HP Brocade 8/12c Fabric OS Encryption Administrator's Guide v6.4.0 (53-1001864 - Page 213
General encryption troubleshooting
 |
View all HP Brocade 8/12c manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 213 highlights
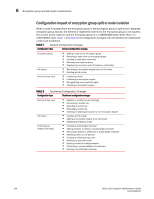
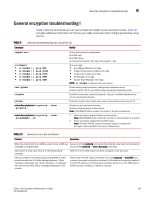
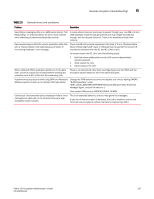
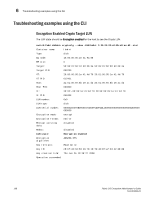
General encryption troubleshooting I 6 General encryption troubleshooting I Table 9 lists the commands you can use to check the health of your encryption setup. Table 10 provides additional information for failures you might encounter while configuring switches using the CLI. TABLE 9 Command General troubleshooting tips using the CLI Activity supportsave errdumpall • errdumpall | grep KAC • errdumpall | grep CVLM • errdumpall | grep CVLC • errdumpall | grep SPM • errdumpall | grep CNM configshow cfgshow nsshow switch:SecurityAdmin> cryptocfg --show -groupcfg switch:SecurityAdmin> cryptocfg --show -groupmember -all Check whole system configuration. Run RAS logs. Run RAS traces. Run Security Processor (SP) logs (mainly kpd.log). Run error logs: • Key Adapter Module error logs. • Crypto Virtual device module error logs. • Crypto LUN module error logs. • SP Manager error logs. • Cluster Node Manager error logs. NOTE: errdumpall requires root user access. Check whole system persistent configuration database dump. Check for SPM-, CVLM-, and CNM-related persistent database entries. Check for redirection zones starting with "red_xxx" in defined database for virtual and physical devices. Check for crypto virtual target and crypto virtual initiator entries for VT/VI Check key vault connection status. Check encryption group/cluster status. Note: CONVERGED status means the cluster is formed successfully. 1 Check encryption group/cluster member status. Note: DISCOVERED state means the member is currently part of a cluster. 2 Check encryption engine/SP and KEK status. Note: SP state ONLINE means encryption engine is enabled for encryption with valid KEK (Link Key or Master Key). TABLE 10 Problem General errors and conditions Resolution When the connectivity to an LKM key vault is lost, a RAS log Issue any of the cryptocfg commands that attempt a key vault communication message is not generated. (such as the cryptocfg --show -groupcfg command). Connection to a key vault returns a "Not Responding" message. After you create an encryption group using RKM, a newly created container's LUN state changes between "Write metadata is pending" and "Write metadata is in progress" with continuous [RKD-1001] messages displayed on the console. Determine if the default port has been changed on the key vault. Power cycle the DCX chassis and then issue the cryptocfg --enableEE [slot number] command to bring the container's LUN state to Encryption Enabled.If the eth0 IP address on the Brocade Encryption Switch or on the FS8-18 port blade has been modified, a reboot is required. Fabric OS Encryption Administrator's Guide 195 53-1001864-01