ZyXEL P-794H User Guide - Page 193
Security Logging Configuration, Table 89
 |
View all ZyXEL P-794H manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 193 highlights
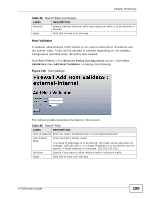
Chapter 15 Security PROTOCOL TCP ICMP TCP TCP UDP ATTACK NAME IMAP SYN/FIN Scan ((Port scan attack) SMURF (if victim protection is set; SMURF Attack) SYN Flood (if scanning threshold is exceeded; SYN/FIN/RST Flood ) Net Bus Scan (Port scan attack) Back Orifice Scan (Port scan attack) 15.2.4.4 Security Logging Configuration Click Security Logging Configuration to show the following screen. You can configure your security logging settings. Figure 122 Security Logging Configuration The following table describes the labels in this screen. Table 89 Security Logging Configuration LABEL DESCRIPTION Security Logging State Disable Security Logging This shows the condition of security logging. Click Disable Security Logging if you want to disable it. Click Enable Security Logging if you want to ensable it. Security Event Logging States Logging Type This show the type of logging. Status This shows the status of the logging. P-794H User's Guide 193