Cisco WS-C2960S-24PD-L Software Guide - Page 182
Starting TACACS+ Accounting, Configuring a Switch for Local AAA
 |
View all Cisco WS-C2960S-24PD-L manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 182 highlights
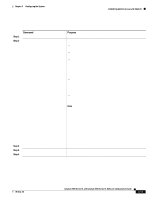
Configuring TACACS+ Chapter 6 Configuring the System Starting TACACS+ Accounting You use the aaa accounting command with the tacacs+ keyword to turn on TACACS+ accounting for each Cisco IOS privilege level and for network services. Beginning in privileged EXEC mode, follow these steps to enable TACACS+ accounting: Step 1 Step 2 Step 3 Step 4 Command configure terminal aaa accounting exec start-stop tacacs+ aaa accounting network start-stop tacacs+ exit Purpose Enter global configuration mode. Enable TACACS+ accounting to send a start-record accounting notice at the beginning of an EXEC process and a stop-record at the end. Enable TACACS+ accounting for all network-related service requests, including SLIP, PPP, and PPP NCPs. Return to privileged EXEC mode. Configuring a Switch for Local AAA You can configure AAA to operate without a server by setting the switch to implement AAA in local mode. The switch then verifies authentication and authorization. No accounting is available in this configuration. Beginning in privileged EXEC mode, follow these steps to configure the switch for local AAA: Step 1 Step 2 Step 3 Step 4 Step 5 Command configure terminal aaa new-model aaa authentication login default local aaa authorization exec local aaa authorization network local Step 6 username name privilege level password password Purpose Enter global configuration mode. Enable AAA. Set the login authorization to default to local. Configure user AAA authorization for all network-related service requests. Configure user AAA authorization to determine if the user is allowed to run an EXEC shell. Enter the local database. Repeat this command for each user. 6-54 Catalyst 2900 Series XL and Catalyst 3500 Series XL Software Configuration Guide 78-6511-08