HP CM8000 Practical IPsec Deployment for Printing and Imaging Devices
HP CM8000 - Color Multifunction Printer Manual
 |
View all HP CM8000 manuals
Add to My Manuals
Save this manual to your list of manuals |
HP CM8000 manual content summary:
- HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 1
A Parable: Confidentiality, Authentication, and Integrity 2 IPsec and Virtual Private Networks ...5 The Intranet Threat Model ...8 Too Easy: The Repeater ...10 Packet 44 IPsec Guidelines for Printing and Imaging Devices 46 HP Jetdirect IPsec Configuration Wizard: Pre-Shared Key Authentication 51 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 2
Configuration Wizard: Kerberos Authentication 137 Microsoft Windows: Kerberos Authentication 152 HP Web Jetadmin 10.x IPsec Configuration Wizard 154 Summary ...172 Appendix A: IKE Templates...173 Appendix B: Troubleshooting Web Jetadmin and Kerberos 178 Appendix C: Importing a Certificate 181 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 3
guard when he sees him again tomorrow. The boss has been running into an authentication problem. He is unable to verify his role to those in control of resources (i.e., the the HTTP protocol. The user can see this change via the Lock Icon and the HTTPS URL. • The user provides shipping information 3 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 4
-model, are indicative of an authentication problem. If an HTTPS web site on information of any kind. Figure 1 - Authentication Problem with HTTPS Let's assume the web site that web browser must support HTTPS, certificates, drivers for IPsec were and how this application transparency allowed - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 5
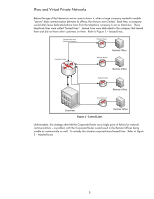
Figure 2 - Leased Lines Remote Office Unfortunately, this strategy often left the Corporate Router as a single point of failure for network communications - a problem with the Corporate Router would result in the Remote Offices being unable to communicate as well. To remedy this situation required - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 6
Office Remote Office Remote Office Corporate Figure 3 - Meshed Lines Remote Office At substantial cost, the company is able to provide some form of networking redundancy which has some "security" for their data paths. In these models, although the leased line is dedicated to the company, the - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 7
More than likely, you are attaching to the Internet via an Internet Service Provider or ISP. In this example, we are going to use the problem when leased lines aren't an option any more? We need a way to provide private communication over a public network. In short, we need a Virtual Private Network - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 8
"protecting data via mutual authentication, integrity, and confidentiality". The Intranet Threat Model What do Virtual Private Networks have to do with printing and imaging? No company is placing their printers on the public Internet (if you thought spam was bad on fax machines....) so is there - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 9
suspicious of everyone, you review the security camera logs didn't scan them in, and she didn't hack into the MFP over the network. Yet Jane still obtained them. You may think that Jane is an accomplished hacker. She isn't. She was able to accomplish all of this by downloading - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 10
advantage. We'll review five different and mutually exclusive ways in which Jane could have obtained the data. Note: This section and the "Too Easy" sections that follow are focused on printing and imaging. However, the techniques used are applicable to any service running on the network, such as - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 11
Figure 8 - A Repeater In Figure 8, we see that a repeater sends out an Ethernet packet received on one port to all other ports. You can think of Node "A" as being the wild teenager and Node "F" being the teenager's friend and Nodes "B", "C", "D", and "E" being watchful parents and curious siblings. - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 12
downloaded from the Internet for free is Wireshark (previously known as Ethereal). Wireshark is a network sniffer - it listens to network conversations (Ethernet as well as other networking been fifty cables connected to it! Which one was the MFP? Then, Jane noticed that they were all labeled with - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 13
Repeater Whenever Jane saw the CEO go into the secured MFP room to scan documents, Jane went to the open conference room and may have read the last section and said: "This isn't a problem for me because all of my network infrastructure equipment is locked away and safe. Since Jane cannot insert an - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 14
Figure 11 - Switch Broadcast Behavior Here, the broadcast address is a special address that the Ethernet switch knows that it has to send out all ports. It is an address that makes the switch act like an Ethernet repeater. Another way in which the Ethernet switch will act like an Ethernet repeater - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 15
and there is only so much memory in a switch. If we can fill up with Switch MAC table with false addresses, then every address that the switch receives for a valid device it will have to flood out all ports. In other words, fill up the Switch MAC table and you can make it act like an Ethernet - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 16
continue to use Wireshark and a tool that comes with most Microsoft Windows operating systems: Telnet. Many network administrators value the ability to use network sniffing as a way of troubleshooting normal networking problems. The initial influx of Ethernet switches made it harder and harder to do - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 17
the network administrator never knew! Using the user manual that Jane MFP. When she is done capturing packets, she moves to another open conference room and deletes the mirror port configuration. Too Easy: MITM Active Sniffing Well, you may have read the last section and said: "This isn't a problem - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 18
TCP/UDP Header Ethernet Data IP Header Ethernet Trailer Ethernet Header Figure 16 - Models Figure 16 shows three different ways of visualizing how networking protocols relate to one another. The first model is called the Academic Model. Essentially, each protocol maps to a layer or block. Ethernet - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 19
to the museum. Figure 17 - Cargo In our analogy, the truck/driver represents the Ethernet frame. The cargo represents the IP packet. The IP he intercepts the cargo. He is able to examine the fossils and then hires another driver to drive the rest of the way to the museum. By making sure the museum - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 20
kept in what is called a cache. This cache maps IP addresses to Ethernet Addresses. When data is being sent from one node to another, the networking driver will add the Ethernet Address to the Ethernet frame based upon this cached information. Refer to Figure 19 - Ping Communication. 20 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 21
