ZyXEL ZyWALL 2 Plus User Guide - Page 289
IPSec High Availability, Encryption and Authentication Algorithms
 |
View all ZyXEL ZyWALL 2 Plus manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 289 highlights
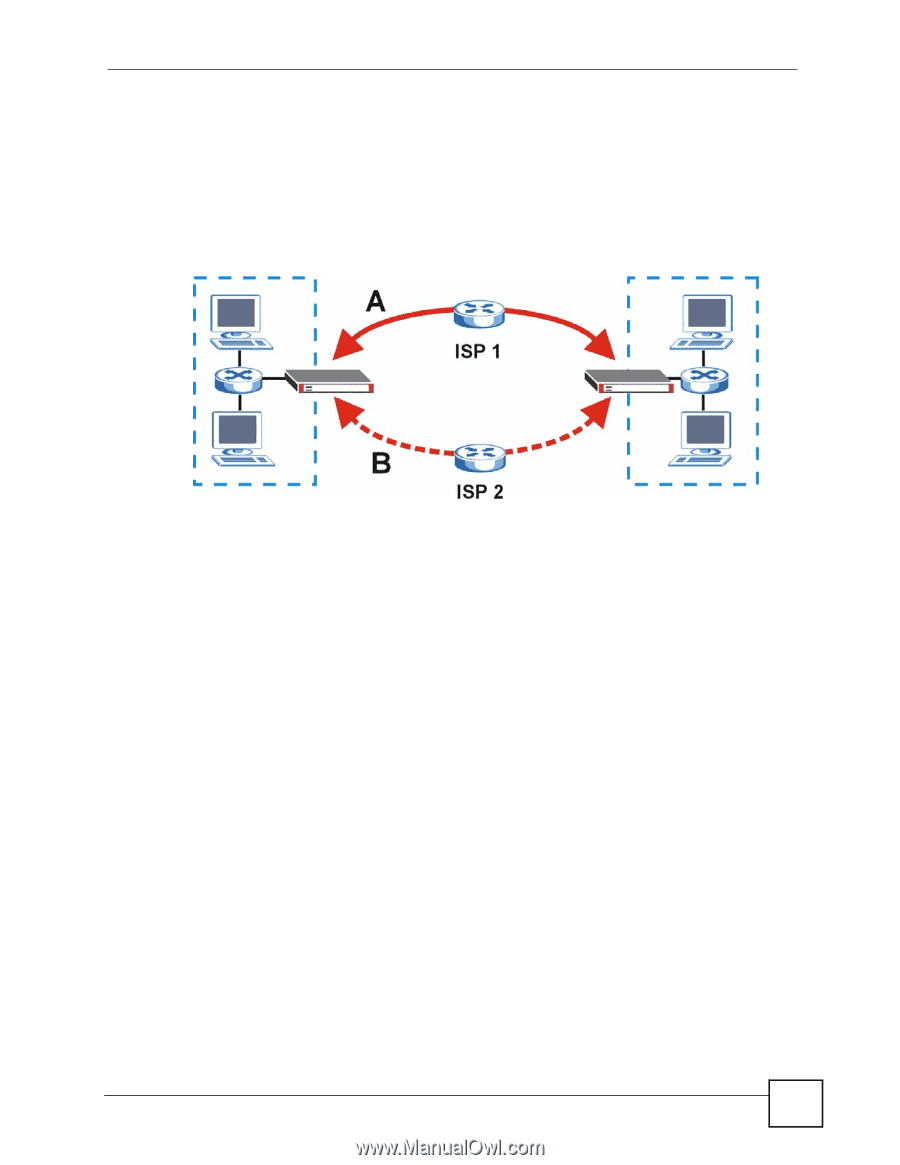
Chapter 14 IPSec VPN Screens IPSec High Availability IPSec high availability (also known as VPN high availability) allows you to use a redundant (backup) VPN connection to another WAN interface on the remote IPSec router if the primary (regular) VPN connection goes down. In the following figure, if the primary VPN tunnel (A) goes down, the ZyWALL uses the redundant VPN tunnel (B). Figure 191 IPSec High Availability When setting up an IPSec high availability VPN tunnel, the remote IPSec router: • Must have multiple WAN connections • Only needs one corresponding IPSec rule • Should only have IPSec high availability settings in its corresponding IPSec rule if your ZyWALL has multiple WAN connections • Should ideally identify itself by a domain name or dynamic domain name (it must otherwise have My Address set to 0.0.0.0) • Should use a WAN connectivity check to this ZyWALL's WAN IP address If the remote IPSec router is not a ZyWALL, you may also want to avoid setting the IPSec rule to nailed up. Encryption and Authentication Algorithms In most ZyWALLs, you can select one of the following encryption algorithms for each proposal. The encryption algorithms are listed here in order from weakest to strongest. • Data Encryption Standard (DES) is a widely used (but breakable) method of data encryption. It applies a 56-bit key to each 64-bit block of data. • Triple DES (3DES) is a variant of DES. It iterates three times with three separate keys, effectively tripling the strength of DES. • Advanced Encryption Standard (AES) is a newer method of data encryption that also uses a secret key. AES applies a 128-bit key to 128-bit blocks of data. It is faster than 3DES. Use the commands to have the AES encryption apply 192-bit or 256-bit keys to 128-bit blocks of data. You can select one of the following authentication algorithms for each proposal. The algorithms are listed here in order from weakest to strongest. ZyWALL 2 Plus User's Guide 289