ZyXEL P-202H Plus User Guide - Page 329
P-202H Plus v2 User's Guide, Appendix C Log Descriptions, Packet Filter Logs, ICMP Logs, TCP Reset
 |
View all ZyXEL P-202H Plus manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 329 highlights
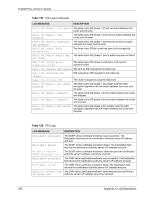
P-202H Plus v2 User's Guide Table 119 TCP Reset Logs (continued) LOG MESSAGE Firewall session time out, sent TCP RST Exceed MAX incomplete, sent TCP RST Access block, sent TCP RST DESCRIPTION The router sent a TCP reset packet when a dynamic firewall session timed out. The default timeout values are as follows: ICMP idle timeout: 3 minutes UDP idle timeout: 3 minutes TCP connection (three way handshaking) timeout: 270 seconds TCP FIN-wait timeout: 2 MSL (Maximum Segment Lifetime set in the TCP header). TCP idle (established) timeout (s): 150 minutes TCP reset timeout: 10 seconds The router sent a TCP reset packet when the number of incomplete connections (TCP and UDP) exceeded the userconfigured threshold. (Incomplete count is for all TCP and UDP connections through the firewall.)Note: When the number of incomplete connections (TCP + UDP) > "Maximum Incomplete High", the router sends TCP RST packets for TCP connections and destroys TOS (firewall dynamic sessions) until incomplete connections < "Maximum Incomplete Low". The router sends a TCP RST packet and generates this log if you turn on the firewall TCP reset mechanism (via CI command: "sys firewall tcprst"). Table 120 Packet Filter Logs LOG MESSAGE [TCP | UDP | ICMP | IGMP | Generic] packet filter matched (set:%d, rule:%d) DESCRIPTION Attempted access matched a configured filter rule (denoted by its set and rule number) and was blocked or forwarded according to the rule. Table 121 ICMP Logs LOG MESSAGE DESCRIPTION Firewall default policy: ICMP , , ICMP access matched the default policy and was blocked or forwarded according to the user's setting. For type and code details, see Table 129 on page 336. Firewall rule [NOT] match: ICMP , , , ICMP access matched (or didn't match) a firewall rule (denoted by its number) and was blocked or forwarded according to the rule. For type and code details, see Table 129 on page 336. Triangle route packet forwarded: The firewall allowed a triangle route session to pass ICMP through. Packet without a NAT table entry The router blocked a packet that didn't have a blocked: ICMP corresponding NAT table entry. Appendix C Log Descriptions 328