IP Address B tell me what their Ethernet Address is? Device-2 Cache (IP:MAC) A:[empty] IP Address: B Ethernet Address: 2 All Devices on the network receive this packet Device-2 "Device-1 is asking for my Ethernet Address. I better respond. They may have something important to send me!" Device - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 22
Jane can use to capture data leveraging off of our previous MITM attack. Once Jane is in possession of a packet, let's say a packet from the MFP containing the destination email addresses that the secret document is going to be delivered to, Jane simply adds her email address to the existing email - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 23
MFP documents by taking advantage of the lack of confidentiality, mutual authentication, and integrity as well as some network infrastructure capabilities. We also know that these are general vulnerabilities and that any service on a TCP/IP network job being sent to the printer. We also know that - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 24
the figure is that the IP packet that received IPsec protection has its content encrypted. This encryption provides confidentiality and is shown by the yellow color and the brackets around TCP and Print Data. Should this IP packet be captured by Wireshark, the contents in yellow are unreadable and - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 25
the Ethernet addresses (NOTE: This whitepaper does not discuss IPsec Network Address Translation (NAT) or NAT traversal for the Intranet). The My IP 3 DEFAULT My IP ANY To IP Printer IP Protocol TCP From Port To Port Any 443 Printer IP TCP Printer IP ANY TCP ANY Any Any ANY 9100 80 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 26
IPsec. There are some situations where this behavior is required. For instance, there may be a service such as WINS that has many different clients, some supporting IPsec and some that do not. A network administrator may decide it is easier to not protect this protocol to prevent issues with devices - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 27
column, IP Compression, is a way of reducing the amount of data that you need to transmit by compressing the data. HP printing and imaging products do not support any IP compression protocols as yet, so we aren't going to talk about it here. Finally, for discussing Encapsulating Security Payload - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 28
to determine which packets should be protected by IPsec, the format of the IPsec packet, and the algorithms that can be used to provide IPsec services. However, the IPsec policy doesn't have any secret keys and these algorithms need secret keys to work! Where do the secret keys for these algorithms - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 29
IP TCP Print Data Configured by Administrator Does IP Traffic Require IPsec Protection? Consult IPsec Policy IPsec Policy Database Require IPsec Entry in the Security Association Database (SADB)? NO YES Security Association Database Call on IKE to populate the SADB Ethernet IP IPsec [TCP] - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 30
Because IKE is so important, we are going to go through a simple construction analogy to better illustrate the key concepts. The IPsec Policy Corporation is expanding and has decided it needs a new building. The IPsec Policy Corporation has hired IKE Construction to build this company building. The - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 31
without reference to ISAKMP. IKE terminology around proposals and acceptance is relatively confusing. Essentially, what the initiator is trying to convey is a series of parameters with associated logical operands of AND as well as OR. Since IKE can carry a variety of information, the various formats - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 32
Security Association Payload Proposal [#] Payload Transform [#] Payload Attribute Essentially, there is one Security Association payload which contains one or more Proposal payloads. Each Proposal can have one or more Transform payloads. Each Proposal [#] is an SA Format recommendation. The - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 33
Lifetime in bytes: null Transform 7 Confidentiality Algorithm: AES256 Authentication/Integrity Algorithm: SHA-1 Authentication Type: Pre-share Key DH-Group #: 2 Lifetime in sections: 3600 Lifetime in bytes: null Transform 8 Confidentiality Algorithm: AES256 Authentication/Integrity Algorithm: AES- - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 34
Figure 26 - Publicly Exchanging a Secret Here the Blue PC puts a secret in a box and locks it with the blue lock, then drops the box in the "mail" so to speak and the Green PC receives it. The Green PC puts on a green lock and drops the box back in the mail. The Blue PC removes the blue lock and - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 35
computer systems know the pass-phrase without actually transmitting it over the network. To configure IKE Pre-Shared Key Authentication, you'll need to enter Figure 27 - Windows Authentication Method This next screen shot is from HP Jetdirect. Notice the pass phrases are the same and have to be the - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 36
a Pre-Shared Key change and Microsoft and HP do not recommend it be deployed in a used for IKE SA establishment phase. It is important to review where we are at this point - we have covered decided to print data to a printer • The first packet sent to the printer is intercepted within the host's - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 37
to the packet and sends the packet out on the network • The printer receives the IPsec protected packet and checks the SADB for Phase 1 cannot use IPsec to protect its communication because of the chicken-egg problem. Tunnel Mode and Transport Mode are specific to IPsec and therefore specific to - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 38
a given security policy. For a quick overview of IKE and the configuration of Phase 1 and Phase 2, let's look at the HP Jetdirect advanced configuration screens to review all the configuration parameters. Refer to Figure 29 - IKE Phase 1: Figure 29 - IKE Phase 1 Here we make the selection between - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 39
- IKE Phase 2/Quick Mode Here we see the Encapsulation Type - HP Jetdirect recommends Transport for the Intranet. The cryptographic parameters are ESP with : • An application decided to print data to a printer • The first packet sent to the printer is intercepted within the host's IP stack by IPsec - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 40
protection to the packet and sends the packet out on the network • The printer receives the IPsec protected packet and checks the SADB for this information because the data has been processed through a driver and put into a format the printer can understand and process quickly. Do not mistake this - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 41
You can now save this data to a file, let's call it Jane.bin. Using Microsoft LPR, you can then send this data to a similar model printer later on and get the exact print out. Here is the command to use: LPR -S -P RAW Jane.bin Now let's look at the - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 42
