Ricoh Aficio MP C3001 Security Target - Page 49
FPT_FDI_EXP.1, Restricted forwarding of data to external interfaces
 |
View all Ricoh Aficio MP C3001 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 49 highlights
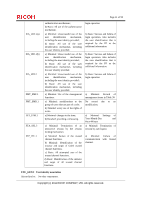
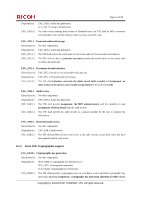
Page 48 of 93 are firewall systems but also other systems that require a specific work flow for the incoming data before it can be transferred. Direct forwarding of such data (i.e., without processing the data first) between different external interfaces is therefore a function that-if allowed at all-can only be allowed by an authorized role. It has been viewed as useful to have this functionality as a single component that allows specifying the property to disallow direct forwarding and require that only an authorized role can allow this. Since this is a function that is quite common for a number of products, it has been viewed as useful to define an extended component. The Common Criteria defines attribute-based control of user data flow in its FDP class. However, in this Protection Profile, the authors needed to express the control of both user data and TSF data flow using administrative control instead of attribute-based control. It was found that using FDP_IFF and FDP_IFC for this purpose resulted in SFRs that were either too implementation-specific for a Protection Profile or too unwieldy for refinement in a Security Target. Therefore, the authors decided to define an extended component to address this functionality. This extended component protects both user data and TSF data, and it could therefore be placed in either the FDP or the FPT class. Since its purpose is to protect the TOE from misuse, the authors believed that it was most appropriate to place it in the FPT class. It did not fit well in any of the existing families in either class, and this led the authors to define a new family with just one member. FPT_FDI_EXP.1 Restricted forwarding of data to external interfaces Hierarchical to: No other components Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to restrict data received on [assignment: the Operation Panel, LAN, telephone line] from being forwarded without further processing by the TSF to [assignment: the LAN and telephone line]. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.