Netgear Wg111v2 WG111v2 User Manual - Page 60
Shared Key Authentication, 11 Authentication, Open System Steps - adapter does what
 |
UPC - 012495805855
View all Netgear Wg111v2 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 60 highlights
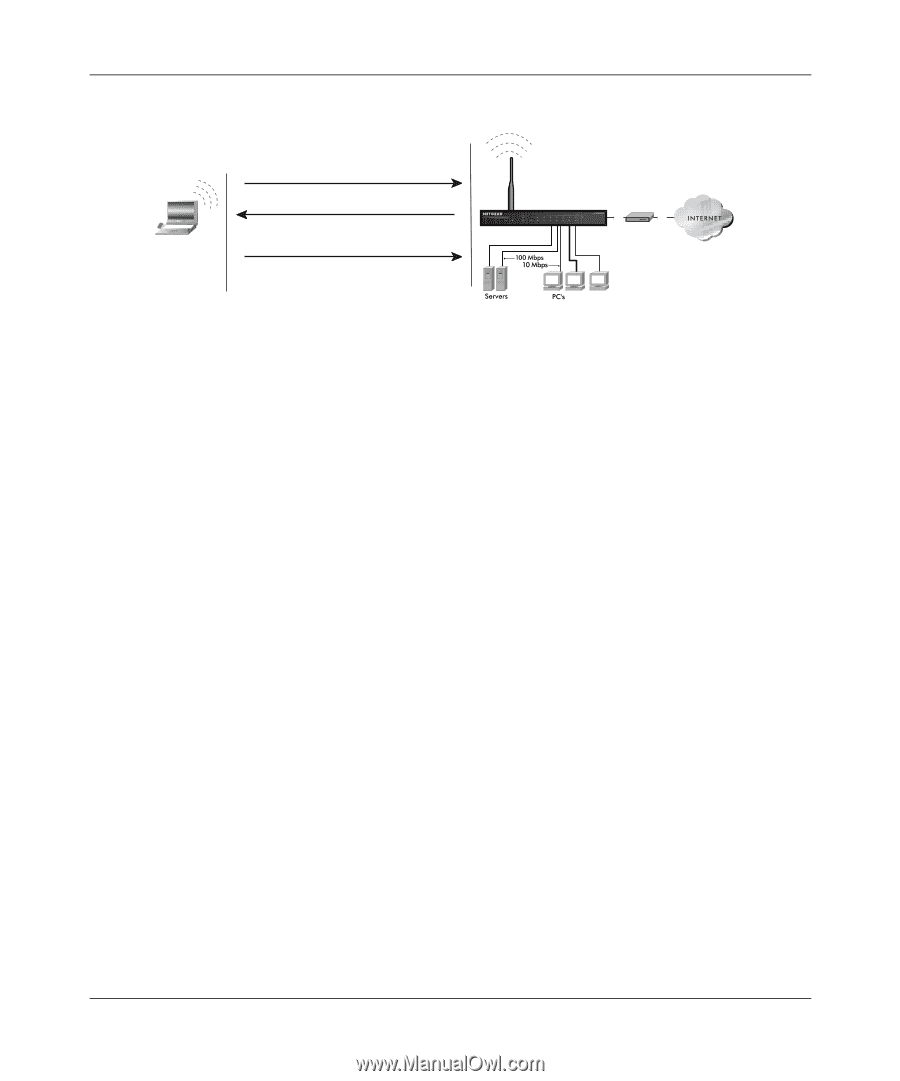
User Manual for the NETGEAR 54 Mbps Wireless USB 2.0 Adapter WG111 802.11 Authentication Open System Steps 1) Authentication request sent to AP 2) AP authenticates Client attempting to connect 3) Client connects to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem Figure 4-1: 802.11 open system authentication Shared Key Authentication The following steps occur when two devices use Shared Key Authentication: 1. The station sends an authentication request to the access point. 2. The access point sends challenge text to the station. 3. The station uses its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the access point. 4. The access point decrypts the encrypted text using its configured WEP Key that corresponds to the station's default key. The access point compares the decrypted text with the original challenge text. If the decrypted text matches the original challenge text, then the access point and the station share the same WEP Key and the access point authenticates the station. 5. The station connects to the network. If the decrypted text does not match the original challenge text (i.e., the access point and station do not share the same WEP Key), then the access point will refuse to authenticate the station and the station will be unable to communicate with either the 802.11 network or Ethernet network. This process is illustrated in below. B-4 Wireless Networking Basics 202-10026-01