Here we see the IKE Phase 1 main mode negotiation where the host is sending HP Jetdirect the list of transforms it wants to support. In Figure 34, HP Jetdirect accepts one. Figure 34 - IKE Phase 1: Accepted Now we begin the Diffie-Hellman key exchange in Figure 35. Figure 35 - IKE Phase 1: Diffie- - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 43
Figure 36 - IKE Phase 1: Authentication IKE Phase 1 is finally finished and now in Figure 37, we can see IKE Phase 2 or Quick Mode started. Figure 37 - IKE Phase 2: Quick Mode Finally, IKE is completed and the SADB is populated on both the initiator and the responder. This entire process will happen - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 44
on both the initiator and responder. • IPsec uses these entries to provide IPsec protection to the packet and sends the packet out on the network • The printer receives the IPsec protected packet and checks the SADB for a matching entry based upon the IP addresses and Security Parameters Index (SPI - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 45
Figure 39 - ESP Let's examine our transmitted IPsec protected packet closely as shown in Figure 37. How in the world is the receiver of this packet going to know what it is? Hmmm... Nothing there really indicates what data this packet is carrying. All is not lost. The valid recipient of this packet - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 46
goals: • Provide proper protection to protocols as referenced by the company's security policy • Provide proper protection to these protocols without bringing down the network or creating an unavailable service for the devices that require it. An incorrectly deployed IPsec policy can easily bring - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 47
rather than using an intermediate Windows Print Server. • HP Jetdirect Printers and MFPs that support IPsec. Second most common platform in use as there are several desktops or laptops for every shared network printer or MFP. • Servers providing common network services - such as DHCP, DNS, WINS, etc - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 48
IPsec policy. The default selections allow for proper operation of the network without too much exposure to security threats. This behavior is IPsec policy where all IP addresses and all IP services are required to use IPsec, the HP Jetdirect device will still get DHCP configured. This behavior - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 49
(e.g., printer.example.com) and turn it into an IP address that devices can use. Some of these devices are IPsec capable and some are not. If we say that "all devices" must support IPsec to utilize these name resolution services, we will have caused a great deal of problems our network administrator - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 50
clearly indicates what traffic is protected and what is not. HP Jetdirect Rule 1: All IP addresses, IPsec Exemptions Services, Allow without IPsec Protection Rule 2: All IP addresses, All services, Require IPsec Where the Service Template "IPsec Exemptions" is created by the administrator and has - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 51
manage because we will want to protect all services to specific IP addresses. We may be tempted reading the "HP Jetdirect Security Guidelines" whitepaper. The "HP Jetdirect Security by using https:// from your favorite browser. Then we'll click the "Networking" tab, and - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 52
Here we are. We can see that Jetdirect supports ten rules and the default rule. Remember, we are going to deploy an IPsec policy that exempts certain services and then secures the rest. Let's click on the "Advanced" button first. Because we are going to exempt these protocols anyway, let's go ahead - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 53
Click "Apply". Back at the main screen. Here we can see that Jetdirect breaks each rule into 3 templates. The first two are for Matching and the last one is for Action. Let's go ahead and click "Add Rules..." 53 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 54
you want this rule to match?" We select "All IP Addresses" and click "Next". Here we answer the question: "For the IP addresses selected, which services do you want this rule to match?" Here we are going to create our own - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 55
SSL/TLS so it doesn't need IPsec to provide it protection. We choose "TCP", "Remote Service", and use a specific Remote Port of 636. Then click "Add" NOTE: Before adding custom services, be sure to check if the service is already present to save you some work. As an example, LDAPS is already pre - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 56
Now we define the same thing for UDP. Click "Add". Now let's click "OK". We are back at the Manage Services screen. We want to choose the services that are exempt from having IPsec required. Check "Bonjour" and scroll down. 56 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 57
Select "BOOTP/DHCP", then select "DHCPv6", then "DNS" for both UDP and TCP. Scroll down. Select "HTTPS", "ICMPv4", "ICMPv6". Scroll down. Select "IGMPv2" 57 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 58
Select "NTP" for both UDP and TCP. Scroll down. Select SLP for UDP as a local service and remote service. Scroll Down. Select "WINS" and "WSDiscovery". Click "OK". 58 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 59
Now we have selected all the services that we would like to be exempt from having to require IPsec protection. Let's give this service template a name, "IPsec Exemptions" and then click "OK". Select "IPsec Exemptions", then click "Next". Select "Allow". Click "Next". 59 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 60
We have created two rules - one for IPv4 and one for IPv6. Select "Create Another Rule". Select "All IP addresses". Click "Next". 60 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 61
Select "All Services". Click Next. Select "Require IPsec". Click "Next". Now we need to specify an IPsec template. This answers the question: "for the IP addresses and their respective services that you want protected by IPsec, what is the IPsec configuration you would like to use?" Click "New". 61 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 62
Here we give the IPsec template a name and select IKEv1. We use the most interoperable IKE settings. For more security, you can customize the IKE settings or use a different default value. Click "Next" Here we select our Authentication scheme, which is Pre-Shared Key. The PreShared Key needs to be - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 63
Select the IPsec template "PSK". Click "Next". Now we have 4 Rules and a very clear IPsec policy about what traffic doesn't have to be protected by IPsec and what traffic is protected by IPsec. Click "Finish". 63 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 64
too much and they may add more protocols to the "IPsec Exemptions" service template. In any case, it is clear to see via the Jetdirect Highly Secure Printing and Imaging Policy for HP Jetdirect Here is a different policy to utilize for HP Jetdirect. This policy values security above interoperability - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 65
