ZyXEL P-662H-D3 User Guide - Page 225
Keep Alive, VPN, NAT, and NAT Traversal
 |
View all ZyXEL P-662H-D3 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 225 highlights
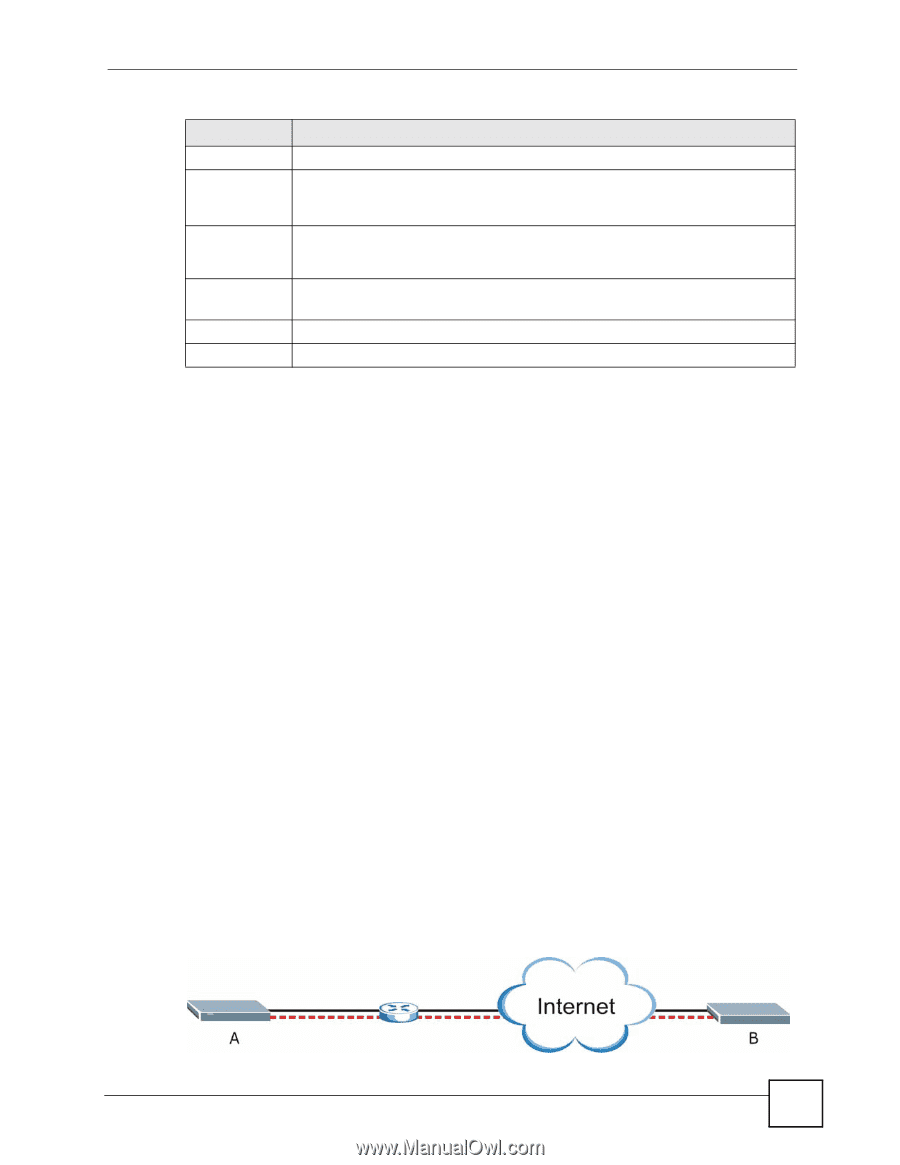
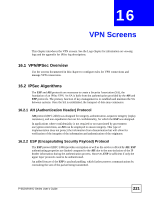
Chapter 16 VPN Screens Table 87 VPN Setup LABEL DESCRIPTION Encap. This field displays Tunnel or Transport mode (Tunnel is the default selection). IPSec Algorithm This field displays the security protocols used for an SA. Both AH and ESP increase ZyXEL Device processing requirements and communications latency (delay). Secure Gateway IP This is the static WAN IP address or URL of the remote IPSec router. This field displays 0.0.0.0 when you configure the Secure Gateway Address field in the VPNIKE screen to 0.0.0.0. Modify Click the Edit icon to go to the screen where you can edit the VPN configuration. Click the Delete icon to remove an existing VPN configuration. Apply Click Apply to save your changes back to the ZyXEL Device. Cancel Click Cancel to begin configuring this screen afresh. 16.6 Keep Alive When you initiate an IPSec tunnel with keep alive enabled, the ZyXEL Device automatically renegotiates the tunnel when the IPSec SA lifetime period expires (see Section 16.12 on page 233 for more on the IPSec SA lifetime). In effect, the IPSec tunnel becomes an "always on" connection after you initiate it. Both IPSec routers must have a ZyXEL Device-compatible keep alive feature enabled in order for this feature to work. If the ZyXEL Device has its maximum number of simultaneous IPSec tunnels connected to it and they all have keep alive enabled, then no other tunnels can take a turn connecting to the ZyXEL Device because the ZyXEL Device never drops the tunnels that are already connected. When there is outbound traffic with no inbound traffic, the ZyXEL Device automatically drops the tunnel after two minutes. 16.7 VPN, NAT, and NAT Traversal NAT is incompatible with the AH protocol in both transport and tunnel mode. An IPSec VPN using the AH protocol digitally signs the outbound packet, both data payload and headers, with a hash value appended to the packet, but a NAT device between the IPSec endpoints rewrites the source or destination address. As a result, the VPN device at the receiving end finds a mismatch between the hash value and the data and assumes that the data has been maliciously altered. NAT is not normally compatible with ESP in transport mode either, but the ZyXEL Device's NAT Traversal feature provides a way to handle this. NAT traversal allows you to set up an IKE SA when there are NAT routers between the two IPSec routers. Figure 130 NAT Router Between IPSec Routers P-662H/HW-D Series User's Guide 225