HP CM8000 Practical IPsec Deployment for Printing and Imaging Devices - Page 45
ESP
 |
View all HP CM8000 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 45 highlights
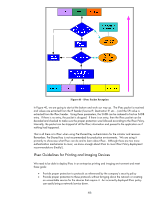
Figure 39 - ESP Let's examine our transmitted IPsec protected packet closely as shown in Figure 37. How in the world is the receiver of this packet going to know what it is? Hmmm... Nothing there really indicates what data this packet is carrying. All is not lost. The valid recipient of this packet can go through this algorithm shown in Figure 40. 45

45
Figure 39 - ESP
Let’s examine our transmitted IPsec protected packet closely as shown in Figure 37.
How in the world
is the receiver of this packet going to know what it is? Hmmm… Nothing there really indicates what
data this packet is carrying.
All is not lost.
The valid recipient of this packet can go through this
algorithm shown in Figure 40.