not using DHCP, DHCPv6, or other protocols, you can uncheck them for better security. We step through the wizard and select "All IP addresses", "All Services", and our PSK IPsec template. By using the HTTPS failsafe option, we have a deployed a very secure IPsec policy that still allows us to access - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 66
Printing and Imaging Management Policy for HP Jetdirect Here is a different policy to utilize for HP Jetdirect. This policy values security for management services but not for printing services. This policy won't stop an attacker like Jane, but does allow for easier IPsec policy deployment by only - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 67
This indicates that we are only interested in Management protocols. Here we can see that all Jetdirect management services are provided IPsec protection and anything else is allowed. Be sure to enable the failsafe option with this configuration! HTTPS is a management protocol that will - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 68
through a Microsoft configuration. Before doing that, we need to review what we are trying to accomplish. • (1) We want followed by IPsec protection of all services. Now we want to focus on IPsec Configuration Wizard for Pre-Shared Key HP Recommend IPsec Policy to Protect Printing for Desktops - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 69
NOTE: The "IP Security Policy Management" MMC Snap-In discussed in the following slides is available on Microsoft XP/2003/Vista/2008. However, it only protects IPv4 and is limited in its choice of IPsec parameters. For Microsoft Vista and Server 2008, the netsh commands or the Advanced Firewall MMC - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 70
Add a snap-in. Select IP Security Policy Management. 70 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 71
Select "Local Computer" for test/lab setups. Once configurations have been tested, use the Active Directory to deploy IPsec policy. Refer to Microsoft Documentation on recommendations for IPsec policy distribution using Active Directory. Example: http://www.microsoft.com/ipsec Click "Add" then Click - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 72
Select "IP Security Policies on Local Computer". Select "Create IP Security Policy". 72 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 73
Click "Next" Provide a name and description. 73 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 74
Do not activate the default response rule. Click "Finish". 74 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 75
Click "Add..." Click "Next". 75 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 76
Select "This rule does not specify a tunnel". We are dealing with intranet printing and do not need to worry about tunnels. Select "All network connections". 76 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 77
Here we are going to create an IP Filter, which is a way of telling IPsec what traffic to be interested in. Click "Add..." Add name and description. Click "Add...". 77 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 78
Click "Next". Add a description and make sure "Mirrored" is checked. 78 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 79
Source is "My Address" or any IP address on the Client. Destination is "Any IP address". 79 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 80
We want to protect TCP. From any port to port 9100 (the Jetdirect Printing Port). 80 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 81
Click Finish. Click "Ok". 81 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 82
Select our IP filter. We have now told IPsec what traffic to be interested in. Click "Next". Click "Add...". 82 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 83
Click "Next". Add a name and description. Click "Next". 83 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 84
Select "Negotiate security". Select "Do not allow unsecured communication". 84 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 85
/2008 and this MMC snap-in, you MUST set the "Session key settings" to 3600 or higher due to an interoperability issue between Microsoft and HP Jetdirect. 85 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 86
Click "Next". Click "Finish" 86 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 87
Select our Filter Action. Now we have told IPsec what traffic we are interested in and what do to with that traffic. Click "Next". Select "Preshared key" and enter the EXACT SAME preshared key used by Jetdirect. Click "Next". 87 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 88
Click "Finish" Click "Ok" 88 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 89
what we have covered previously. It provides more updated encryption algorithm support such as AES as well as integrated IPv6 support. NOTE: For the best interoperability with HP Jetdirect and Vista, please use Vista with Service Pack 1 or later. Unfortunately, there is no way to specify protocols - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 90
Here all the details for the connection security rule "P9100" are shown. Unfortunately, rules that are created via the netsh command line will appear in the Advanced Firewall UI, but they cannot be managed there because they use attributes only available from the command line. Therefore, to enable - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 91
2008: IPsec Configuration via Advanced Firewall HP Recommend IPsec Policy to Protect Printing Firewall so we can take advantage of seamless support of both IPv4 and IPv6. Here we must in the whitepaper: "Using the Network to Help Secure Printers and MFPs", even this configuration can be much - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 92
Select "Windows Firewall with Advanced Security". Click "Add". Select "Local Computer". 92 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 93
Click "OK". Select "Connection Security Rules". 93 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 94
Click "New Rule..." Select "Server-toserver". Click "Next". 94 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 95
device. Click "OK". NOTE: This endpoint needs to be an IPv4 address. An IPv6 address can only be used when Microsoft Vista is updated to Service Pack 1 or later. It is highly recommended that all the IP addresses on - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 96
Select "Require authentication for inbound and outbound connections". Click "next". Select "Preshared Key" and enter the same key as configured on Jetdirect. Click "Next". 96 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 97
Select all of the profiles. Click "Next". Give the rule a name and description. Click "Finish". 97 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 98
This rule is enabled by default. Click "Windows Firewall with Advanced Security" on the left, then click the link "Windows Firewall Properties" in the middle. 98 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 99
not even happen. NOTE: It appears that Vista with Service Pack 1 will allow ICMPv6 Neighbor Discovery packets to be both Jetdirect and Microsoft Windows. The only problem that we have is that we have been using - which isn't recommended by Microsoft or HP for production deployments. We need to cover - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 100
