Print Controller Design Guide for Information Security
Page 4 of 86
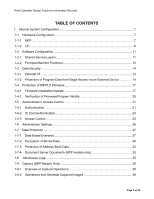
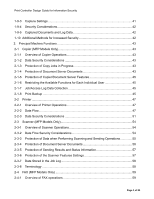
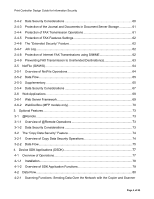
2-4-2
Data Security Considerations
...............................................................................
60
2-4-3
Protection of the Journal and Documents in Document Server Storage
...............
61
2-4-4
Protection of FAX Transmission Operations
.........................................................
61
2-4-5
Protection of FAX Features Settings
.....................................................................
62
2-4-6
The “Extended Security” Feature
..........................................................................
62
2-4-7
Job Log
.................................................................................................................
62
2-4-8
Protection of Internet FAX Transmissions using S/MIME
......................................
62
2-4-9
Preventing FAX Transmission to Unintended Destination(s)
.................................
63
2-5
NetFile (GWWS)
......................................................................................................
64
2-5-1
Overview of NetFile Operations
............................................................................
64
2-5-2
Data Flow
..............................................................................................................
65
2-5-3
Supplementary
......................................................................................................
65
2-5-4
Data Security Considerations
...............................................................................
67
2-6
Web Applications
.....................................................................................................
69
2-6-1
Web Server Framework
........................................................................................
69
2-6-2
WebDocBox (MFP models only)
...........................................................................
70
3.
Optional Features
.........................................................................................................
73
3-1
@Remote
.................................................................................................................
73
3-1-1
Overview of @Remote Operations
.......................................................................
73
3-1-2
Data Security Considerations
...............................................................................
73
3-2
The “Copy Data Security” Feature
...........................................................................
74
3-2-1
Overview of Copy Data Security Operations
.........................................................
74
3-2-2
Data Flow
..............................................................................................................
75
4.
Device SDK Applications (DSDK)
................................................................................
77
4-1
Overview of Operations
............................................................................................
77
4-1-1
Installation
.............................................................................................................
78
4-1-2
Overview of SDK Application Functions
................................................................
79
4-2
Data Flow
.................................................................................................................
80
4-2-1
Scanning Functions: Sending Data Over the Network with the Copier and Scanner