TP-Link TL-SL3428 User Guide - Page 43
Configuring Traffic Control - manual
 |
UPC - 845973020491
View all TP-Link TL-SL3428 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 43 highlights
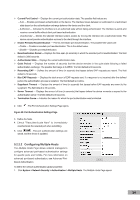
Figure 48: Authenticated Hosts Page The Authenticated Hosts Page contains the following fields: User Name - Lists the supplicants that were authenticated, and are permitted on each port. Port - Displays the port number. Session Time - Displays the amount of time (in seconds) the supplicant was logged on the port. Authentication Method - Displays the method by which the last session was authenticated. The possible field values are: - Remote - 802.1x authentication is not used on this port (port is forced-authorized). - None - The supplicant was not authenticated. - RADIUS - The supplicant was authenticated by a RADIUS server. MAC Address - Displays the supplicant MAC address. 5.2.3 Configuring Traffic Control This section contains information for managing both port security and storm control, and includes the following topics: Managing Port Security Enabling Storm Control 5.2.3.1 Managing Port Security Network security can be increased by limiting access on a specific port only to users with specific MAC addresses. The MAC addresses can be dynamically learned or statically configured. Locked port security monitors both received and learned packets that are received on specific ports. Access to the locked port is limited to users with specific MAC addresses. These addresses are either manually defined on the port, or learned on that port up to the point when it is locked. When a packet is received on a locked port, and the packet TP-Link source MAC address is not tied to that port (either it was learned on a different port, or it is unknown to the system), the protection mechanism is invoked, and can provide various options. Unauthorized packets arriving at a locked port are either: Forwarded Discarded with no trap Discarded with a trap Shuts down the port Locked port security also enables storing a list of MAC addresses in the configuration file. The MAC address list can be restored after the device has been reset. Disabled ports are activated from the Port Security Page. To view port security parameters: 1. Click System > Network Security > Traffic Control > Port Security. The Port Security Page opens: 36