certificate - which indirectly means that this web site may not be the web site we think it is. There are two warning icons associated with this dialog. The help text by the first warning icon prompts us to view the certificate. Let's click on "View Certificate". Figure 45 - Certificate Details 100 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 101
given state. A person that goes to the DMV to get a driver's license must pass a series of tests that helps the DMV determine if they are fit to Security Alert dialog is troubling because it is indicative of a trust problem. In the terms of our analogy, it would be like a driver, who has been pulled - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 102
Symmetric cryptography commonly has two attributes associated with it: • It performs well - it is fast and easy to implement • It has a key distribution problem - how do you get the symmetric key to everyone that needs it in a secure way? Asymmetric cryptography is also available and functions very - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 103
We get the flexibility of asymmetric cryptography and the speed of symmetric cryptography. Now we only have to solve the trust problem. In order to solve the trust problem, five things will need to be discussed: • A certificate authority - a trusted third party that creates digital certificates from - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 104
Jack's private key, which no one should know but Jack, John can be sure that Jack was the one that sent it. We still have a problem - How does John know that Jack's public key really belongs to the person that he knows as "Jack"? There are many people in the world - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 105
Jack Create Key Pair Jack's Public Key Jack's Private Key Identity Info + CA's Public Key Jack Jack's Private Key (Stays Private) Jack's Public Key Certificate Request Certificate Authority CA's Private Key (Also performs Identity Verification on Jack) Identity Info + CA Info + Jack's - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 106
Figure 51 - Public Key Certificates Here we can see that everyone's public key certificate is, well - um, public. The important thing to note is that the certificate authority also has a public key certificate that identifies itself. This certificate is signed with its own private key and is a "self - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 107
the Intranet, we will be talking about Microsoft's certificate authorities later on. HP Jetdirect and Public Key Certificates Now that we have covered some basics around to create a Certificate Template. A certificate template is the guide that controls how the certificates are created. 107 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 108
There is a workaround for this problem as well as a fix. can be created for services. The Microsoft CA HP Jetdirect. Note: The certificate template functionality described below is only available for the "Enterprise CA". It requires the Certificate Template snap-in to be loaded into MMC. A printer/MFP - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 109
Provide the names you would like the certificate template to have. Select the "Allow private key to be exported" checkbox in the Request Handling tab. 109 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 110
Select the Application Policies extension in the Extensions tab. Click Edit. Click Add... 110 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 111
Select Client Authentication, then click OK. Click OK. 111 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 112
Click OK. Now we have created a new certificate template, we need to enable it to be used by the Certification Authority. Select Certificate Templates under Certification Authority. Now right click and select New and then "Certificate Template to Issue". 112 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 113
and click OK. Check the Certificate Templates folder in the Certification Authority snapin in MMC and make sure that the HP Jetdirect template is present. Done. More than likely, the creation of the certificate template will be done by someone in the PKI team. Once this - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 114
From the main web interface, click "Download a CA certificate..." Select "Current [RootCA]", then DER (or Base 64 if you are using an older Jetdirect product), then click "Download CA certificate", 114 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 115
Click Save. Name the file "cacert.cer" Once we have the CA cert on the desktop, we can install it on Jetdirect. Let's bring up the Embedded Web Server and go to the Networking Tab Go to the Certificate Wizard. 115 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 116
Select "Install CA Certificate" Point to the cacert.cer file and click Finish! Done! NOTE: this process will need to be done on every HP Jetdirect that will be utilizing IPsec with Certificate Authentication We also want to install the CA certificate chain on every computer system that will be - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 117
Click Yes. Done Creating a Jetdirect CSR and Installing the Certificate We've installed the Root CA on every Jetdirect. Now we need to install the Identity Certificate on each Jetdirect. Each Jetdirect will have a unique certificate and we need to create a certificate signing request. Starting with - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 118
Click on the "Networking" tab and go to "Authorization" and then "Certificates". Click "Configure" under the Jetdirect Certificate section. Select "Create Certificate Request" and then click "Next". Enter in the fields that describe the devices. Click "Next". 118 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 119
Jetdirect generates the public/private key pair, which can take a little while. You can save the file, or you can simply copy the text starting and including "----BEGIN CERTIFICAT REQUEST-----" up to and including the last five dashes of the "END CERTIFICATE REQUEST-----" Moving back to the web - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 120
Here we paste in our Certificate Request and select the HP Jetdirect certificate template. Then click "Submit". Now we have our certificate. Most Jetdirect cards support both DER and Base64, but all support Base64. Simply click "Download Certificate". Save the certificate. 120 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 121
Going back to the Jetdirect Certificate Wizard, we select the "Install Certificate" option. Click "Next". Select the certificate file saved previously. Click "Finish". NOTE: starting with V.38.XX firmware and later, the private key can be protected from export when the certificate is first installed - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 122
start off using the recommended Jetdirect deployment of the "IPsec Exemptions" service template, as was done in the Pre-Shared Key screen shots. This screen shots that are not relevant to certificate authentication. HP Jetdirect IPsec Configuration Wizard: Certificate Authentication The "IPsec - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 123
Select All Services, Click "Next". Select "Require traffic...." Click "Next" Click "New" 123 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 124
Here we have named the IPsec template "Certificates". Click "Next" Select Certificates as the authentication for IKE. NOTE: this process assumes that you have already installed the Certificates as outlined in the previous section. Select the "Certificates" template. Click "Next". 124 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 125
