Compaq Evo n800c Wireless Security - Page 16
Digital Signatures
 |
View all Compaq Evo n800c manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 16 highlights
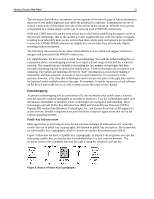
Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be the legal equivalent of handwritten signatures. The signer generates a "hash value" or "digital fingerprint" of the document or message to be signed.4 The hash value is unique to the document or message. The hash value is then converted into a digital signature by the user's private key. The digital signature is sent to the recipient for verification. The recipient verifies the digital signature by generating a hash value of the original message, decrypting the original hash value in the digital signature with the public key, then comparing the original hash value with the recipient's hash value. If the two hash values match, the signature is deemed authentic. Another way to verify a digital signature is through a Certification Authority (CA). A CA is usually a trusted third party able to verify that the private key used to generate the digital signature belongs to the signer, and that the public key is indeed associated with the digitally signed document or message. Figure 8 illustrates digital signatures. In Figure 8 the original data is hashed using a one-way algorithm. The hash is encrypted using the originator's private key. The original data along with the digital signature is sent over the network to the recipient, who decrypts the digital signature using the public key. The recipient compares the one-way hash from the digital signature to the one-way hash from the original data. If the two match, the data has not been compromised and the identity of the originator is confirmed. Figure 8: Digital Signatures 4 Hashing is the process of transforming a string of characters into a fixed-length numeric value or "key" that represents the original string.