HP Brocade BladeSystem 4/24 HP StorageWorks Fabric OS 6.1.1 administrator guid - Page 65
Protecting the local user database from distributions, Configuring password policies
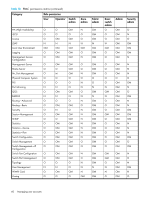
 |
View all HP Brocade BladeSystem 4/24 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 65 highlights
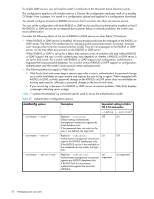
where is a semicolon-separated list of switch Domain IDs, switch names, or switch WWN addresses. You can also specify -d "*" to send the local user database only to Fabric OS 5.2.0 or later switches in the fabric. Protecting the local user database from distributions Fabric OS 5.2.0 and later allow you to distribute the user database and passwords to other switches in the fabric. When the switch accepts a distributed user database, it replaces the local user database with the user database it receives. By default, switches accept the user databases and passwords distributed from other switches. This section explains how to protect the local user database from being overwritten. To accept distribution of user databases on the local switch: 1. Connect to the switch and log in using an admin account. 2. Issue the following command: fddCfg --localaccept PWD where PWD is the user database policy. To reject distributed user databases on the local switch: 1. Connect to the switch and log in using an admin account. 2. Issue the following command: fddCfg --localreject PWD Configuring password policies The password policies described in this section apply to the local switch user database only. Configured password policies (and all user account attribute and password state information) are synchronized across CPs and remain unchanged after an HA failover. Password policies can also be manually distributed across the fabric (see "Distributing the local user database" on page 64). Following is a list of the configurable password policies: • Password strength • Password history • Password expiration • Account lockout All password policies are enforced during logins to the standby CP. However, you may observe that the password enforcement behavior on the standby CP is inconsistent with prior login activity. This is because password state information from the active CP is automatically synchronized with the standby CP, thereby overwriting any password state information that was previously stored there. Also, password changes are not permitted on the standby CP. Password authentication policies configured using the passwdCfg command are not enforced during initial prompts to change default passwords. Setting the password strength policy The password strength policy is enforced across all user accounts, and enforces a set of format rules to which new passwords must adhere. The password strength policy is enforced only when a new password is defined. The total of the other password strength policy parameters (lowercase, uppercase, digits, and punctuation) must be less than or equal to the value of the MinLength parameter. Use the following attributes to set the password strength policy: • Lowercase Specifies the minimum number of lowercase alphabetic characters that must appear in the password. The default value is zero. The maximum value must be less than or equal to the MinLength value. • Uppercase Specifies the minimum number of uppercase alphabetic characters that must appear in the password. The default value is zero. The maximum value must be less than or equal to the MinLength value. Fabric OS 6.1.1 administrator guide 65