Samsung SCX-4720F Quick Guide (easy Manual) (ver.1.0) (English) - Page 27
None security mode settings, WPA Shared Key
 |
View all Samsung SCX-4720F manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 27 highlights
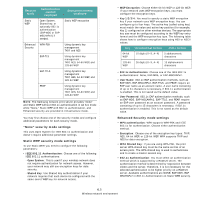
Security mode Authentication method employed Static WEP Open System, Shared key, or optionally 802.1x authentication (EAP-MD5 or EAPMSCHAPv2) if needed. Enhanced WPA-PSK Security EAP-TLS EAP-TTLS PEAP Encryption method employed Static WEP encryption Using dynamic key management TKIP, and AES Using dynamic key management TKIP, AES, 64-bit WEP, and 128-bit WEP Using dynamic key management TKIP, AES, 64-bit WEP, and 128-bit WEP Using dynamic key management TKIP, AES, 64-bit WEP, and 128-bit WEP NOTE: The Samsung network print server provides "None" and Static WEP without 802.1x authentication in Ad hoc mode while "None," Static WEP with 802.1x authentication, and Enhanced security are provided in Infrastructure mode. You may first choose one of the security modes and configure additional parameters for each security mode. "None" security mode settings This uses Open System for IEEE 802.11 authentication and doesn't require additional parameter settings. Static WEP security mode settings To use Static WEP, you need to configure the following parameters: • IEEE 802.11 Authentication: Choose one of the following IEEE 802.11 authentications: - Open System: This is used if your wireless network does not require authentication for network access. However, your network may still use encryption keys for data security. - Shared Key: Use Shared Key authentication if your network requires that each device be configured with the same secret WEP key for network access. • WEP Encryption: Choose either 64-bit WEP or 128-bit WEP. If your network uses WEP encryption keys, you must configure the encryption keys. • Key 1/2/3/4: You need to specify a static WEP encryption key if your network uses WEP encryption keys. You can configure up to four keys. The active key (called using key) must match the value and active key position (for example, Key 1) configured on other wireless devices. The appropriate key size must be configured according to the WEP key entry format and the WEP encryption key type. The following table shows how to configure encryption keys using HEX or ASCII values. Key Hexadecimal format ASCII format 64-bit WEP 10 digits (0~9, A~F) 5 alphanumeric characters 128-bit WEP 26 digits (0~9, A~F) 13 alphanumeric characters • 802.1x Authentication: Choose one of the IEEE 802.1x authentications: None, EAP-MD5, or EAP-MSCHAPv2. • User Name: 802.1x EAP authentication methods, such as EAP-MD5, EAP-MSCAHPv2, EAP-TTLS, and PEAP, require an EAP user name as an account name. A user name consisting of up to 31 characters is necessary, if 802.1x authentication is enabled. This is not saved as the default value. • User Password: 802.1x EAP authentication methods, such as EAP-MD5, EAP-MSCAHPv2, EAP-TTLS, and PEAP, require an EAP user password as an account password. A password consisting of up to 15 characters is necessary, if 802.1x authentication is enabled. This is not saved as the default value. Enhanced Security mode settings • WPA authentication: WPA supports WPA-PSK and IEEE 802.1x for authentication. Choose either authentication method. • Encryption: Choose one of the encryption key types: TKIP, AES, 64-bit WEP, or 128-bit WEP. WPA supports TKIP and AES for data encryption. • WPA Shared Key: If you are using WPA-PSK, the print server WPA shared key must be the same as that of an access point. The WPA shared key is used to authenticate and to create a master session key. • 802.1x Authentication: You must select an authentication method which is supported by a RADIUS server. The authentication method is determined by negotiation between clients and the server. Therefore, it is not necessary for the selected authentication to be higher priority on a RADIUS server. Available authentications are NONE, EAP-MD5, EAP MSCHAPv2 in 802.1x Authentication on Static WEB security. 6.5 Wireless network environment