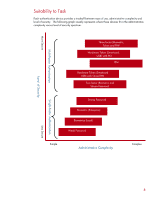
HP Tc4200 HP ProtectTools: Authentication technologies and suitability to task - Page 9
Conclusion, result in user dissatisfaction.
 |
View all HP Tc4200 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 9 highlights
Conclusion All authentication technologies provide a level of protection against unauthorized access. The determining tradeoffs are level of security, cost, and usability. In making a decision on which authentication technology to deploy, all three factors should be taken into consideration. It is important that the selected technology provide the level of protection appropriate for an environment. It is also important that the selected technology be usable and not result in user dissatisfaction. For more information www.hp.com www.hp.com/products/security © 2005 Hewlett-Packard Development Company, L.P. The information contained herein is subject to change without notice. The only warranties for HP products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. HP shall not be liable for technical or editorial errors or omissions contained herein. Microsoft and Windows are U.S. registered trademarks of Microsoft Corporation 5983-1956EN, Revision 2, 06/2005