ZyXEL P-2602R-D1A User Guide - Page 385
Table 160, Table 161, Table 162
 |
View all ZyXEL P-2602R-D1A manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 385 highlights
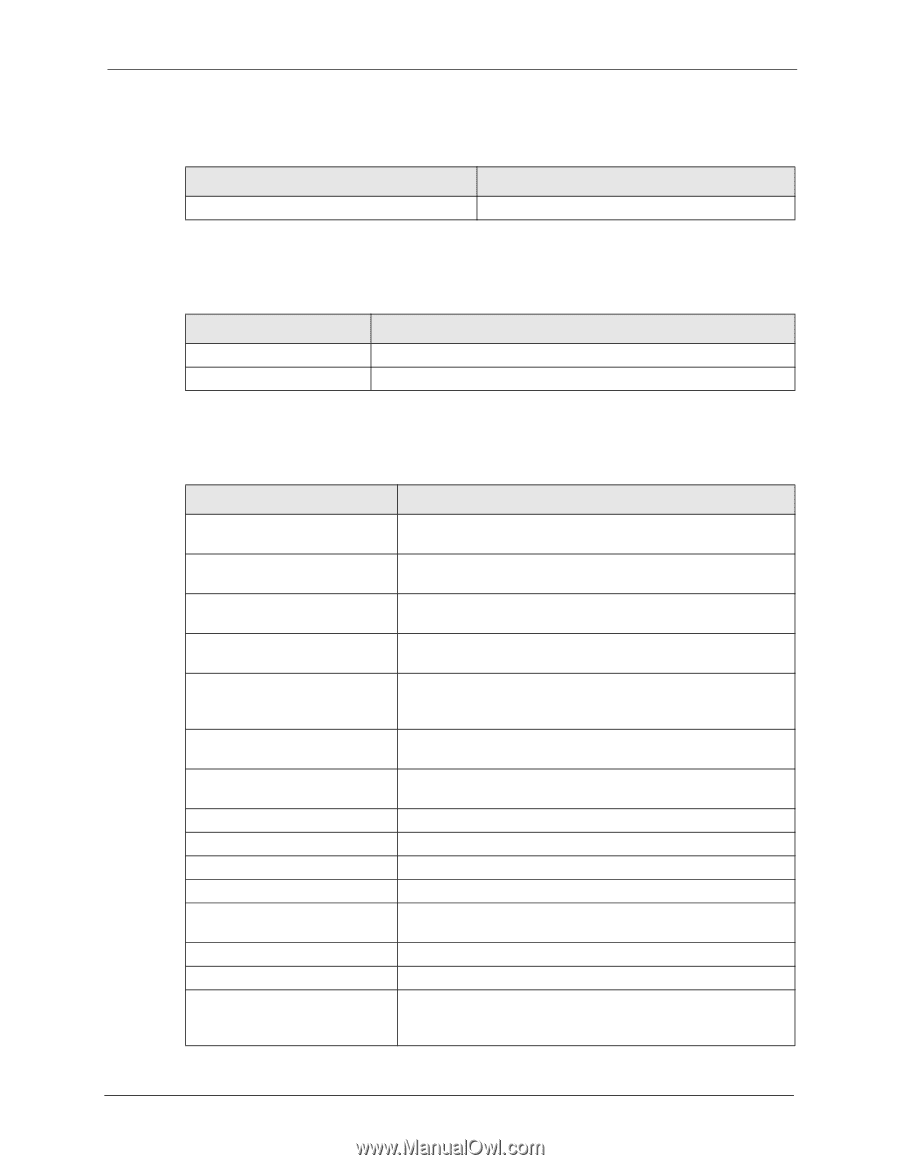
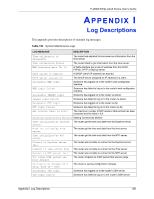
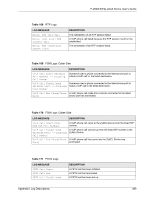
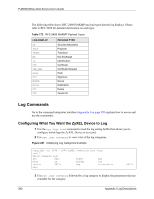
P-2602H(W)(L)-DxA Series User's Guide Table 160 UPnP Logs LOG MESSAGE UPnP pass through Firewall DESCRIPTION UPnP packets can pass through the firewall. Table 161 Content Filtering Logs LOG MESSAGE %s: block keyword %s DESCRIPTION The content of a requested web page matched a user defined keyword. The system forwarded web content. For type and code details, see Table 165 on page 387. Table 162 Attack Logs LOG MESSAGE DESCRIPTION attack [ TCP | UDP | IGMP | ESP | GRE | OSPF ] attack ICMP (type:%d, code:%d) land [ TCP | UDP | IGMP | ESP | GRE | OSPF ] land ICMP (type:%d, code:%d) ip spoofing - WAN [ TCP | UDP | IGMP | ESP | GRE | OSPF ] ip spoofing - WAN ICMP (type:%d, code:%d) icmp echo : ICMP (type:%d, code:%d) syn flood TCP ports scan TCP teardrop TCP teardrop UDP teardrop ICMP (type:%d, code:%d) illegal command TCP NetBIOS TCP ip spoofing - no routing entry [ TCP | UDP | IGMP | ESP | GRE | OSPF ] The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF attack. The firewall detected an ICMP attack. The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF land attack. The firewall detected an ICMP land attack. The firewall detected an IP spoofing attack on the WAN port. The firewall detected an ICMP IP spoofing attack on the WAN port. The firewall detected an ICMP echo attack. The firewall detected a TCP syn flood attack. The firewall detected a TCP port scan attack. The firewall detected a TCP teardrop attack. The firewall detected an UDP teardrop attack. The firewall detected an ICMP teardrop attack. The firewall detected a TCP illegal command attack. The firewall detected a TCP NetBIOS attack. The firewall classified a packet with no source routing entry as an IP spoofing attack. Appendix I Log Descriptions 385