D-Link DGS-1500-20 User Manual - Page 71
Security > Safeguard Engine, Security > Storm Control, Security > ARP Spoofing Prevention
 |
View all D-Link DGS-1500-20 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 71 highlights
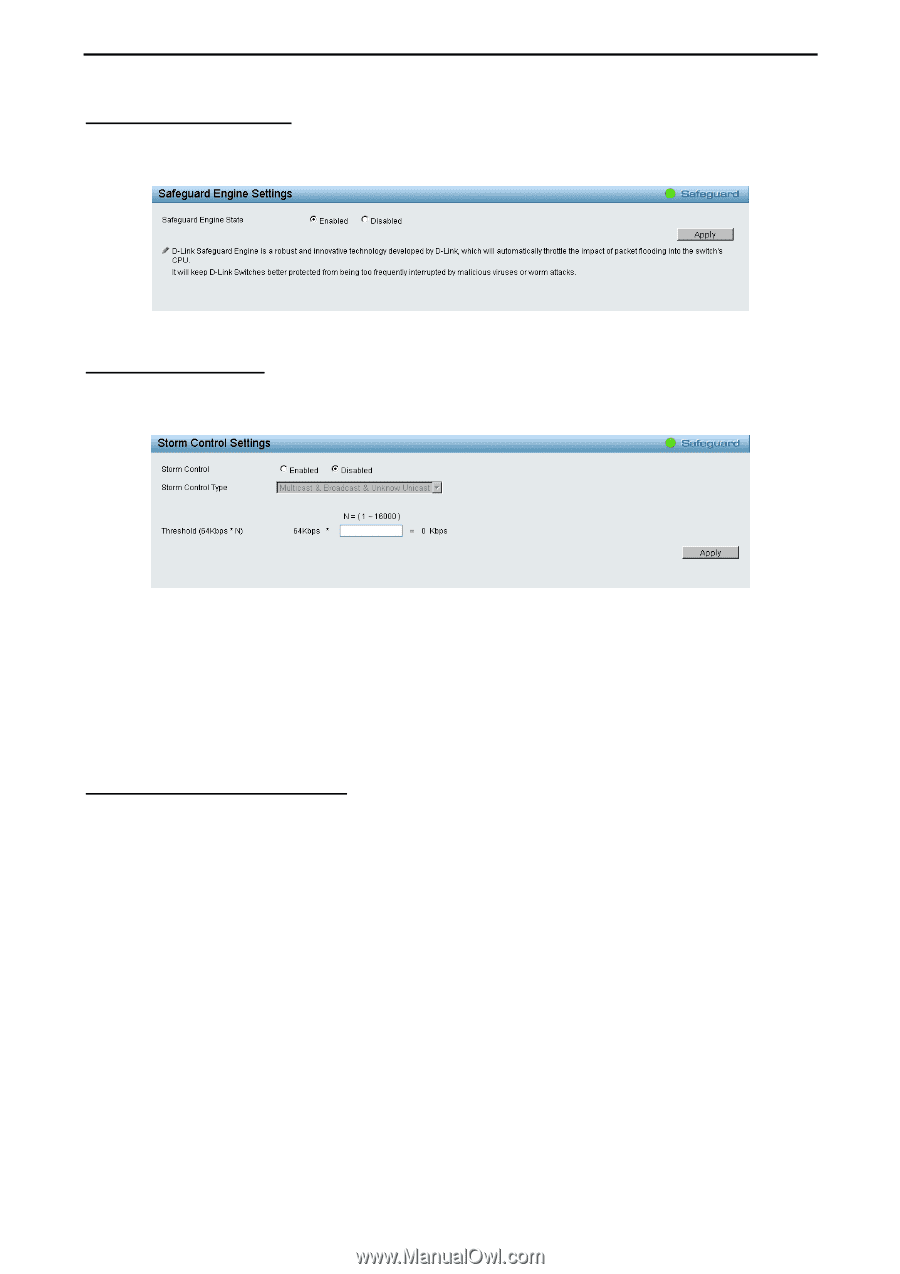
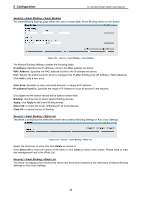
5 Configuration D-Link Web Smart Switch User Manual Security > Safeguard Engine D-Link's Safeguard Engine is a robust and innovative technology that automatically throttles the impact of packet flooding into the switch's CPU. This function helps to protect the Web-Smart Switch from being interrupted by malicious viruses or worm attacks. This option is enabled by default. Figure 5.84 - Security > Safeguard Engine Security > Storm Control The Storm Control feature provides the ability to control the receive rate of broadcast, multicast, and unknown unicast packets. Once a packet storm has been detected, the Switch will drop packets coming into the Switch until the storm has subsided. Figure 5.85 - Security > Storm Control Storm Control Type: User can select the different Storm type from Broadcast Only, Multicast & Broadcast and Broadcast & Multicast & Unknown Unicast. Threshold: If storm control is enabled (default is disabled), the threshold can be set here. The threshold is from of 64 ~ 1,024,000 Kbit per second, with steps (N) of 64Kbps. N can be from 1 to 16000. Click Apply for the settings to take effect. Security > ARP Spoofing Prevention ARP spoofing, also known as ARP poisoning, is a method to attack an Ethernet network by allowing an attacker to sniff data frames on a LAN, modifying the traffic, or stopping the traffic (known as a Denial of Service - DoS attack). The main idea of ARP spoofing is to send fake or spoofed ARP messages to an Ethernet network. It associates the attacker's or random MAC address with the IP address of another node such as the default gateway. Any traffic meant for that IP address would be mistakenly re-directed to the node specified by the attacker. A common DoS attack today can be done by associating a nonexistent or specified MAC address to the IP address of the network's default gateway. The malicious attacker only needs to broadcast one gratuitous ARP to the network claiming to be the gateway, so that the whole network operation is turned down as all packets to the Internet will be directed to the wrong node. The ARP Spoofing Prevention function can discard the ARP Spoofing Attack in the network by checking the gratuitous ARP packets and filtering those with illegal IP or MAC addresses. 65