Compaq 615 Security - Linux - Page 5
Protecting the computer
 |
View all Compaq 615 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 5 highlights
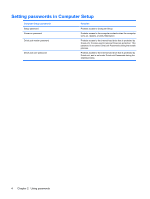
1 Protecting the computer NOTE: Security solutions are designed to act as deterrents. These deterrents may not prevent a product from being mishandled or stolen. Security features provided with your computer can protect the computer, personal information, and data from a variety of risks. The way you use your computer will determine which security features you need to use. The operating system offers certain security features. Additional security features are listed in the following table. Most of these additional security features can be configured in the Computer Setup utility (referred to hereafter as Computer Setup). To protect against Use this security feature Unauthorized use of the computer Power-on authentication using passwords or smart cards Unauthorized access to Computer Setup (f10) Setup password in Computer Setup* Unauthorized access to the contents of a hard drive DriveLock password in Computer Setup* Unauthorized reset of Computer Setup (f10) passwords Stringent security feature in Computer Setup* Unauthorized startup from an optical drive, diskette drive, or internal network adapter Unauthorized access to data Boot options feature in Computer Setup* ● Firewall software ● Operating system updates Unauthorized access to Computer Setup settings and other Setup password in Computer Setup* system identification information Unauthorized removal of the computer Security cable slot (used with an optional security cable) *Computer Setup is a utility accessed by pressing f10 when the computer is turned on or restarted. When using Computer Setup, you must use the keys on your computer to navigate and make selections. 1