Cisco NM-HD-1V= User Guide - Page 10
Authentication Initiation and Message Exchange, dot1x port-control auto
 |
UPC - 746320823355
View all Cisco NM-HD-1V= manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 10 highlights
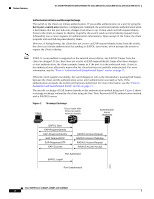
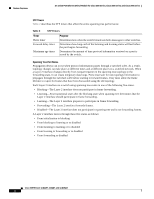
Feature Overview 16- and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Authentication Initiation and Message Exchange The switch or the client can initiate authentication. If you enable authentication on a port by using the dot1x port-control auto interface configuration command, the switch must initiate authentication when it determines that the port link state changes from down to up. It then sends an EAP-request/identity frame to the client to request its identity (typically, the switch sends an initial identity/request frame followed by one or more requests for authentication information). Upon receipt of the frame, the client responds with an EAP-response/identity frame. However, if during bootup, the client does not receive an EAP-request/identity frame from the switch, the client can initiate authentication by sending an EAPOL-start frame, which prompts the switch to request the client's identity. Note If 802.1x is not enabled or supported on the network access device, any EAPOL frames from the client are dropped. If the client does not receive an EAP-request/identity frame after three attempts to start authentication, the client transmits frames as if the port is in the authorized state. A port in the authorized state effectively means that the client has been successfully authenticated. For more information, see the "Ports in Authorized and Unauthorized States" section on page 11. When the client supplies its identity, the switch begins its role as the intermediary, passing EAP frames between the client and the authentication server until authentication succeeds or fails. If the authentication succeeds, the switch port becomes authorized. For more information, see the "Ports in Authorized and Unauthorized States" section on page 11. The specific exchange of EAP frames depends on the authentication method being used. Figure 2 shows a message exchange initiated by the client using the One-Time-Password (OTP) authentication method with a RADIUS server. Figure 2 Client Message Exchange Cisco router with Ethernet switch network module Authentication server (RADIUS) EAPOL-Start EAP-Request/Identity EAP-Response/Identity EAP-Request/OTP EAP-Response/OTP EAP-Success RADIUS Access-Request RADIUS Access-Challenge RADIUS Access-Request RADIUS Access-Accept Port Authorized EAPOL-Logoff Port Unauthorized 88851 Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 10