Cisco 4506-E Software Guide - Page 500
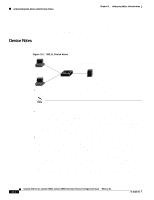
Device Roles
 |
View all Cisco 4506-E manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 500 highlights
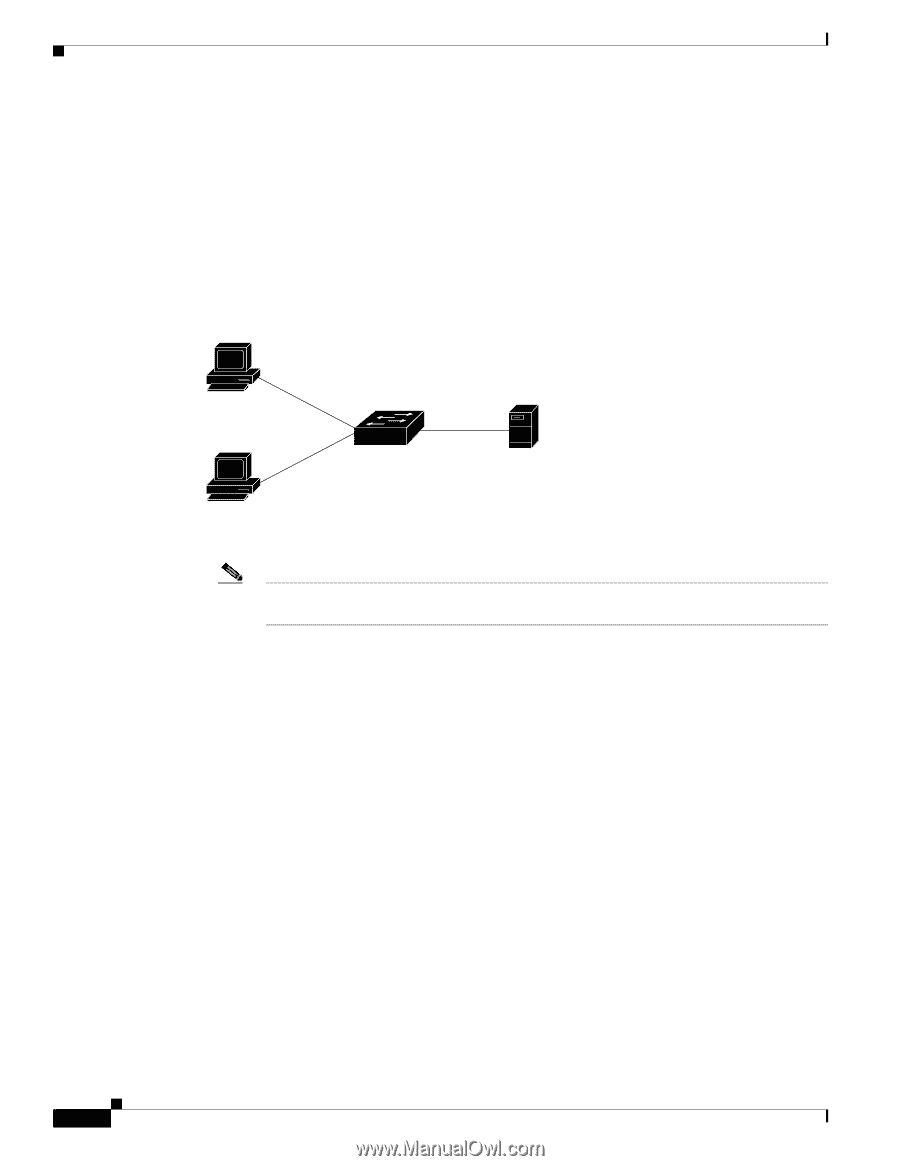
Understanding How 802.1x Authentication Works Chapter 31 Configuring 802.1x Authentication always open. The controlled port is open only when the device that is connected to the port has been authorized by 802.1x. After this authorization takes place, the controlled port opens, allowing normal traffic to pass. You can restrict traffic in both directions or just incoming traffic. The following sections describe how 802.1x authentication work. Device Roles With 802.1x port-based authentication, the devices in the network have specific roles. (See Figure 31-1.) Figure 31-1 802.1x Device Roles Workstations (supplicants) Catalyst switch Authentication server (RADIUS) 79599 • Host-Requests access to the LAN and switch services and responds to requests from the switch. The workstation must be running 802.1x-compliant software. Note IEEE 802.1x uses the term supplicant for client or host. In this publication, we use host instead of supplicant because host is used in the Catalyst 4000 family CLI syntax. • Authentication server-Performs the actual authentication of the host. The authentication server validates the identity of the host and notifies the switch whether or not the host is authorized to access the LAN and switch services. Because the switch acts as the proxy, the authentication service is transparent to the host. In this release, the Remote Authentication Dial-In User Service (RADIUS) security system with Extensible Authentication Protocol (EAP) extensions is the only supported authentication server; it is available in Cisco Secure Access Control Server version 3.0. RADIUS operates in a client/server model in which secure authentication information is exchanged between the RADIUS server and one or more RADIUS clients. • Switch-Controls the physical access to the network based on the authentication status of the host. The switch acts as an intermediary (proxy) between the host and the authentication server, requesting identity information from the host, verifying that information with the authentication server, and relaying a response to the host. The switch interacts with the RADIUS client. The RADIUS client encapsulates and decapsulates the EAP frames and interacts with the authentication server. When the switch receives Extensible Authentication Protocol over LAN (EAPOL) frames and relays them to the authentication server, the Ethernet header is stripped and the remaining EAP frame is reencapsulated in the RADIUS format. The EAP frames are not modified or examined during encapsulation, and the authentication server must support EAP within the native frame format. When the switch receives frames from the authentication server, the server's frame header is removed, leaving the EAP frame, which is then encapsulated for Ethernet and sent to the host. 31-2 Catalyst 4500 Series, Catalyst 2948G, Catalyst 2980G Switches Software Configuration Guide-Release 8.1 78-15486-01