Dell EqualLogic PS4210X EqualLogic Group Manager Administrator s Guide PS Seri - Page 122
Enable the iSCSI Discovery Filter, About Multihost Access to Targets
 |
View all Dell EqualLogic PS4210X manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 122 highlights
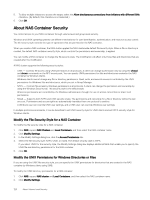
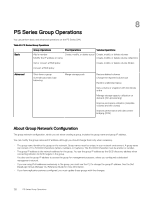
Table 22. Access Requirements for iSCSI Targets Security Condition Description Network access To discover targets, the initiator must have network access to the group IP address. Initiator access controls (Optional) If the initiator enabled target authentication (sometimes called mutual authentication), the target authentication credentials in the group must match the credentials that were configured in the initiator. These credentials apply to all group targets. Target access controls The initiator must meet all the conditions in one access control policy for the target. (See About Multihost Access to Targets.) Enable the iSCSI Discovery Filter To enable the iSCSI discovery filter: 1. Click Group → Group Configuration. 2. Click the iSCSI tab. 3. In the iSCSI Discovery panel, select Prevent unauthorized hosts from discovering targets. Disable the iSCSI Discovery Filter To disable the iSCSI discovery filter: 1. Click Group → Group Configuration. 2. Click the iSCSI tab. 3. In the iSCSI Discovery panel, clear Prevent unauthorized hosts from discovering targets. About Multihost Access to Targets In a shared storage environment, you must control computer access to iSCSI targets (volumes and snapshots), because multiple computers writing to a target in an uncoordinated manner will result in volume corruption. When an initiator tries to log in to a target, the group uses access control policies to determine if access should be authorized. However, access control policies do not prevent multiple initiators, either on the same computer or different computers, from accessing the same target. By default, the group disables multihost (shared) access to a target. Therefore, only one iSCSI qualified name (IQN) can connect to a target at one time. If you disable multihost access to a volume, when an initiator tries to log in to the volume: • If an iSCSI initiator is not connected to the volume, the group uses access control policies to determine whether to authorize access. • If an initiator is connected to the volume, the group compares the IQN of the current connection to the IQN of the incoming connection. If the IQNs are not the same, access is denied. If the IQNs are the same, the group uses access control policies to determine whether to authorize access. However, some environments might need multihost access to a target. You can enable multihost access to a target if you meet one of the following conditions: • Your cluster environment gives the initiators on each cluster computer a different IQN, and the environment can manage multiple connections to a target. For example, the environment uses a Distributed Lock Manager or SCSI reservations. • Your multipathing solution does not use the same IQN on all initiators, and you cannot modify the names to be the same. • You use an environment, such as a virtual server, that can manage multiple connections to the same iSCSI target (for example, through SCSI reservations). • Initiators on a single computer do not use the same IQN. In all cases, use access control policies as the primary method of protecting iSCSI targets in a group. 122 About Volume-Level Security