Dell PowerConnect W-Series FIPS Dell PowerConnect W-AP92/93, W-AP105, W-AP175 - Page 35
Services
 |
View all Dell PowerConnect W-Series FIPS manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 35 highlights
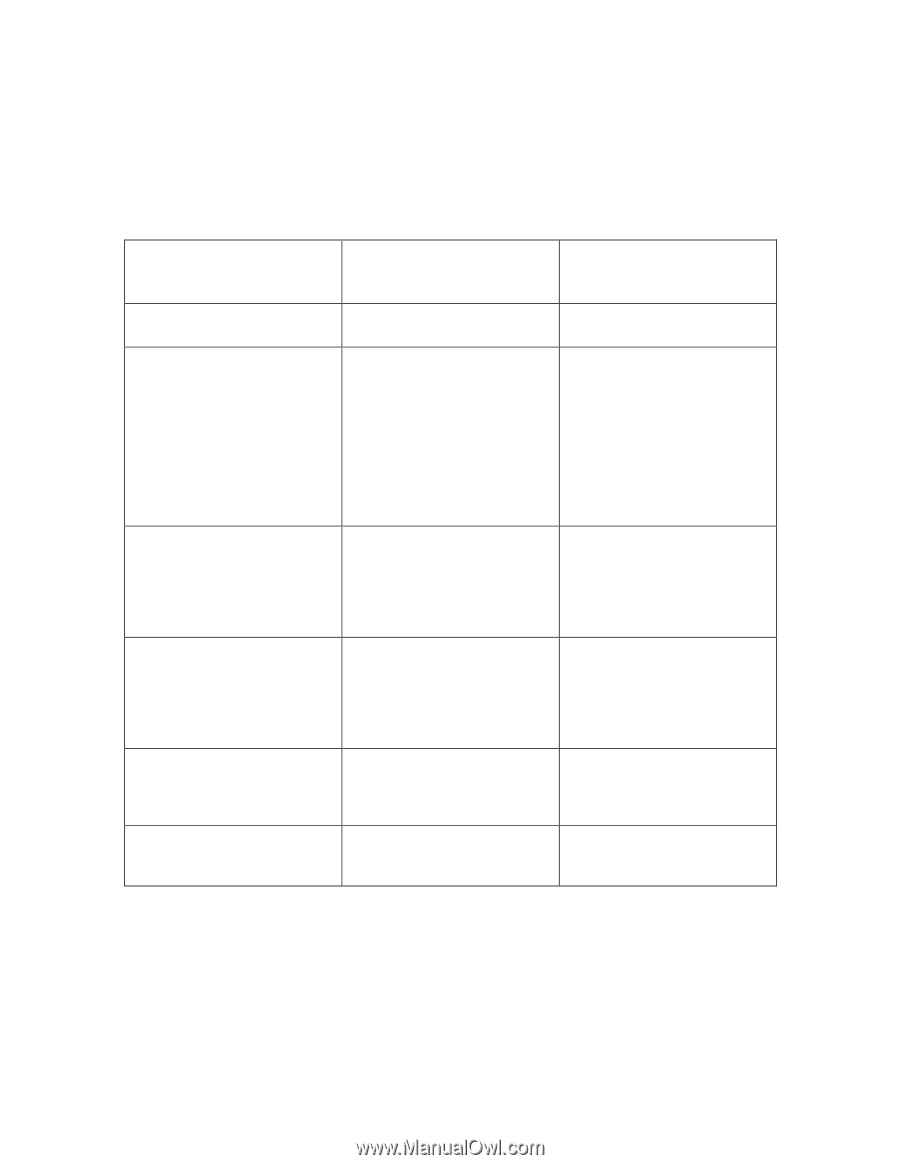
4.2 Services The module provides various services depending on role. These are described below. 4.2.1 Crypto Officer Services The CO role in each of FIPS modes defined in section 3.3 has the same services Service Description CSPs Accessed (see section 6 below for complete description of CSPs) FIPS mode enable/disable The CO selects/de-selects FIPS mode as a configuration option. None. Key Management The CO can configure/modify the IKEv1/IKEv2 shared secret (The RSA private key is protected by non-volatile memory and cannot be modified) and the WPA2 PSK (used in advanced Remote AP configuration). Also, the CO/User implicitly uses the KEK to read/write configuration to nonvolatile memory. IKEv1/IKEv2 shared secret WPA2 PSK KEK Remotely reboot module The CO can remotely trigger a reboot KEK is accessed when configuration is read during reboot. The firmware verification key and firmware verification CA key are accessed to validate firmware prior to boot. Self-test triggered by CO/User reboot The CO can trigger a programmatic reset leading to self-test and initialization KEK is accessed when configuration is read during reboot. The firmware verification key and firmware verification CA key are accessed to validate firmware prior to boot. Update module firmware The CO can trigger a module firmware update The firmware verification key and firmware verification CA key are accessed to validate firmware prior to writing to flash. Configure non-security related module parameters CO can configure various None. operational parameters that do not relate to security 35