ZyXEL P-662H-D3 User Guide - Page 464
Table 194, Table 193
 |
View all ZyXEL P-662H-D3 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 464 highlights
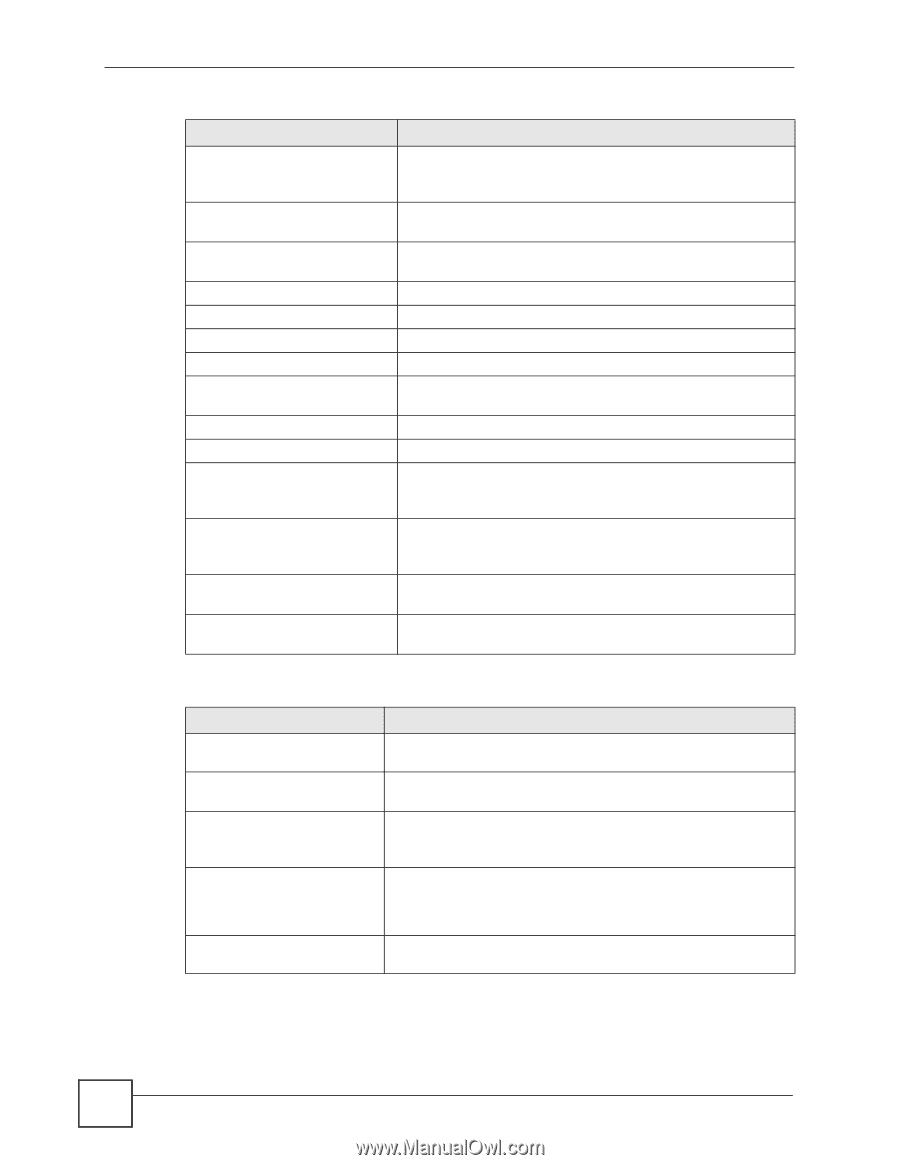
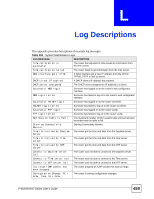
Appendix L Log Descriptions Table 193 Attack Logs (continued) LOG MESSAGE DESCRIPTION ip spoofing - WAN [TCP | UDP | IGMP | ESP | GRE | OSPF] The firewall detected an IP spoofing attack on the WAN port. ip spoofing - WAN ICMP (type:%d, code:%d) The firewall detected an ICMP IP spoofing attack on the WAN port. For type and code details, see Table 200 on page 470. icmp echo: ICMP (type:%d, The firewall detected an ICMP echo attack. For type and code code:%d) details, see Table 200 on page 470. syn flood TCP The firewall detected a TCP syn flood attack. ports scan TCP The firewall detected a TCP port scan attack. teardrop TCP The firewall detected a TCP teardrop attack. teardrop UDP The firewall detected an UDP teardrop attack. teardrop ICMP (type:%d, code:%d) The firewall detected an ICMP teardrop attack. For type and code details, see Table 200 on page 470. illegal command TCP The firewall detected a TCP illegal command attack. NetBIOS TCP The firewall detected a TCP NetBIOS attack. ip spoofing - no routing entry [TCP | UDP | IGMP | ESP | GRE | OSPF] The firewall classified a packet with no source routing entry as an IP spoofing attack. ip spoofing - no routing entry ICMP (type:%d, code:%d) The firewall classified an ICMP packet with no source routing entry as an IP spoofing attack. vulnerability ICMP (type:%d, code:%d) The firewall detected an ICMP vulnerability attack. For type and code details, see Table 200 on page 470. traceroute ICMP (type:%d, The firewall detected an ICMP traceroute attack. For type and code:%d) code details, see Table 200 on page 470. Table 194 IPSec Logs LOG MESSAGE Discard REPLAY packet Inbound packet authentication failed Receive IPSec packet, but no corresponding tunnel exists Rule idle time out, disconnect WAN IP changed to DESCRIPTION The router received and discarded a packet with an incorrect sequence number. The router received a packet that has been altered. A third party may have altered or tampered with the packet. The router dropped an inbound packet for which SPI could not find a corresponding phase 2 SA. The router dropped a connection that had outbound traffic and no inbound traffic for a certain time period. You can use the "ipsec timer chk_conn" CI command to set the time period. The default value is 2 minutes. The router dropped all connections with the "MyIP" configured as "0.0.0.0" when the WAN IP address changed. 464 P-662H/HW-D Series User's Guide