Select "Finish". That's all there is to configuring certificate authentication on Jetdirect. Once we have the certificate files from the CA, it really isn't much harder than configuring IPsec for pre-shared key authentication. Let's go through the changes to our Microsoft configuration. Microsoft - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 126
Firewall with Advanced Security - a very similar configuration. One possible problem that you may run across is that the Certificate Authority that was Store of the Windows machine. This will happen if you forgot to download the certificate chain from the Certificate Authority. To fix this, since we - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 127
Select "Import..." Click "Next" 127 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 128
Specify the filename of the CA's public key certificate. Click "Next". Specify that the certificate should go into the "Trusted Root Certification Authorities" store. Click "Next". 128 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 129
Click "Finish" And there it is! Windows XP/2003/Vista/2008: IPsec Identity Certificate You should also make sure that your machine has a certificate that can be used for IPsec - remember, it has to send a certificate to Jetdirect to authenticate itself. If the machine doesn't have a suitable - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 130
have to jump through a few hoops to receive the benefits of Kerberos. Since HP Jetdirect is not a member of an AD domain as a computer object, it "Realm", in Kerberos terminology. Jetdirect supports Intra-Realm authentication but does not support cross-Realm authentication. Essentially, any - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 131
what name the KDC knows it by • The principal needs to know what realm it belongs to • The principal needs to know the network address of the Authentication Service • The principal needs to know he current time - via a time server or the principal's clock both of which have to be synchronized to - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 132
other companies do. He simply tells the members of DSG: simply put your membership identity in the text fields of any of the "free" dating services that you currently are a member of. This process allowed our entrepreneur not to invest in web sites and databases and allowed DSG's members to utilize - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 133
includes a Ticket Granting Ticket (TGT). Vista uses this TGT in the Step 2, this time communicating with the Ticket Granting Service (TGS) with a request (TGS-REQ) to get a service ticket for the application server. Vista includes an Authenticator with this message as well. The TGSREP from the TGS - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 134
Figure 53 - AS-REQ Vista and the KDC both have the exact same key. Vista sends an AS-REQ that is basically saying "I want a TGT from the TGS. It is also saying "I'm proving to the KDC that I'm Vista because I'm going to encrypt a timestamp with my secret key that only myself and the KDC knows". If - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 135
Session key. Notice that it also exists in the TGT. Let's see how it is used - refer to Figure 55 - TGSREQ. Figure 55 - TGS-REQ Here we can see that the Authenticator is used to communicate to the TGS in the TGS-REQ packet. The Authenticator is using the session key that was sent back in the AS-REP - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 136
Figure 56 - TGS-REP Here we see the application server ticket is just an "opaque blob" to Vista as well. However, using the TGS/Vista session key, information about the application server ticket is also included so that Vista can communicate with the application server. Kerberos tries to use session - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 137
Let's move on to actually configuring Kerberos for use in a production environment. HP Jetdirect IPsec Configuration Wizard: Kerberos Authentication Because Jetdirect is not a member of the First, we need to load the Support Tools for Windows 2003 in order to get a program called "ktpass.exe". 137 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 138
Here is a Support Pack executable for Windows 2003. With the latest service packs, this file is often on the CD so you don't have to download it. Click "Next". 138 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 139
Deal with the license agreement.... Enter your credentials. 139 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 140
Figure out where you want to put it. All done - relatively painless! Once that has been loaded, we will need to create a user object (not a computer object) that will represent Jetdirect in the Active Directory. Where the object is located in the directory tree doesn't matter as long as it is in the - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 141
Launch Active Directory Users and Computers Create a new user that will represent Jetdirect. We'll name it "finance" in this example. 141 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 142
Provide a password and change some of the options. Remember, this will be a Jetdirect device rather than an actual user. All done. 142 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 143
Still need one more parameter to configure. Highlight the user, right-click, and select "properties". Click the "Account" Tab. Select "Use DES encryption" and then click "Apply". 143 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 144
Got to the EWS of the Jetdirect card and setup the hostname and domain name. In this example, we are going to use a hostname of finance and a domain name of "example.internal". Moving over to DNS, we setup the DNS records for the Jetdirect device. Here is the "A" record. And here is the PTR record. - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 145
Not quite done jumping through hoops..... Here we want to create a krb5.conf file that contains some information for Jetdirect. You can do this in notepad if you wish. Here are the contents for a Jetdirect card that we will configure later. Now we want to run our ktpass tool to map an Active - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 146
Here is the output of the ktpass command. Don't worry about the "WARNING". Now we can use the file "finance.ketab" to upload our Kerberos configuration. Okay - we've jumped through the necessary hoops to get Jetdirect represented in the AD as well as in the KDC. Now let's go ahead and configure a - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 147
Select "All IP Addresses". Click "Next" Select "All Services". Click "Next". Click "New". 147 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 148
Provide a template name and select an IKE defaults template. Click "Next". Select Kerberos and click "Configure..." Select "Import configuration files". Provide the krb5.conf and finance.keytab files. Click "Next". 148 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 149
If the files loaded correctly, then we will be back at the main page for Authentication. Click "View..." Click "Validate...." It is very important that the validation is successful at this point, otherwise IPsec will not work. 149 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 150
