HP Cisco MDS 9216i Cisco MDS 9000 Family Storage Media Encryption Configuratio - Page 248
Creating CA Certificates, req -x509 -days 365 -newkey rsa -out cacert.pem -outform PEM
 |
View all HP Cisco MDS 9216i manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 248 highlights
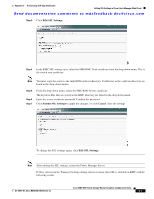
Configuring SSL for Cisco SME Appendix C Provisioning Self-Sign Certificates Send documentation comments to [email protected] Creating CA Certificates To generate the CA certificates, follow these steps: Step 1 Step 2 Create a CA certificate using the OpenSSL application. Issue the following command for the 365 day certificate: OpenSSL> req -x509 -days 365 -newkey rsa -out cacert.pem -outform PEM This creates a cacert.pem file in the directory with OpenSSL.exe. Open the CLI and enter the configuration mode. switch# config t Step 3 Step 4 Step 5 Enter configuration commands, one per line. End with CNTL/Z. Create a trust point named my_ca. switch(config)#crypto ca trustpoint my_ca Create an RSA keypair for the switch in the trustpoint submode. switch(config-trustpoint)# rsakeypair my_ca_key Exit the trustpoint submode. switch(config-trustpoint)# exit Step 6 Authenticate the cacert.pem file for the trustpoint by cutting and pasting the contents of the cacert.pem created in Step 1. switch(config)# crypto ca authenticate my_ca input (cut & paste) CA certificate (chain) in PEM format; end the input with a line containing only END OF INPUT : ----BEGIN CERTIFICATE---MIIDnjCCAwegAwIBAgIBADANBgkqhkiG9w0BAQQFADCBlzELMAkGA1UEBhMCVVMx EzARBgNVBAgTCkNhbGlmb3JuaWExETAPBgNVBAcTCFNhbiBKb3NlMRowGAYDVQQK ExFDaXNjbyBTeXN0ZW1zIEluYzEOMAwGA1UECxMFRGV2ZWwxETAPBgNVBAMTCG1h bWFzc2V5MSEwHwYJKoZIhvcNAQkBFhJtYW1hc3NleUBjaXNjby5jb20wHhcNMDcx MTIyMDgzNDM1WhcNMDgxMTIxMDgzNDM1WjCBlzELMAkGA1UEBhMCVVMxEzARBgNV BAgTCkNhbGlmb3JuaWExETAPBgNVBAcTCFNhbiBKb3NlMRowGAYDVQQKExFDaXNj byBTeXN0ZW1zIEluYzEOMAwGA1UECxMFRGV2ZWwxETAPBgNVBAMTCG1hbWFzc2V5 MSEwHwYJKoZIhvcNAQkBFhJtYW1hc3NleUBjaXNjby5jb20wgZ8wDQYJKoZIhvcN AQEBBQADgY0AMIGJAoGBAMbZAv0+Ka/FS3/jwdaqItc8Ow3alpw9gyqEzA3uFLjN tXSfHRu9OsrP5tliHHlJP+fezeAUuVfmMTPrOIxURcF2c7Yq1Ux5s4Ua3cMGf9BG YBRbhO8Filt2mGDqY5u0mJY+eViR69MZk8Ouj+gRxQq83fB8MqJG39f1BedRcZLB AgMBAAGjgfcwgfQwHQYDVR0OBBYEFGXsBg7f7FJcL/741j+M2dgI7rIyMIHEBgNV HSMEgbwwgbmAFGXsBg7f7FJcL/741j+M2dgI7rIyoYGdpIGaMIGXMQswCQYDVQQG EwJVUzETMBEGA1UECBMKQ2FsaWZvcm5pYTERMA8GA1UEBxMIU2FuIEpvc2UxGjAY BgNVBAoTEUNpc2NvIFN5c3RlbXMgSW5jMQ4wDAYDVQQLEwVEZXZlbDERMA8GA1UE AxMIbWFtYXNzZXkxITAfBgkqhkiG9w0BCQEWEm1hbWFzc2V5QGNpc2NvLmNvbYIB ADAMBgNVHRMEBTADAQH/MA0GCSqGSIb3DQEBBAUAA4GBAFmDucZlBZFJk09IihEm 5wd4oouxHsKPQroyG/CYShv1XXAyEGytxuCAITDzMq2IJiFbZt0kIiyuP9YRQLNR z47G4IRJGp5J2HnOc2cdF8Mc0DDApdgndUiIX/lv7vuQfyxqX45oSncwQct3y38/ FPEbcRgZgnOgwcrqBzKV0Y3+ ----END CERTIFICATE---END OF INPUT Fingerprint(s): MD5 Fingerprint=1E:18:10:69:7B:C1:CC:EA:82:08:67:FB:90:7D:58:EB Do you accept this certificate? [yes/no]:yes Cisco MDS 9000 Family Storage Media Encryption Configuration Guide C-2 OL-18091-01, Cisco MDS NX-OS Release 4.x