Dell PowerEdge M605 Fabric OS Administrator’s Guide - Page 184
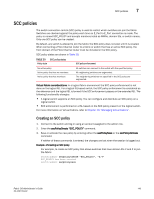
Authentication policy for fabric elements, Switch A, Local secret A, Peer secret B
 |
View all Dell PowerEdge M605 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 184 highlights
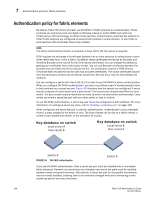
7 Authentication policy for fabric elements Authentication policy for fabric elements By default, Fabric OS v6.2.0 and later use DH-CHAP or FCAP protocols for authentication. These protocols use shared secrets and digital certificates, based on switch WWN and public key infrastructure (PKI) technology, to authenticate switches. Authentication automatically defaults to FCAP if both switches are configured to accept FCAP protocol in authentication. To use FCAP on both switches, PKI certificates have to be installed. NOTE The fabric authentication feature is available in base Fabric OS. No license is required. FCAP requires the exchange of certificates between two or more switches to authenticate to each other before they form or join a fabric. By default, these certificates are issued by Brocade, and therefore Brocade is the root CA for all of the issued certificates. You can change the default by getting your certificates from a third-party vendor. You can use Brocade certificates between the switches that are Fabric OS v6.4.0 and pre-v6.4.0. The certificates must be in PEM (Privacy Enhanced Mail) encoded format for both root and peer certificates. The switch certificates issued from the third-party vendors can be directly issued from the root CA or from an intermediate CA authority. You can configure a switch with Fabric OS v6.2.0 or later to use DH-CHAP for device authentication. When you configure DH-CHAP authentication, you also must define a pair of shared secrets known to both switches as a secret key pair. Figure 16 illustrates how the secrets are configured. A secret key pair consists of a local secret and a peer secret. The local secret uniquely identifies the local switch. The peer secret uniquely identifies the entity to which the local switch authenticates. Every switch can share a secret key pair with any other switch or host in a fabric. To use DH-CHAP authentication, a secret key pair has to be configured on both switches. For more information on setting up secret key pairs, refer to "Setting a secret key pair" on page 149. When configured, the secret key pair is used for authentication. Authentication occurs whenever there is a state change for the switch or port. The state change can be due to a switch reboot, a switch or port disable and enable, or the activation of a policy. Key database on switch Local secret A Peer secret B Key database on switch Local secret B Peer secret A Switch A FIGURE 16 DH-CHAP authentication Switch B If you use DH-CHAP authentication, then a secret key pair must be installed only in connected fabric elements. However, as connections are changed, new secret key pairs must be installed between newly connected elements. Alternatively, a secret key pair for all possible connections may be initially installed, enabling links to be arbitrarily changed while still maintaining a valid secret key pair for any new connection. 144 Fabric OS Administrator's Guide 53-1001763-02