Symantec 10268947 User Guide - Page 20
About detection, Core Architecture of Symantec Network Security
 |
UPC - 037648243766
View all Symantec 10268947 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 20 highlights
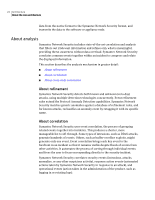
20 Architecture About the core architecture Figure 2-1 Core Architecture of Symantec Network Security Refinement Correlation Policy Application Automated Response Network Traffic Protocol Anomaly Detection Stateful Signatures User-defined Signatures DoS Detection External Sources Scan Detection EDP Detection Analysis This section describes the following topics: ■ About detection ■ About analysis ■ About response Response About detection Symantec Network Security uses multiple methods of threat detection that provide both broad and deep detection of network-borne threats. These include Protocol Anomaly Detection (PAD), traffic rate monitoring, and network pattern matching, or signature-based detection. Each of these methods has strengths and weaknesses. Signature-based approaches can miss new attacks; protocol anomaly detection can miss attacks that are not considered anomalies; traffic anomaly detection misses single-shot or low-volume attacks; and behavioral anomaly detection misses attacks that are difficult to differentiate from normal behavior. Symantec Network Security combines multiple techniques and technologies into a single solution. In addition, it adapts to the changing threat landscape by adopting new techniques and technologies that improve upon or replace existing ones.