Click "Next". Select the Kerberos template we just created. Click "Next". 150 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 151
Jetdirect. Let's go back a few screens to where we entered the configuration files. Instead of saying "import configuration files, we can choose to manually specify the configuration information. You still need to run ktpass, but instead of worrying about the files, you can just go ahead and enter - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 152
krb5.conf file can be used here, rather than the files themselves. CAPITALIZATION of the Principal is very important! Okay, those are the two manual methods for configuration Kerberos on Jetdirect. Once we've got that setup, now we need to go back to the Microsoft configuration and setup Kerberos - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 153
Windows Vista/Server 2008: Advanced Firewall In the MMC snap in "Windows Firewall with Advanced Security", we would select the "Advanced" authentication method and then hit "Customize" on the Server-toServer configuration. 153 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 154
manually configuring IPsec on Jetdirect using the Embedded Web Server. We can also batch configure IPsec from Web Jetadmin 10.X (hereafter, WJA10) with any HP Jetdirect IPsec device at V.36.11 and later. Yeah! Currently, only Kerberos and Pre-Shared Key are supported via WJA10. - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 155
This whitepaper won't talk about the extensive features in WJA10 except for configuring IPsec. To learn more about WJA10, go to http://www.hp.com/go/webjetadmin. One thing we still need to do is setup our Jetdirect cards in DNS. The next three screenshots are repeats regarding the - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 156
as a file. The IPsec package will be available free for WJA10 and can be found using WJA10's application management features or via the http://www.hp.com/go/webjetadmin web site. In case we need to install the IPsec plugin. Select "Application Management" on the bottom left, then "Available Packages - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 157
Select the filename. Click "Next". Click "Done". 157 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 158
Now we see the IPsec package as an "Available Package". Now select "Install" to install it into WJA10. Use the appropriate administrative credentials for the WJA10 server. Click "Next". 158 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 159
Click "Next". Here are the results. Click "Close". 159 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 160
Let's highlight our device and then click the "Config" tab at the bottom. NOTE: In the slides that follow, a full recommended deployment of IPsec for a Jetdirect device will be shown using WJA10. Expand the "Security" navigation link and then select "IPsec Policy". This screen looks familiar! Click - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 161
Uncheck the Broadcast and Multicast bypass boxes. Click "OK". Back to the main screen - click the "Add Rules..." button. 161 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 162
Select "All IP Addresses". Click "Next" Select "New..." 162 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 163
Select "Manage Services..." Select the services that are recommended as "IPsec Excemptions". NOTE: There are more screen shots here but we've deleted them since they are simply showing the other IPsec service Exemptions that we've covered previously. We are going to skip right to the end of the - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 164
Here are all the services that we don't care whether they are provided IPsec protection or not. Click "OK". Select the service template "IPsec Excemptions". 164 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 165
Select "Allow". Click "Next". Click "Create Another Rule". 165 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 166
Select "All IP Addresses". Click "Next". Select "All Services". Click "Next". 166 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 167
Select "Require ...." Click "Next". Name our Template Kerberos and then click "Next". 167 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 168
Select "Kerberos" then click "Configure...." Provide the credentials of the user that is able to create User Objects in the AD for the given OU Path. Provide the REALM. There is no need to provide the principal names as WJA10 will be creating the users for you. Of course, we need to provide the KDC - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 169
Click "Next" Select "Kerberos" and click "Next". 169 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 170
Here is our summary. Click "Finish". Check "enable IPsec" and check "enable" by all of our rules we created. Then click "Apply..." 170 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 171
Select "Yes" for enable and "No" for failsafe. Click "OK" Click "Configure Devices". Done! 171 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 172
computers, for the OU Printers, we can see the user object that was created. Summary We've sure covered a lot of material! HP hopes that this whitepaper security policy. IPsec doesn't solve all problems around security, but it can definitely solve some types of problems better than others. If you've - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 173
Appendix A: IKE Templates When configuring the IPsec template, we just selected "High interoperability/low security" for the IKE defaults. What if we want to do something different with IKE? Well, here are the options. There are 5 total - High/Low, Med/Med, Low/High, High/Adv, and Custom where you - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 174
Here are the IKE settings for Med/Med Here are the IKE settings for Low/High 174 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 175
Here are the IKE settings for High/Adv. What if you don't like these defaults? You can go "Custom". Select "Specify Custom Profile" then click "Next". 175 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 176
Here we specify a preshared key, but any authentication parameter will do. Click "Next". Here are Jetdirect's IKE Phase 1 parameters. If you click on "edit" for the DH groups.... Here are the DH group settings for IKE Phase 1. You can select which DH groups can be used. 176 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 177
Here are the Quick Mode parameters. Here are the Advanced parameters. All Done! 177 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 178
Appendix B: Troubleshooting Web Jetadmin and Kerberos WJA10 uses SSL to communicate with AD. If this isn't setup correctly, the WJA10 IPsec configuration may fail. Using a program loaded with the Support Tools called "LDP.EXE", we can test this out before using WJA10. Run LDP Select "Connect..." 178 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 179
Enter the KDC FQDN. NOTE: if you enter the IP the LDAPS server certificate probably has the FQDN as the common name which means this step will fail. Be sure to use the FQDN. Here is a sample screen of output after the connection. Now select "Bind..." from the Connection menu. Enter the credentials. - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 180
