for Each Individual User
................................
45
2-1-7
Job/Access Log Data Collection
...........................................................................
45
2-1-8
Print Backup
.........................................................................................................
45
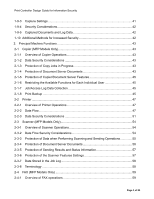
2-2
Printer
......................................................................................................................
47
2-2-1
Overview of Printer Operations
.............................................................................
47
2-2-2
Data Flow
..............................................................................................................
47
2-2-3
Data Security Considerations
...............................................................................
51
2-3
Scanner (MFP Models Only)
....................................................................................
54
2-3-1
Overview of Scanner Operations
..........................................................................
54
2-3-2
Data Flow Security Considerations
.......................................................................
54
2-3-3
Protection of Data when Performing Scanning and Sending Operations
..............
55
2-3-4
Protection of Document Server Documents
..........................................................
56
2-3-5
Protection of Sending Results and Status Information
..........................................
57
2-3-6
Protection of the Scanner Features Settings
........................................................
57
2-3-7
Data Stored in the Job Log
...................................................................................
58
2-3-8
Terminology
..........................................................................................................
58
2-4
FAX (MFP Models Only)
..........................................................................................
59
2-4-1
Overview of FAX operations
.................................................................................
59