Print Controller Design Guide for Information Security
Page 2 of 86
TABLE OF CONTENTS
1.
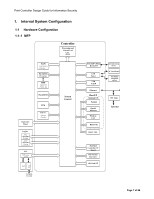
Internal System Configuration
........................................................................................
7
1-1
Hardware Configuration
.............................................................................................
7
1-1-1
MFP
........................................................................................................................
7
1-1-2
LP
...........................................................................................................................
9
1-2
Software Configuration
.............................................................................................
11
1-2-1
Shared Service Layers
..........................................................................................
11
1-2-2
Principal Machine Functions
.................................................................................
12
1-3
Data Security
...........................................................................................................
14
1-3-1
External I/F
...........................................................................................................
14
1-3-2
Protection of Program Data from Illegal Access via an External Device
...............
14
1-4
Protection of MFP/LP Firmware
...............................................................................
17
1-4-1
Firmware Installation/Update
................................................................................
17
1-4-2
Verification of Firmware/Program Validity
.............................................................
20
1-5
Authentication, Access Control
................................................................................
21
1-5-1
Authentication
.......................................................................................................
21
1-5-2
IC Card Authentication
..........................................................................................
24
1-5-3
Access Control
......................................................................................................
25
1-6
Administrator Settings
..............................................................................................
26
1-7
Data Protection
........................................................................................................
27
1-7-1
Data Erase/Overwrite
............................................................................................
27
1-7-2
Encryption of Stored Data
.....................................................................................
29
1-7-3
Protection of Address Book Data
..........................................................................
32
1-7-4
Document Server Documents (MFP models only)
................................................
33
1-8
Job/Access Logs
......................................................................................................
35
1-9
Capture (MFP Models Only)
....................................................................................
39
1-9-1
Overview of Capture Operations
...........................................................................
39
1-9-2
Operations that Generate Captured Images
.........................................................
39