Should see "Authenticated" at the bottom. Do a simple search by selecting "Search" from the menu. 180 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 181
do this, we can probably create users in that OU. That would be the next step using LDP. Appendix C: Importing a Certificate For versions of HP Jetdirect firmware that are earlier than V.36.XX, you will need to import a certificate rather than use the Certificate Signing Request. For the Microsoft - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 182
Click "advanced certificate request" 182 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 183
Click "Create and submit a request to this CA". 183 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 184
Be sure to select the Certificate Template "HP Jetdirect" and to check the checkbox entitled "Mark keys as exportable". Click Yes. 184 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 185
Click "Install this certificate" to install it on your local computer. We will export it and then delete it from this computer later. Click Yes. 185 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 186
Done. At this point, we want to export the certificate so that it can be loaded with its private key into Jetdirect. We need to bring up MMC again and load the Certificates snap-in. 186 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 187
Go to the File Menu and select Add/Remove Snap-In. Click "Add..." 187 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 188
Click "Certificates" Click "My user account" 188 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 189
Click "Local Computer" Select the folder "Certificates" under "Personal". Highlight the Jetdirect certificate issued. Right Click and select "Export..." 189 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 190
that is not compatible with Jetdirect's CSR and this resulted in Jetdirect refusing to accept the certificate during its installation. Jetdirect has since addressed this problem starting with version V.36.11. Using V.36.11 and later, certificates issued from the 190 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 191
Enterprise CAs using a Jetdirect CSR file are accepted. As this process is more secure and preferred, we will cover it later in the whitepaper. Type a password to protect the private key. Click "Next". Name the file "jdcert.pfx" and click "Next" 191 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 192
Click Finish Click Ok. To import the certificate in Jetdirect Click "Configure" under the heading "Jetdirect Certificate". 192 - HP CM8000 | Practical IPsec Deployment for Printing and Imaging Devices - Page 193
Select "Import certificate and private key". Click "Next". Browse the file name of the Jetdirect certificate and supply the password that you used when exporting the certificate earlier. We are done! 193
1
Practical IPsec Deployment for Printing and Imaging Devices
June 2008
Table of Contents:
Introduction
.....................................................................................................................................
2
A Parable: Confidentiality, Authentication, and Integrity
.......................................................................
2
IPsec and Virtual Private Networks
.....................................................................................................
5
The Intranet Threat Model
.................................................................................................................
8
Too Easy: The Repeater
..................................................................................................................
10
Too Easy: The Flood
.......................................................................................................................
13
Too Easy: The Mirror Port
...............................................................................................................
16
Too Easy: MITM Active Sniffing
.......................................................................................................
17
Too Easy: MITM Data Injection
........................................................................................................
22
IPsec Basics
...................................................................................................................................
23
IPsec Basics: IPsec Policy – Packet Matching
.....................................................................................
25
IPsec Basics: IPsec Policy – Action-on-Match
......................................................................................
26
IPsec Basics: Internet Key Exchange and the SADB
............................................................................
29
IKE Authentication: Pre-shared Key
...................................................................................................
35
IKE Phase 2/Quick Mode
...............................................................................................................
36
IKE in Action
.................................................................................................................................
39
IPsec Basics: Receiving an IPsec Protected Packet
...............................................................................
44
IPsec Guidelines for Printing and Imaging Devices
.............................................................................
46
HP Jetdirect IPsec Configuration Wizard: Pre-Shared Key Authentication
..............................................
51
Microsoft IPsec Configuration Wizard for Pre-Shared Key
...................................................................
68
Microsoft Vista/Server 2008: IPsec Configuration via Netsh
...............................................................
89
Microsoft Vista/Server 2008: IPsec Configuration via Advanced Firewall
.............................................
91
Public Key Infrastructure and Public Key Certificate Basics
................................................................
100
HP Jetdirect and Public Key Certificates
..........................................................................................
107
IKE Authentication: Public Key Certificates
......................................................................................
107
The Microsoft Certificate Authority Environment
...............................................................................
107
Creating a Certificate Template
.....................................................................................................
108
Retrieving and Installing a CA Certificate
........................................................................................
113
Creating a Jetdirect CSR and Installing the Certificate
......................................................................
117
HP Jetdirect IPsec Configuration Wizard: Certificate Authentication
...................................................
122
Microsoft Windows: Certificate Authentication
................................................................................
125
Kerberos, Active Directory, and Jetdirect
.........................................................................................
130
Kerberos Basics
...........................................................................................................................
131
whitepaper